Operations | Monitoring | ITSM | DevOps | Cloud
Incident Response
Incident response that's fast and cost-effective: Why 3 companies chose Grafana Cloud
When an incident occurs, every second counts. On-call staff need to quickly get all the relevant information in front of them in a way that’s easy to digest so they can more successfully investigate the issue and communicate with relevant stakeholders.
Incident response that's fast and cost-effective: Why these 3 companies chose Grafana Cloud
When an incident occurs, every second counts. On-call staff need to quickly get all the relevant information in front of them in a way that’s easy to digest so they can more successfully investigate the issue and communicate with relevant stakeholders.
What Is an Incident Response Team?
The vast number of threats lately lurking in cyberspace means that for cybersecurity teams, it's not a question of if an incident will occur but when. Whether it's a service outage, a data breach, a ransomware attack, or some other disturbance, organizations are bound to face security incidents eventually — the only question is if they're prepared.
Automated incident response in ITOps: Here's everything you need to know
If you’re like most IT leaders, you realize that automating repetitive, low-level incident response actions is key to unlocking enhanced workforce productivity, improved IT services, minimized downtime, better user experiences, cost savings, and the freedom to focus on innovation. Yet you don’t know where to start – or maybe aren’t sure of the best approach.
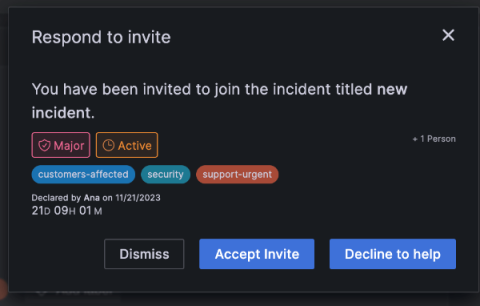
Easily page participants to accelerate incident response in Grafana IRM
Incidents almost never happen in a vacuum. When you receive an alert about a potential issue, odds are pretty good that you’ll need to navigate between different tools and teams to get things resolved. Of course, timing is critical in these situations, so the easier it is to communicate — between both tools and teams — the better off you’ll be.
Lessons in Incident Response I Learned While Waiting Tables
Before I stumbled into the tech industry (a story for another day), I spent several years in the customer service world as a server and front-of-house manager in restaurants. It was in these jobs that I first honed some critical skills that would later lead me on the path to incident response.