Operations | Monitoring | ITSM | DevOps | Cloud
October 2021
Splunking Netflow with Splunk Stream - Part 2: Basic Netflow Analytics
Hi there, I guess that if you are here, you've already read the first part of this series and want some help to quickly get value from your NetFlow data, building trend analysis and advanced analytics with long term data (i.e months), in addition to playing with real-time data. You can take advantage of Splunk’s super flexible schema on read architecture to exploit your real-time data from the very first moment you get the data in.
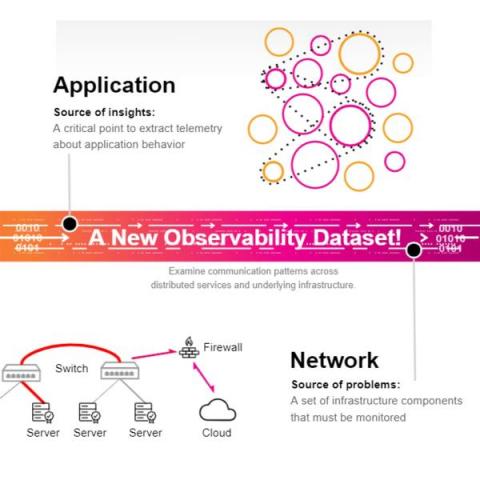
Having Trouble Getting the Right Insights From Your Cloud Network Monitoring? Preview Splunk NPM Today!
With cloud computing, containers, virtualization and the move to software-defined infrastructure, your cloud infrastructure monitoring is consistently evolving. New challenges can impact the reliability of business services where network performance is a significant subset. Your network is filled with a multitude of hosts, distributed services, and containers. It’s hard to monitor the health of these ephemeral cloud infrastructure components. How is their behavior affecting your applications?
VoIP Service Provider and Titanium 3CX Partner, Amplisys, uses Obkio to Monitor End-User Network Performance
Learn how Obkio works with 3CX partner and VoIP Provider, Amplisys, to create a streamlined network monitoring and troubleshooting process to quickly and proactively support every one of Amplisys’ VoIP customers for impeccable customer satisfaction and support.
Scale Testing the Network Control Plane | Anubhav Mishra (HashiCorp)
Observability for Service Organizations | Bart Scheltinga (RawWorks)
Feature Highlight: Application Private Networks
An Application Private Network (APN) is a private, encrypted network running in parallel with your standard network - essentially a VPN for your application.
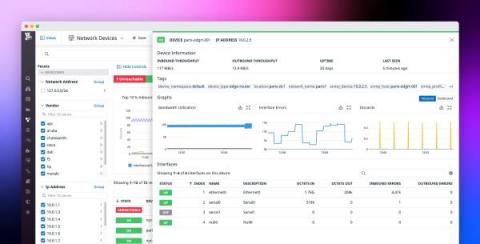
Introducing Network Device Monitoring
For many organizations, the success of their business depends on their ability to maintain on-prem or hybrid infrastructure. For instance, some companies rely on data centers for security reasons or to support their large, static workloads, while others must execute their critical business processes as close to the edge as possible to ensure minimal latency.
Dakota Central Deploys Ribbon IP Optical Solutions for Faster Broadband Speeds and Increased Network Reliability
Guide To AWS Load Balancers
The AWS Elastic Load Balancing (ELB) automatically distributes your incoming application traffic across multiple targets, such as EC2 instances, containers, and IP addresses, in one or more Availability Zones, ultimately increasing the availability and fault tolerance of your applications. In other words, ELB, as its name implies, is responsible for distributing frontend traffic to backend servers in a balanced manner.
Cloud 66 Feature Highlight: Application Private Networks (APN)
Untangling Business In The ISP Industry With Elliot Noss | Network AF Episode 4
Network AF, Episode 4: Untangling business in the ISP industry with Elliot Noss
Today on the episode 4 of the Network AF podcast, host Avi Freedman welcomes his longtime friend Elliot Noss. For 25 years, Elliot has been the CEO of Tucows, the internet services company with the second-largest domain registrar in the world. Elliot is considered an outlier in the ISP industry, largely due to his transparency and for the stellar customer experiences he encourages through Tucows.
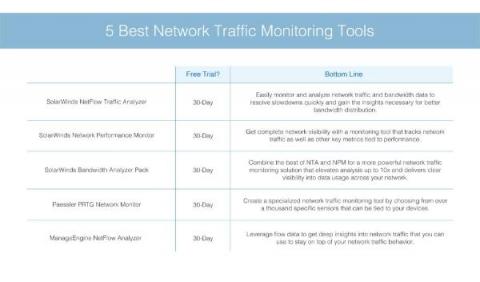
5 Best Network Traffic Monitoring Tools
Robin.io and AirHop Announce Strategic Partnership to Modernize Open RAN Solutions for 4G/5G Networks
Kubernetes Networking: CNI & Network Policies | Kublr Webinar
Adopting A Network-as-a-Service Model
DNS filtering: What is it and why do companies use it?
