Operations | Monitoring | ITSM | DevOps | Cloud
June 2021
6 Ways to Support a Remote DevOps Team
CircleCI Continuous Updates | Server 3.1
Foundations: What Is Dynamic Configuration?
Modern App Deployments: How to use NGINX and JFrog to Automate your Blue/Green deployments
The New Developer Experience at Okta
DevSecOps is a practice. Make it visible
Enable Multi-Site DevOps with Federated Repositories
Getting Started with Go and Cloudsmith
Securing pipelines through secret management
Secrets management plays a critical role in keeping your pipelines and applications secure. While secrets management tools help, you need to implement best practices and processes to successfully manage secrets in a DevOps environment. Standardizing, automating and integrating these processes also helps secure secrets by reducing the chance of human error.
Reducing microservice overhead with shared libraries
It’s a common story: the product team gets early success and grows into a large monolithic code base. While everything is in a single code base, features can be added quickly. This is partly due to the ability to leverage shared code across each feature in the codebase. When your team is adding a new feature, a developer can leverage the existing codebase for needs such as logging or special error handling.
We've Agreed to Acquire Vdoo, Unifying Developers and Security Teams from Source to Device
Docker Security Scanning
Top 5 Kubernetes Mistakes and How to Avoid Them
Understanding and tracking the impact of your ever-changing k8s deployments
Automating Your DevOps Automation
End-to-End DevOps for Containerized Applications with JFrog and Docker
3 ways to motivate your developer team with metrics
What DevOps means to devs
The Top 4 DevOps Headlines of 2025
The Biggest DevSecOps Hits From swampUP 2021
How to implement dynamic config using setup workflows
Drive DevSecOps Visibility with JFrog Partner Integrations
Share configuration across your organization: CircleCI private orbs
The Confident Commit | Episode 5: Software engineering with a purpose ft. Brad Henrickson
JFrog How To's - How to Set Up Xray to Scan Repositories, Builds or Bundles
How to Create Docker Images for ASP.NET Core
Microsoft has begun working with the Docker team and community so Docker can be used for the following: If you would like to run an ASP.NET Core web app in a Docker container and learn how to create images, we will explain all the steps on how to do the following: A Docker container image is a standalone, lightweight package that can be executed and contains all the requirements you need to run an application, such as: code, runtime, libraries, and settings.
How to set up a Private, Remote and Virtual Maven/Gradle Registry
JFrog Artifactory: Administration (2020+) - Course Sneak Peek
JFrog CloudFormation Modules Make Provisioning to AWS Easy and Secure
Jenkins Kubernetes Plugin: Running Agents In Other Clusters
At Moogsoft we use Jenkins to implement our CICD Pipelines. We run Jenkins where we run most everything else; Kubernetes, but you don’t need to have Jenkins running on Kubernetes to use this plugin. This is made possible by the community maintained Kubernetes plugin. Recently we had the need to not only run agents local to the same cluster that Jenkins runs in, but in other clusters across different regions.
Jenkins Kubernetes Plugin: Using the plugin in your pipelines
In our first post we went over setting up the Kubernetes Plugin. This described the basic setup of getting the plugin configured, and set with the proper perms to function. In this post we will go over how to leverage the plugin to generate agent pods. At Moogsoft most of our pipelines are scripted and are built inside of, or from parts of, Jenkins shared functions library we maintain.
JFrog Product Leaders Answer swampUP Attendees' Burning Questions
Artifactory DevOps Tool Overview - Online Course SNEAK PEEK
Developer, Transform Yourself: Digital Transformation Starts with You
Leaping Forward With Our Partners: JFrog Unveils Tech Partner Program
Continuously deploy Rust applications
Rust, a blazing fast and memory-efficient language, made its first appearance about ten years ago. Rust has gained a lot of momentum recently with the popularity of WebAssembly, a language that allows languages like C++, C, and Rust to run in web browsers. This enables developers to build highly performant applications and provide web apps with native functionalities that are not available on the web platform. In this tutorial, you will learn how to deploy a Rust application to a hosting platform.
