Operations | Monitoring | ITSM | DevOps | Cloud
March 2021
Navigating the 5G Edge - Xhaul, Slicing and MEC
Bigleaf with Big Problems: Does It Have the Solutions?
Your business seeks a high-performance, flexible, cost-effective, and more secure alternative to Multiprotocol Label Switching (MPLS). Welcome to software-defined wide area networks (SD-WANs)! An improvement over legacy dedicated MPLS circuits, SD-WAN solutions deliver easily manageable networks with a high quality of service (QoS). Yet, your IT team tells you that SD-WANs aren’t cloud-optimized or mobile-device friendly.
Network monitoring with Hosted Graphite
Network monitoring is the process of looking after your network with the help of various tools and techniques. These tools that are often called network monitoring systems constantly track various aspects concerning your network, such as bandwidth usage, traffic, etc. This tracking is important in case of outages as these systems notify the network administrator immediately. Moreover, network monitoring systems are essential for status updates so that you can improve your system’s efficiency.
AppDynamics and ThousandEyes Extend Complete Visibility and Collaboration Across Your Entire Application Ecosystem
Say goodbye to silos and gain end-to-end application delivery chain visibility. It’s time to take back control with AppDynamics and ThousandEyes.
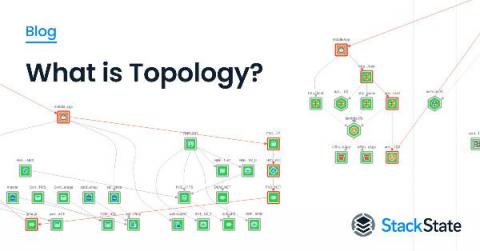
What Is Topology?
Topology is a multilayered map showing how everything in the IT environment is related. It's similar to Google Maps, which gives you a bird's eye view into an area and how everything is interconnected. Also, in Google Maps, you can see how traffic is flowing and which intersections may be causing bottlenecks. A view into topology allows similar visibility. You can see how components of an IT system are laid out to interact with each other.
10 Best Cisco Switch Monitoring Tools for 2021
Network monitoring is critical to ensuring a business stays secure. Switches are crucial to the proper functioning of that network. Hence, continue reading about the ten best Cisco switch monitoring tools. Switches connect networks and serve as controllers that let organizations share resources and talk to each other for better productivity. Without them, organizations face crippled information sharing and resource allocation, not to mention unnecessary costs.
Why Your Business Should Consider Private And Direct Connections To Google Cloud
How Eliminating Network Choke Points Can Help the DoD Plan for the Next Wave of the Pandemic
HAProxy Enterprise 2.3 and HAProxy 2.4 Support the Financial Information eXchange Protocol (FIX)
A floor of commotion bustling with people holding phones and shouting out purchase and sell orders, some using hand signals to communicate over the noise. This was a common scene on Wall Street in the 1980s. Nowadays, transactions happen at the push of a button with traders sitting directly in front of a computer. In fact, the computer has made it possible to automate the buying and selling of securities, leading to an era of high-frequency, algorithmic trading.
How to Increase Network Visibility with a Second Monitoring Session | Obkio
Auvik and TruMethods: Operational Excellence: Learn How to Be a World Class IT Service Provider
Best 7 Automated Network Diagram Software + Guide
What Is a Network Diagram?
In Pursuit of the Dark NOC: Transforming the Future of Network Operations with Automation & AIOps
How To Monitor Network Performance for Microsoft Teams, Office & Azure
Use Nmap for faster discovery in Cloud Migrations
When starting a cloud migration project, one of the most important and often challenging parts is to have an accurate understanding of what you are trying to migrate. Over time, companies start new projects, which means creating new infrastructure, adding servers, databases, etc. This is a normal part of the development cycle. However, despite best efforts, inventories get out of sync.
Pittsburgh Penguins Trade Up To High Availability with HAProxy Enterprise Load Balancer
The Importance of Network Documentation
Unraveling open port threats and enhancing security with port scanning tools
From exposing your network vulnerabilities to becoming a passageway for intruders, open ports can pose several risk vectors that threaten your network’s confidentiality, integrity, and availability. This is why it’s a best practice to close your open ports. To tackle the risks introduced by open ports, network admins rely on port scanning tools to identify, inspect, analyze, and close open ports in their networks.
SolarWinds Head Geeks to Discuss "Next Normal" Network Improvements Needed at Cisco Live! 2021
What Is the OSI Model?
10 Best Tools for Monitoring Wireless Access Points
Monitoring wireless access points is business-critical, allowing teams to facilitate day-to-day workflows. These wireless access points (APs or WAPs) provide strong Wi-Fi signals and transmission ranges for sending and receiving valued information. But wireless access points are susceptible to cyberattacks that jeopardize your revenue and reputation.
How to Monitor Network Traffic: Best Tips for IT Pros
What if I told you that monitoring network traffic is a lot less daunting than it actually seems? I think I have your attention. As a network has various moving parts, understanding it all can be a serious challenge. If something breaks or a component stops working correctly, implementing a quick troubleshooting process is essential. If you can't fix the issue right away, this could be detrimental for your end users, leading to more severe complications.
Cisco Network Monitoring: 6 Best Practices
It's often said that your network is the "backbone" of your IT infrastructure, underlying every other part of your enterprise IT. If your Cisco network infrastructure goes down or is experiencing performance issues, it's crucial that you have a real-time solution to identify and resolve the problem as soon as possible. But what does such a solution look like when it comes to Cisco networks?