The Domain Name System (DNS) makes it possible for users to access websites using domain names, like wikipedia.org, in place of nine-digit IP addresses. Due to its ubiquitous nature, DNS can be used to block access to selected websites, which is commonly known as DNS filtering. Many companies see security and productivity benefits from implementing this strategy where appropriate. Read on as we explore some of the key details around how DNS filtering works and how it can be beneficial.
Better, Not Just More, is the True Network Goal
In modern communications networks the demand for more speed and more capacity to drive ever more advanced services has been at the heart of network development – especially in the mobile space. Even the generational numbers hint at the increases – 3G, 4G, 5G - every change indicating an increase, every change indicating something that is somehow bigger and better. And, of course, the impression created is largely correct.
NPM, encryption, and the challenges ahead: Part 2
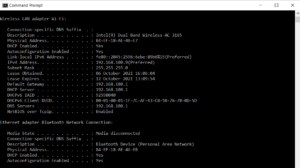
In part 1 of this series, I talked a bit about how encryption is shaping network performance monitoring (NPM). Let’s dive in deeper now… Most NetOps and DevOps professionals today hear complaints about network performance when employees work from home. Unless the complaint is coming from all remote users of an application, individuals suffering from slowness are on their own to figure out how to optimize connection speeds.
Who is Ribbon
SolarWinds Gives Data Pros the Tools for DataOps Success With Database Mapper and Task Factory
Australia (Oceania): Have You Checked Your DNS Performance Lately?
Any organization with an online presence understands the importance of its website. That’s why companies invest thousands of dollars in design, user interface (UI) development, and site optimization. But that’s only part of the puzzle. Your website or online application can have all the bells and whistles, but if you aren’t fully optimizing your DNS, you’re losing money—plain and simple.
Web Performance of the World's Top 50 Blogs
Top SysAdmin Tools (That Aren't Software!)
How We Automated One Of The World's Largest High-Performance Networks
Announcing HAProxy Data Plane API 2.4
Version 2.4 improves its e2e tests, revamps how logging in the HAProxy Data Plane API works, adds support for namespace filtering in Consul Service Discovery, improves runtime capabilities for maps and ACLs, adds server-template support and adds log_targets to global and defaults sections.
ManageEngine captures top honors at GovTech Innovation Awards 2021
ManageEngine captured the Network Management & Monitoring Vendor of the Year honor at the GovTech Innovation Awards 2021 conducted by Tahawul Tech. Elitser Technologies, a regional distributor for ManageEngine, accepted the award on behalf of ManageEngine on September 27 in Dubai, UAE.
Network AF, Episode 3: Uniting networking pros with Salesforce's Janine Malcolm
If you’ve ever thought networking is bewildering as a newcomer, you’re not alone. In episode 3 of Network AF, meet Janine Malcolm, the director of network engineering at Salesforce. She joins podcast host Avi Freedman to chat about some of the experiences she’s had throughout her career and how to make network engineering a more accessible profession. At Salesforce, Janine is currently focused on uniting groups of people as one overall network engineering team.
Ribbon Employees Mark Global Day of Service with Volunteer Activities Around the World
Network monitoring tools: The good, the bad, and the ugly
For organizations that rely on their network to support their daily operations, how well the network operates can make or break their business. As a network admin, your core objective is to ensure that day-to-day business operations are carried out successfully. This involves optimizing the network for maximum performance and minimizing service disruptions.
NPM, encryption, and the challenges ahead: Part 1 of 2
It’s interesting to observe how encryption and network performance monitoring (NPM) have evolved over time. When I first entered the networking industry right out of college, many applications sent passwords over the network in clear text, unencrypted. Since just about everyone’s PC was wired back to a repeater (i.e., not a switch), we could observe each other’s traffic with free packet analyzers and laugh.
Event and Log Management for Optimized Security and Performance
Welcoming Newcomers to the Networking Industry with Janine Malcolm | Network AF Podcast Ep. 3
6 All Too Common Network Security Hacks Your Team Should Know About
Network monitor 101: All about network monitors
With the increase in the number of organizations that have a sizable network infrastructure, the need for a network monitor also increases substantially. With properly established network monitoring protocols in place, organizations can work more efficiently, have more visibility over their network devices, and avoid unexpected downtimes and network issues.
