Operations | Monitoring | ITSM | DevOps | Cloud
September 2022
SBOMs The New Standard in Supply Chain Security - DevOpsCon NY 2022
JFrog's Newest Board Member Shares Her Thoughts on DevOps, Security & IoT
Securing Terraform Modules with tfsec
Infrastructure as Code (IaC) patterns have enabled velocity, repeatability, and codification of best practices for our environments. However, using IaC has introduced new challenges, especially around security. Securing manually deployed infrastructure is already difficult. This problem rapidly multiplies when organizations adopt IaC patterns, since they must now contend with the complexity of code and the proliferation of environments enabled by this increased velocity.
October is National Cybersecurity Awareness Month
It’s National Cybersecurity Awareness Month, and as a Cybersecurity Awareness Month Champion Organization, xMatters is proud to be actively participating. Since the National Cybersecurity Alliance started this initiative in 2004, the number of devices connected to the internet and the amount of time we spend interacting online has increased exponentially. The impact on our lives is so massive that it’s become hard to imagine what life would be like without our devices.
What is new in Calico v3.24
A couple of weeks ago, TIgera engineers released the new version of Calico, as part of a community effort to drive cloud security and networking even further. But before I begin diving into the details of this new release, I want to first spotlight a few of our community members who have merged their contributions to Calico Open Source for the first time.
Webinar recap: A NetOps guide to DDoS defense
We recently broadcast a webinar to discuss DDoS trends and developments. Our partner Cloudflare had their cybersecurity evangelist, Ameet Naik, join us along with our own Doug Madory, head of internet analysis. I had the pleasure of moderating the discussion.
Installation Guide: Aqua Security on DKP
Mind the Overspray - Password Spraying Remains a Major Threat
If you’re wondering if that classic car you’ve been scoping out on Bring a Trailer or eBay Motors is as authentic as posited by the seller – specifically re: the common claims of “original paint” or “high quality respray” – you’re going to want to take a closer look around the edges. This is because a talented painter can make a second or 30th-hand vehicle look pretty snazzy with a well-affected, if not super high-quality, repaint.
A Smart Home System That Does Not Rely On a Cloud
Internal Social Media Platforms and Risk Management
What's the Sharpest Tool in Your Security Shed?
How easy is it to work with your security tools? So easy that you’re telling all your family and friends and you singing their praises from the occasional rooftop? Well, we sure hope so. Security tools, like any other tool, should help you save time, not waste it. Nobody would have invented a drill if screwdrivers were fast enough — but it’s also up to you to make sure you are using your drill and all the other power tools available in the modern world.
How a telecom company elevated integrated risk management and security
Managing risk and compliance in telecommunications is no easy feat. When a telecom company operates in underserved remote and rural communities—including hurricane-prone island markets and mountainous regions in the southwestern US—it can be even trickier. That’s where communications services company ATN International, based in Massachusetts, found itself. The company wanted a platform to elevate its integrated risk management (IRM) program.
A NetOps Guide to DDoS Defense
Increased security for Enterprise and Elite
As a Platform.sh customer, your protection is paramount and every single one of your projects is secure. For Enterprise and Elite customer projects we go the extra mile and offer a rich selection of enhanced security features, which can be used right now. Let’s dig into each of them.
What is CyberArk?
How Wiz and Torq Combine to Mitigate Existential Cloud Security Threats
A single cloud security incident can stop an enterprise in its tracks, sometimes resulting in irreparable damage to its operation, reputation, and customer loyalty. One key strategy for preventing such incidents is combining complementary cybersecurity tools to defeat threats at scale. A coherent Cyber Security Incident Response Planning (CSIRP) approach requires enterprises to select and integrate the right tools before a security incident occurs.
Take Network Monitoring to the Extreme with WhatsUp Gold/Flowmon Duo
Network monitoring is the key to efficient, reliable operation, as well as performance and security. The deeper and more broadly you can monitor (yes, you want to do both), the better your network operates. What if you could combine a superstar in network infrastructure monitoring with the champion of network flow monitoring? You can. Progress, owner of WhatsUp Gold, recently acquired Kemp and their market-leading Flowmon solution.
Is Your Mac Spying On You? Maybe It Should be
What would you call software installed on your Mac, that’s hidden from sight, difficult to remove, and that silently monitors everything that happens on the system? You might call it spyware, or a RAT (Remote Access Trojan), and start thinking about how best to get rid of it. However, that same description can also be applied to the software that’s used to keep your machine safe from such threats.