Effortless Peering Across Europe With Console Connect
The 5G Fork in the Road for Network Transport (And Which Path to Take)
The hype of 5G is ushering in the potential for drastic network change and is driving service providers to prepare for the future. Today’s networks provide ubiquitous all-purpose IP connectivity to support all services.
Using HAProxy as an API Gateway, Part 6 [Security]
In almost every case, APIs have changed how modern applications connect to their data. Mobile apps, single-page web apps, IoT devices, integration hooks between software—all of these things rely on APIs to fetch, update, delete, and create data. In fact, one set of APIs might serve as the backbone of a website, mobile app, voice assistant device, and more, meaning one data store owns a treasure trove of information about us, the human users.
7 Best Network Infrastructure Mapping Tools
Secure by Design | Securing the Software Development Build Environment
Network Throughput vs Bandwidth and How to Measure It
How To Avoid Complex Pricing And Lengthy Contracts With Your Global Internet Access
Using HAProxy as an API Gateway, Part 5 [Monetization]
In our previous blog post, Using HAProxy as an API Gateway, Part 2 [Authentication], you learned that when you operate HAProxy as an API gateway, you can restrict access to your APIs to only clients that present a valid OAuth 2 access token. In this post, we take it a step further. You will learn how to leverage tokens to grant some users more access than others and then charge for the service.
Auvik and Cherwell Present: Processes for Managing Your Network
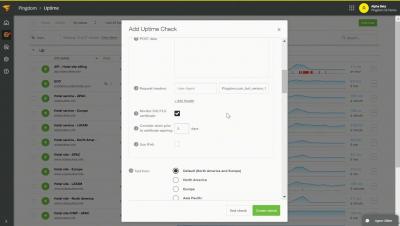
How to Monitor Amazon Chime Network Performance
With many of us now relying on video calls as a main form of communication, many different applications are growing in popularity, including Amazon Chime. To ensure you always have the best video and call quality during meetings, we’re teaching you how to monitor Amazon Chime network performance.
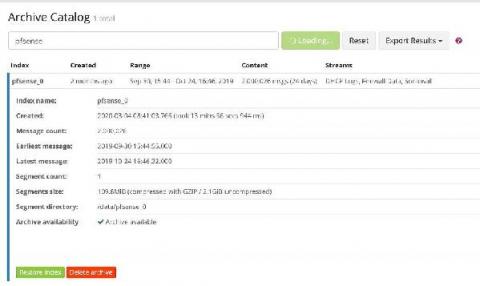
VPN and Firewall Log Management
The hybrid workforce is here to stay. With that in mind, you should start putting more robust cybersecurity controls in place to mitigate risk. Virtual private networks (VPNs) help secure data, but they are also challenging to bring into your log monitoring and management strategy. VPN and firewall log management gives real-time visibility into security risks. Many VPN and firewall log monitoring problems are similar to log management in general.
How to Reduce Bandwidth Consumption for Your Network?
Do you know who interacts with whom, when, and for how long and how frequently in your network? Network administrators must have clear visibility of bandwidth utilization using a robust bandwidth monitoring tool, to find out slow loading yet crucial connections, to plan out the capacity of network properly or to control the Quality of Service.
Securing Your DNS
Everything You Need To Know About Data Centre Interconnection
How to Draw Network Diagrams
How to Draw Network Diagrams
The HAProxy Enterprise WAF
The HAProxy Enterprise WAF with support for ModSecurity rulesets protects your web applications from sophisticated, Layer 7 threats left unhandled by network firewalls. Data breaches. Loss of consumer confidence. An endless cycle of companies being compromised. Not just fly-by-night, sketchy websites either. Large companies—companies that you’d think would do better—are being caught without reliable security measures in place.
Secure by Design | Getting Our Customers Back to Business
Using Thola for monitoring your network devices
Once upon a time there was a small company in the south west of Germany that used an old check plugin for monitoring its network devices. But as their network got bigger and bigger over time, the plugin (written in Perl) became more greedy than ever before and swallowed all of the available resources. The CPUs were melting and the RAM was about to collapse. So a small team of creative software developers decided to take the fate of their company into their own hands.
Best Practices for Monitoring Your End-User Experience - SolarWinds Lab Episode #94
5 Network Security Trends to Watch in 2021
It is not only the COVID-19 pandemic and the associated rise of remote work that is shaping the everyday routine of network security practitioners. Let's take a look at 5 major trends in network security.
Monitor Juniper network devices with Datadog
Juniper Networks provides a range of IT network and security devices, including routers, switches, access points, and firewalls. As you scale your on-prem infrastructure with potentially thousands of devices distributed across multiple locations, getting visibility into your entire network can easily become a pain point.
Cisco discusses benefits of VirtualWisdom with Cisco MDS 9000
5 Steps to Configure Cisco AnyConnect VPN
Ribbon Enterprise Session Border Controllers Certified with Twilio Elastic SIP Trunks to Deliver Direct Routing for Microsoft Teams
Never Discount the Power of Convenience
Whenever I look broadly at my career in telecom, one area that always amuses me is the extent to which our collective business enjoys its peculiarities. Sort of like our own secret handshake society full of unique terms and abbreviations like AIN & ANI, DDI and CLID or CLECs and POTS. After all, the Bell System used to formally publish a list of abbreviations and acronyms. Maybe it is just in our DNA?