Operations | Monitoring | ITSM | DevOps | Cloud
February 2021
How to Identify the Zoom Data Center Location on AWS Infrastructure
Zoom leverage AWS’s global infrastructure, storage, content distribution, and security to deliver its service and store information securely in AWS data centers around the world. This means that when you’re looking to monitor your Zoom performance, it’s important to know how to identify which AWS data center location your Zoom application is using. Keep reading to find out how.
Small Business Network Management Bundle
11 Network Traffic Terms to Know
Windows network monitoring made easy with OpManager
Network administrators are responsible for the day-to-day operation of computer networks at organizations of any size and scale. Their primary duty is to manage, monitor, and keep a close watch on the network infrastructure to prevent and minimize downtime. Managing a network includes monitoring all the network components, including Windows devices. In any Windows network, the desktops, servers, virtual servers, and virtual machines (VMs), like Hyper-V, run on the Windows operating system.
All You Need To Know About Cloud Interconnection
Why Do You Need Network Performance Management Tools?
When your network goes down, revenue is lost exponentially. It is of utmost importance to keep track of your network automatically in order to fix problems before they occur, find the source of your problems as quickly as possible, and keep the user experience as smooth as possible.
Logging with the HAProxy Kubernetes Ingress Controller
The HAProxy Kubernetes Ingress Controller publishes two sets of logs: the ingress controller logs and the HAProxy access logs. After you install the HAProxy Kubernetes Ingress Controller, logging jumps to mind as one of the first features to configure. Logs will tell you whether the controller has started up correctly and which version of the controller you’re running, and they will assist in pinpointing any user experience issues.
How to Monitor Google Network Performance: Google Meet, Google Workspace, Gmail and Google Calendar
Application slowdowns, poor Internet speed, and laggy video calls are always frustrating. Whether you’re working in an office, or working from home, it’s important to keep an eye on the applications that matter most. In this article, we’re teaching you how to monitor the network performance of Google apps, including Google Meet, Google Workspace, Gmail & Google Calendar.
Hot Telecom Super CEO Faceoff
Key Strategies for Migrating to a New Network Monitoring Solution
What Are the Types of Network Devices?
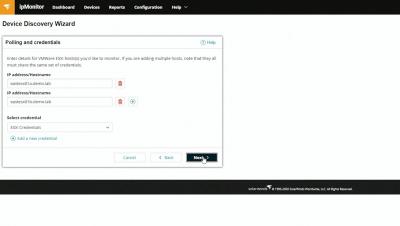
How to Monitor Your VMware Hosts Using ipMonitor
Layer 2 vs Layer 3 Network Switches: What's the Difference?
The what, why, and how of using network IP scanners in IP-centric IT infrastructures
A simple command-line interface (CLI) ping will give you details about your target IP address. However, you may have to input the ipconfig command, and then the arp-a command to fully discover the status of an IP, and this is just for one IP address. Now imagine doing this for an IP block of 300 IPs, or even 50 IPs, or doing the same task periodically to manage your IP pool of thousands of addresses and their metrics. Seems like an Herculean task for any network admin!
5 Things You Need To Know About Interconnection
Using HAProxy as an API Gateway, Part 4 [Metrics]
HAProxy publishes more than 100 metrics about the traffic flowing through it. When you use HAProxy as an API gateway, these give you insight into how clients are accessing your APIs. Several metrics come to mind as particularly useful, since they can help you determine whether you’re meeting your service-level objectives and can detect issues with your services early on. Let’s discuss several that might come in handy.
What Is Cloud Networking?
End-to-End Network Monitoring: Critical KPIs to Track
The IT network stays at the foundation of all the operations and data transfers within your business. Unreliable network or problems with the network performance may have a severe impact on your business. Running a business requires a robust and secure network, that managed effectively to meet all the necessary performance and security goals. The standard network monitoring is not enough in the digital transformation era.
How to Block an External Attack with FortiGate and Flowmon ADS
It’s a question we hear often - how to use Flowmon to block an attack? Flowmon is not an inline appliance to stand in the path of inbound traffic, so we partner with 3rd party vendors who supply equipment like firewalls or unified security gateways. In this post, I’m going to show you how to instruct Fortinet’s firewall FortiGate via Flowmon ADS to block traffic in response to a detected anomaly or attack.
What is Synthetic Monitoring and What Are the Benefits? | Obkio
Ribbon Defense Solutions - IP Optical and Cloud and Edge
Why CSPs Need to Shift Focus to Service Experience Monitoring
The past twelve months have pushed many communication service providers (CSPs) to the limit. According to financial reports of the last six months, the New Normal brought about by the pandemic has significantly increased network expansion efforts, IoT connections, new broadband customers, and out of bundle voice traffic and mobile data.
6 Best Network Traffic Monitor Software Options
Martello in Motion | Real User Monitoring & Network Visualization
As an industry-leading provider of the most comprehensive Microsoft 365 monitoring solution, Martello is in a class all its own; our digital experience monitoring solution features key capabilities that help IT teams identify when and where cloud application performance issues are happening and how to best mitigate the impact.
What Are Network Address Translation and Port Address Translation?