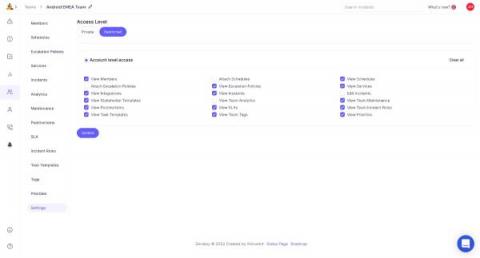
Coming Soon - Role based access control(RBAC) on Zenduty
Over the last few quarters a couple of interesting patterns have emerged amongst our larger customers who are looking to catalyze cross-team collaboration during a major incident spanning members from multiple teams.
How to Manage Your Vulnerability Workflows with Cloudsmith
Scan your packages for vulnerabilities and never miss new vulnerabilities as they get discovered. Create actionable workflows by quarantining packages over defined vulnerability levels.
Five security-first approaches to delivering better application experiences
Five ways to align security, collaboration and business outcomes to drive world-class, secure applications experiences.
How Nonprofits Can Protect Users' Safety Online
Security at Warp Speed - Staying Ahead of Threats with DomainTools and Torq
Understanding Kubernetes Evicted Pods
What does it mean that Kubernetes Pods are evicted? They are terminated, usually the result of not having enough resources. But why does this happen? Eviction is a process where a Pod assigned to a Node is asked for termination. One of the most common cases in Kubernetes is Preemption, where in order to schedule a new Pod in a Node with limited resources, another Pod needs to be terminated to leave resources to the first one.
Spot PC security and compliance
Monitoring CrowdSec with Bleemeo
CrowdSec is an open-source software that allows you to detect peers with malicious behaviors and block them from accessing your systems. It benefits from a global community-wide IP reputation database. Attckers can then be prevented from accessing your resources by deploying bouncers. They are in charge of acting upon actors that triggered alerts: they can block the attacking IP, serve a 403 Forbidden response, and much more.
Ransomware: Latest Variants and Trends on the Rise
Here in this blog, we will talk about some of the emerging ransomware you should know about and how you can prevent such attacks.
Reasons Why IT Support is Important
Benefits of Distributed Computing Systems to the Modern-Day Tech Businesses
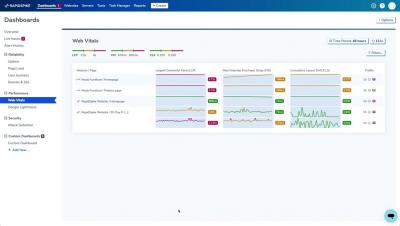
RapidSpike Platform Introduction
Torq Delivers on the Promise of Parallel Execution
Security operations professionals are constantly being pushed to the edge of their capacities. They’re dealing with endless manual processes and managing tasks sequentially, because of the limitations of their security tools and options. They’ve dreamed of being able to execute more tasks simultaneously to quickly enrich, analyze, contain, and resolve security threats. Today, Torq is proud to introduce Parallel Execution, which makes those capabilities a reality.
Making Resilience Decisions Post Pandemic with Jay Sartori
Making Resilience Decisions Post Pandemic with Jeremy Capell
InvGate Obtains SOC 2 Certification: What it Means for You
Cybersecurity Insurance Trends: Key Takeaways for MSPs
The increasing frequency and severity of ransomware attacks are driving significant changes in the cyber insurance market. The May 2021 attack on Colonial Pipeline Co. showed—or rather, confirmed—just how vicious and financially damaging these events can be. Unsurprisingly, cyber security insurers are taking steps to limit their exposure to losses from cyberattacks.
Torq Introduces Parallel Execution
Using automation to deliver reliable managed security services
As a Cloud Service Provider (CSP), Managed Service Provider (MSP), or Managed Security Service Provider (MSSP) you are instrumental in delivering effective and reliable managed security services to your clients. With cybercriminals taking advantage of less secure environments and becoming more advanced with their security breaches, this is becoming increasingly complex.
IT Monitoring for Government
Today’s blog comes from Kevin Howell, CEO of UK partner – Howell Technology Group (HTG) about their work supplying secure cloud technologies and remote working solutions to government and regulated customers. HTG are a trusted industry leader in the UK, who offer virtual desktops, managed services and efficient modern workplace solutions. Their solutions are also available with the UK Government’s Digital Market place under the G-Cloud Framework.
