Operations | Monitoring | ITSM | DevOps | Cloud
December 2023
CFEngine 2023 retrospective
As we bid farewell to 2023, it’s once again time to reflect on the milestones and progress we’ve made throughout the year. This year is especially significant because it marks 30 years since CFEngine’s birth. From its humble beginnings at the University of Oslo to the thousands of implementations across the world and counting, CFEngine has not only weathered the twists and turns of life, but has thrived in an industry where many have come and gone.
7 Common SSL Certificate Errors and How to Fix Them
No matter what industry you work in, your customers need to trust you. And, with 70% of internet users now taking various steps to protect their digital footprint online, your website must be secure. As online shoppers become more security-savvy and demand more from online services, an SSL certificate error has the power to lose valuable website visitors and ultimately reduce sales. Adopting SSL certificates is fast becoming the best practice for websites worldwide. Here's why.
CFEngine: The agent is in 32 - Fireside chat w/ Mike Weilgart
How to Choose the Ultimate Security Router: Guide
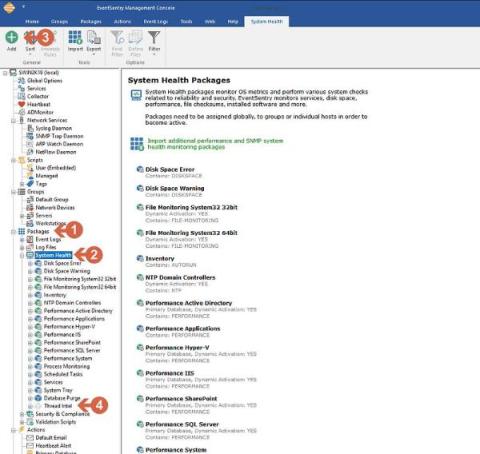
EventSentry Troubleshooting: Reducing the number of email notifications
Top 3 Office 365 Backup solutions for 2024
5 Best SIEM Tools and How to Choose
Cybersecurity has become something of great concern to the IT world over the last few years. The increase in remote working and the move to cloud-based and e-commerce solutions have opened up many new opportunities for cyber exploits and malware attacks. According to the FBI, the incidence of malware and network attacks, particularly ransomware, on both commercial and home systems has shown a major increase. At a corporate and personal level, ID theft has also increased greatly.
The Importance of a Secure Virtual Data Room for Safeguarding Confidential Information
Reasons to Implement Multi-CDN Strategy For Your Website
Predict the Future! A universal approach to detecting malicious PowerShell activity
So, here’s the deal with AntiVirus software these days: It’s mostly playing catch-up with super-fast athletes — the malware guys. Traditional AV software is like old-school detectives who need a picture (or, in this case, a ‘signature’) of the bad guys to know who they’re chasing. The trouble is, these malware creators are quite sneaky — constantly changing their look and creating new disguises faster than AntiVirus can keep up with their photos.
Standardization and Security: Ori Segall on Scaling Managed Services in 2024
Reasons to Switch to a More Reliable Internet Provider
What's new in Calico v3.27
Calico v3.27 is out 🎉 and there are a lot of new features, updates, and improvements that are packed into this release. Here is a breakdown of the most important changes.
What is the Importance of Quality Software for Your Business?
3 secure ways to handle user data in Raygun
Detecting PowerShell Exploitation
In today’s digital landscape, cybersecurity is a top priority for organizations. Hackers are continuously finding new ways to exploit vulnerabilities and compromise systems. PowerShell, a powerful scripting language and automation framework developed by Microsoft, has unfortunately become a favored tool among attackers due to its capability to run.NET code and execute dynamic code downloaded from another system (or the internet) and execute it in memory without ever touching disk.
Ubuntu Confidential VMs on Azure: Introducing Ephemeral OS disks & vTPMs
The rising trend of Data Breaches and Critical Vulnerabilities in 2023
As the year comes to an end, we are taking a look back on the major data breaches and vulnerabilities that disrupted the security of both small, and large and very important organizations around the world and across all industries. According to a recently published report: As this trend is on the rise, governmental organizations and companies of every size put more emphasis on the security of their systems and networks.
How MSPs and MSSPs can reduce risk and liability for their clients
For 83% of companies, a cyber incident is just a matter of time (IBM). And when it does happen, it will cost the organization millions, coming in at a global average of $4.35 million per breach. Add to that stringent data protection laws and the growing frequency and reach of ransomware and other sophisticated attacks.
The 5 Best Vanta Alternatives for Security Compliance
Over the last two to three years, we’ve seen increasing demands on all kinds of software companies to comply with security and compliance standards. More and more organizations are looking to benefit by moving their operations to the cloud, but this increases the potential for cybersecurity attacks and breaches. A new type of compliance vendor has emerged to help companies that must comply with the security standards designed to ward off cybersecurity threats.