Go Cloud-Native or Go Home
The movement away from on-premise and towards the Cloud is unstoppable. Even the US government is on board with their plans to “accelerate movement to secure cloud services, including Software as a Service (SaaS), Infrastructure as a Service (IaaS), and Platform as a Service (PaaS).” On-prem software is deployed, hosted, and maintained by your organization.
Continuously deploy custom images to an Azure container registry
The Azure container registry is Microsoft’s own hosting platform for Docker images. It is a private registry where you can store and manage private docker container images and other related artifacts. These images can then be pulled and run locally or used for container-based deployments to hosting platforms. In this tutorial, you will learn how to create a custom docker image and continuously deploy it to an Azure container registry.
Best Practices for Migrating to Helm v3 for the Enterprise
The Confident Commit | Episode 4: Systems and Flow with Elisabeth Hendrickson
Enterprise CI/CD Best Practices - Part 1
If you are trying to learn your way around Continuous Integration/Delivery/Deployment, you might notice that there are mostly two categories of resources: We believe that there is a gap between those two extremes. We are missing a proper guide that sits between those two categories by talking about best practices, but not in an abstract way.
Enterprise CI/CD Best Practices - Part 2
This is the second part in our “Enterprise CI/CD best practices” series. See also part 1 for for the previous part and part 3 for the next part. You can also download all 3 parts in a PDF ebook.
Enterprise CI/CD Best Practices - Part 3
This is the third and last part in our “Enterprise CI/CD best practices” series. See also part 1 and part 2 for the previous best practices. You can also download all 3 parts in a PDF ebook.
Completing the security testing automation cycle
DevOps, DevSecOps and CI/CD are synonymous with one word - automation. Automating their workflows gives developers the ability to deliver consistency, time savings, and useful insights into their software development life cycle (SDLC). But automation is only as efficient as your weakest link or most cumbersome bottleneck, which can sometimes be security testing. Security testing has traditionally been carried out either manually or quite late in the process.
DORA Metrics Explained
The Future Demands Full Stack DevOps Engineers at the Epicenter
SolarWinds and the Secure Software Supply Chain
In early 2020, threat actors breached the build systems of Solarwinds and used this access to add malicious code into one of SolarWinds products. The product, called “Orion”, is very widely used and deployed by tens of thousands of companies, including many Fortune 500 companies.
Automate and scale your CI/CD with CircleCI orbs
For the past two and a half years as a Solutions Engineer at CircleCI, I’ve had the distinct pleasure of working with some of CircleCI’s largest customers to help them instill healthy CI/CD practices into their development processes. Leading-edge organizations are trying to make sure that their applications are scalable, reliable, and secure. Shipping products to users quickly and reliably is imperative to gaining a competitive edge.
The startup founders' guide to software delivery
Software delivery on a team of 2 people is vastly different from software delivery on a team of 200. Over the growth of a startup, processes and tool choices will evolve naturally - but either optimizing too early or letting them evolve without a picture of where you’re headed can cost you in time and agility later. That’s why I want to talk to you about how to evolve your delivery process with purpose.
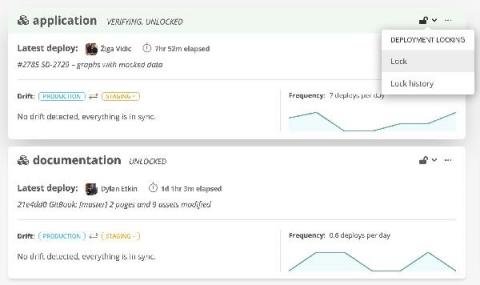
How Statuspage deploys continuously with Bitbucket and Sleuth
The Epicenter of the Developer Community: swampUP 2021
Bring your own CI/CD.
As a developer I couldn’t imagine working without one of these three things. For projects on GitHub the built-in actions should do the latter job fine in most cases. But as everything else they have limits. The more PRs, the more different tests per pull request and the longer those tests run, the longer different PRs have to wait for each other for the continuous integration to run.
How to build a team that demands metrics
When we talk about metrics in software delivery, a lot of developers think of execution metrics — things like throughput, delivery and number of deploys. But in reality, those metrics don’t motivate anyone — at least not without connecting them to a bigger picture. I’ve worked in software for 23 years. I’m a three-time founder and four-time CTO, responsible for leading a 200+ member distributed engineering organization.