New Trends In Network-As-A-Service
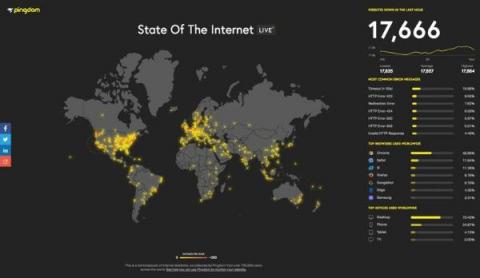
How To Monitor Network Traffic
In today’s digital world, almost every business is driven by technology, whether big or small. With the advancement of technology, the associated threats to the security of the IT infrastructure come hand in hand. Therefore, businesses need network traffic analysis tools to keep an eye on their network. Monitoring network traffic continuously gives a business the insight to optimize and manage performance, minimize attack surfaces, intensify security, and better manage its resources.
Network AF, Episode 2: Backbone engineering and interconnection with Nina Bargisen
In episode 2 of Network AF, meet Nina Bargisen. Nina has spent over two decades in network engineering and talks to podcast host Avi Freedman about her history in interconnection and peering. She’s worked for companies like Netflix and TDC (formerly Tele Danmark Communications). Now Nina is Kentik’s director of GTM strategy focused on supporting service providers. Nina joins Avi on the Network AF podcast to discuss: Nina’s entry into networking was non-standard.
Data centre networking: SDN fundamentals
This blog post is part of our data centre networking series.
Announcing HAProxy Kubernetes Ingress Controller 1.7
We’re proud to announce the release of version 1.7 of the HAProxy Kubernetes Ingress Controller! In this release, we added support for custom resource definitions that cover most of the configuration settings. Definitions are available for the global, defaults and backend sections of the configuration. This promotes a cleaner separation of concerns between the different groups of settings and strengthens validation of those settings.
How Monitor Google Cloud Interconnect & Network Performance | Obkio
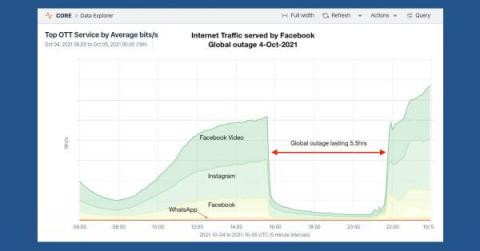
Facebook Outage Underscores Risks of Modern SDN Networks
On October 4, 2021, an outage took Facebook, WhatsApp, and Instagram down for six hours. This major outage is a powerful and high-profile example of the difficulties facing those tasked with managing modern network architectures.
Data centre networking: what is SDN?
The recent contexts have shown that enterprises needed to take a different approach regarding their digital transformation and its prioritisation. They’ve experienced the need to run new configurations and operations remotely on their infrastructure. This quickly showed the benefits of automation solutions to run those changes from few central locations, which highly facilitated the task of systems and network admins.
Ribbon's Professional Services Capabilities Enable Service Providers to Quickly Offer Microsoft Operator Connect for Microsoft Teams
Modernizing Network Operations: How to Check All the Boxes
Optimize Your Network Bandwidth With Detailed Traffic Analysis
Facebook's historic outage, explained
Yesterday the world’s largest social media platform suffered a global outage of all of its services for nearly six hours during which time, Facebook and its subsidiaries, including WhatsApp, Instagram and Oculus, were unavailable.
20 KPIs Your MSP Should be Tracking (Webinar)
Network-As-A-Service And The Cloud
HAProxy Kubernetes Ingress Controller Reaches 10 Million Community Downloads
It’s almost wild how two years have passed already since we first announced the HAProxy Ingress Controller for Kubernetes. Note that this project is different from the jcmoraisjr/haproxy-ingress HAProxy ingress controller project on GitHub. Our project is also an open-source project, but it is overseen by engineers at HAProxy Technologies, which has allowed us to streamline its release cycle.
Your RTC Services Are Better Off When They Are Cloud Native
SBC Interoperability: How Do I know if This Works with That?
Growing up, I was the youngest member of my family, so I was not very fond of the game “Keep Away” that my older brothers liked to play. The idea of the game (it has a few different names) is that two people toss a ball back and forth while the third person stands in the middle and tries to intercept it. Being the youngest, and therefore the smallest, it often seemed like a futile game that wasn’t much fun.
Deploy the RESTMon Microservice in Minutes
Within any enterprise, IT operations teams use a variety of solutions to monitor their technology ecosystem. These products are often business critical and cannot easily be replaced or migrated. Ultimately, it’s important that teams can analyze and correlate data from these different tools so they can produce the insights they need to improve decision making. To help address these requirements, Broadcom offers RESTMon.
Incident Review - Slack Outage Impacts A Subset Of Users Worldwide Due To DNS Issue
DNS observability is an essential part of any Ops team’s strategy. Looking for proof? It’s happening right now. It has been a busy week for Ops teams across the globe. Many were forced to urgently rotate SSL certificates after one of Lets Encrypt’s root certificates expired. Collaboration plays a critical role during such situations where members in a team or multiple teams must communicate and work with each other to rapidly and efficiently complete a collective task.