Problems You Can Solve With SolarWinds Tools
Scaling Up and Out With the Orion Platform
SolarWinds Service Desk Integration With the Orion Platform
What's New in SolarWinds Security Products
What's New in the SolarWinds Orion Platform 2020.2
How to Build Modern Dashboards in the Orion Platform
Monitoring Journey Live Q&A
Taking an API-First Approach to Network Management
What is MEF 3.0 and why it matters
ADS 11.2 - More than ordinary blacklists
Improve your security posture with community Indicators of Compromise and use reputation data to detect threats in encrypted traffic. On the digital battleground, it pays to stay on your toes, but there are ways to make the work easier. Flowmon ADS 11.2 brings you new and refined methods of avoiding known threats and learning from attacks carried out against others. Main news.
Troubleshooting microservices on K8S
Secure by Design | Our Plan for a Safer SolarWinds and Customer Community
Muse SDN Orchestration
Ribbon Rural Utility Solutions
Why is Network Topology Important for Your Business?
With more and more businesses depending on technology, networking can get more and more complex. Therefore, a network topology plan, which gives you a clear oversight of what’s at stake, will always be useful. But what are the benefits of having a topology system in place? How can it help a business with its performance management in real-time? There are a variety of network monitoring tools out there that practice a topological approach to support.
What Are the Benefits of Network Monitoring for Your Business?
In the modern age, all businesses rely on technology. Any company based in an office will depend on networking, too. But how can you be sure that your network is working hard enough for you? No matter the size or shape of your business, it pays to be careful. Without some form of monitoring solution, you, your team, and your revenue are at the mercy of your technology. For many companies, managed network monitoring solutions are essential. It is an industry that is worth $207 billion worldwide.
Your Guide to the Best Network Monitoring Tools
Monitoring your network is essential if you want to make sure you are protecting your productivity. However, knowing where to start is a challenge. That’s why there are multiple network monitoring tools available. But how do you necessarily know which are likely to work best for you? In this guide, we will look at some of the most popular network monitoring software available. We will also consider what each model does to help support network management in real-time.
What is Network Management?
Anyone with an office in the modern age will depend on a network of some kind. Whether you are a small enterprise or a larger company, you’re likely dependent on technology. But what happens when something goes wrong with that network? Do you know how to keep track of its different components and areas? Corporate networking can be complicated. However, managing it properly is vital to make sure that you are hitting your KPIs.
What Is Network Security?
Ribbon Research Reveals More than 100% increase in Interest in Deploying Microsoft Teams by Small Businesses
Operators and Service Providers' Lucrative 5G First-Mover Opportunity
The next-generation of mobile connectivity is rapidly bringing supercharged mobile gaming, Internet of Things technology, and a smarter, better-connected world to consumers’ fingertips. As 5G rapidly evolves and brings new possibilities, it presents a wealth of opportunities for mobile network operators (MNOs) to differentiate their services with high performance applications; and for wireline operators to deliver differentiated backhaul transport services, but they need to act quickly.
Why Cisco embraces Elastic for IT infrastructure transparency
This post is a recap of a presentation given at ElasticON 2020. Interested in seeing more talks like this? Check out the conference archive. Network infrastructure is the engine that drives a company’s business. As companies scale, assets that compose this infrastructure become more complex to manage. That means there’s more hardware, more software, and more subscriptions and services that require tracking.
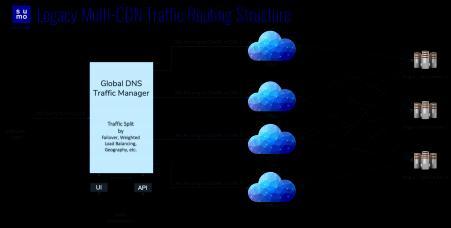
How to Dynamically Auto-Steer your Traffic to Multi-CDN or Multiple Data-Centers
11 Types of Networks: Understanding the Differences
Features to check for in a network scanner for enterprise networks
Network scanners have become an integral part of every IT admin’s first line of defense against security breaches. Using the right network scanner tool to conduct effective network reconnaissance and diagnosis enables you to pinpoint network issues that can escalate to security risks and network mishaps. A typical network scanner would allow you to scan a range of IP addresses sequentially, and display the active devices within that address block.
Six Enterprises Power the Uptime of the Cloud Era with HAProxy Enterprise
How to Map Domain Names to Backend Server Pools with HAProxy
Your HAProxy load balancer may only ever need to relay traffic for a single domain name, but HAProxy can handle two, ten, or even ten million routing rules without breaking a sweat.
Incident Communication Is a Key Part of Resolving Network Issues
HAProxy Monitoring (the InfluxDB Way)
My personal experience with HAProxy dates back to my work with a previous company, where we used HAProxy to do load balancing between pairs of servers with specific roles. Those servers are the core of the major payment gateway in Uruguay, where thousands of users use them every day to pay their bills, recharge their mobile phones, pay parking fees, and even play lottery numbers.
Flowmon 11.1 - A time-saver
High-level information and speedy configuration for the busy network administrator. If you want to respond to network issues quickly and promptly, you can’t waste time digging for information. So how can Flowmon 11.1 help?