Securing Your Smart Home: Tips For A Safe Connected Environment
Security Webinar: A Practical Guide to Deploying Zero Trust Network Access
How to Deploy Microsoft LAPS
Securing privileged accounts is of utmost concern to cybersecurity professionals, and Active Directory, Microsoft’s identity and access management service, forms the backbone of the majority of organizations. Active Directory (AD) centralizes user accounts, computers, and resources, ensuring access control, and local administrator accounts wield substantial power within Windows systems.
What is SSH?
The Importance of Detecting Fraud
We can't wait for SBOMs to be demanded by regulation
Old ads can be startling—cigarette ads used to boast their health-giving properties, sugar-laden candy was once advertised as a dietary aid, and soft drinks were advertised as a milk alternative for babies. None of this would fly today, of course, thanks to regulations. Foods must be advertised more responsibly, and they must list their ingredients clearly on the packaging, especially allergens.
What you can't do with Kubernetes network policies (unless you use Calico): Policies to all namespaces or pods
Continuing from my previous blog on the series, What you can’t do with Kubernetes network policies (unless you use Calico), this post will be focusing on use case number five — Default policies which are applied to all namespaces or pods.
How to securely query AWS S3 from ClickHouse
Importance of Hiding Your IP and Using SOCKS5 Proxy
The Role of Open Architecture in Creating a Unified Security Platform
The Three Ways of DevOps Governance
In this blog post, I take a look at modern IT governance by applying the classic “Three Ways” of DevOps principles originally introduced by Gene Kim in his seminal 2012 article. “We assert that the Three Ways describe the values and philosophies that frame the processes, procedures, practices of DevOps, as well as the prescriptive steps.” Here’s a quick reminder of the three ways set out by Gene: For Gene, all DevOps patterns can be derived from these three principles.
Security Webinar: Modernize Your Patch Management
Navigating the Global Cybersecurity Talent Shortage
Data Overload: Why Companies Collect Too Much Data and Pay the Price
In the US, a recurring news topic is the state of the federal budget – and if we’ll get one signed. Government budgets have hundreds of thousands of line items; each bickered over to gain or lose political capital with one group or another. However, most government budgets aren’t up for debate. Only about 30% of the US federal budget is discretionary or flexible. Nearly two-thirds, or 63%, is mandatory spending required due to prior commitments.
How to Detect Unauthorized Changes in Production with Kosli
Let’s not beat around the bush: change management is a prehistoric discipline desperately in need of fresh thinking. Its “best practices” are frankly terrible. Nobody honestly thinks manually filling out change tickets, waiting for CAB meetings and external approvals does anything to meaningly reduce risk. Change management is slow, inconsistent, doesn’t scale, and is prone to error.
How To Choose The Right Internet Provider For Your Business
What is a Kubernetes cluster mesh and what are the benefits?
Kubernetes is an excellent solution for building a flexible and scalable infrastructure to run dynamic workloads. However, as our cluster expands, we might face the inevitable situation of scaling and managing multiple clusters concurrently. This notion can introduce a lot of complexity for our day-to-day workload maintenance and adds difficulty to keep all our policies and services up to date in all environments.
A Look at How the Cloud Has Streamlined Financial Management
Backstage Developer Portal
Backstage, a development portal, allows developers to maintain constant vigilance over the health of their networks and services, no matter where they are deployed. This is invaluable to teams, as many different deployments across different environments need to be monitored to ensure security and compliance. Find out how to evaluate, implement, and succeed with Backstage in order to maintain your security perimeter and ensure that all deployments are working as intended.
How Automation Can Support Threat Vulnerability Management + Reduce the Attack Surface
CFEngine 3.23 released - Anniversary
Today, we are pleased to announce the release of CFEngine 3.23.0! This is a non-LTS (non-supported) release, where we introduce new features for users to test and give feedback on, allowing us to polish before the next LTS.(CFEngine 3.24 LTS is scheduled to release summer 2024). The codename for this release is anniversary, as this year is CFEngine’s 30th anniversary.
Sending Data to Elastic Security With Cribl Stream (And Making It Work With Elastic SIEM)
Cribl Stream is a real-time security and observability data processing pipeline that can be used to collect, transform, enrich, reduce, redact, and route data from a variety of sources to a variety of destinations. One of the popular destinations for Cribl users is Elastic SIEM. This blog post will walk you through the steps on how to set up Cribl Stream to normalize and forward data to use with Elastic Security for SIEM.