Debunking Myths About Cyberattack Complexity in 2022
Stoking fears about the threat landscape is a popular approach, and one that I don’t particularly care for. Many will tell you that the threat landscape is constantly changing, that threats are getting more complex, and that actors are getting more sophisticated. “The whole world is getting more difficult and scarier, so buy our stuff!” There’s a ton of media sensationalism too, with the popular image of the hacker sitting at a computer, wearing a dark hoodie.
Securing the DX NetOps Development Lifecycle with DevSecOps
Recent, high-profile cybersecurity exploits, such as Sun Burst and Log4j, demonstrate that every enterprise is only a stone’s throw from a software vulnerability. This becomes especially critical when security is breached in a network monitoring component that has privileged access to core enterprise systems. In the case of Sun Burst, a well-known monitoring software provider made international headlines.
Ivanti Announces Lookout CASB/SWG Partnership for Ivanti Neurons for Zero Trust Access
Ivanti is proud to have partnered with Lookout, Inc to provide zero trust secure access across highly distributed application ecosystems while protecting their users, their data and their devices from accidental and malicious data exfiltration and threats. Today we are proud to announce the general availability of Lookout CASB and Lookout SWG as an add-on to Ivanti Neurons for Zero Trust Access (ZTA).
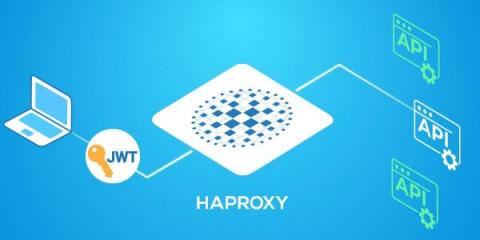
Verify OAuth JWT tokens with HAProxy
With HTTP REST APIs serving as the backbone of modern web applications, securing those APIs presents a critical challenge for organizations. APIs are typically designed to be discoverable, self-documenting, and easily consumed by a range of programming languages, and that makes them appetizing for hackers.
Cybersecurity Companies Have A Customer Profitability Problem - Here's Why
Data Protection Methods for IT & MSP Teams
The two words that IT and MSP teams never want to hear are “data loss.” According to Business Partner Magazine’s article on data backup, “94% of companies that fail to recover from a major data loss do not survive, and 43% of companies never resume their operation after a major data loss event.” To prevent these disasters from occurring, IT & MSP teams rely on data protection.
Everbridge Signal - Open Source Threat Intelligence to Keep People Safe and Operations Running
Top 5 Reasons Why Splunk Is the Ideal Platform for Unified Security and Observability
Splunk embodies the top 5 principles of unified security and observability, and has been an expert in log management, security, and observability for years.
Mobile app security testing: tools and best practices
To minimize the security risks of an application, developers need their apps to stand up to stringent security testing. Fortunately, there are tools available that simplify and even automate these security tests. There are also best practices to guide and inform the testing process. In this article, I will cover the most common security issues for mobile apps and highlight popular security tests.
IBM Patches Severe Vulnerabilities in MQ Messaging Middleware
IBM this week announced patches for high-severity vulnerabilities in IBM MQ, warning that attackers could exploit them to bypass security restrictions or access sensitive information. Messaging and queuing middleware, IBM MQ provides enterprise-grade messaging between applications, enabling the transfer of data between programs and the sending of messages to multiple subscribers. Two security issues were resolved in IBM MQ this week, both residing within the libcurl library.
Prevent long IT security workdays through collaboration
From surprise zero-day vulnerabilities to new exploits surfacing in the wild, few things ruin an IT security analyst’s after-hours or vacation plans faster than having to work overtime because of a cyberattack. Here’s a glimpse into how the story usually goes at most companies: A horribly bad cybersecurity day The first cup of morning coffee or tea is on your desk.
A Primer on SASE: What It Is, Why You Should Care, and How OpsRamp Can Help
As more workloads move to the cloud, more employees work remotely and SaaS application adoption increases, enterprises have had to rethink the way they secure access to the IT services their employees need. The reality for most enterprises today is a multi-vendor, siloed approach that has only compounded their security and IT operations management headaches as they end up using multiple management tools to secure and govern their access to cloud services.
Microsoft's Coordinated Disclosure Discussion from BlackHat & DefCon '22
5 Reasons Why Open Source Remains A Good Software Option
3 ways to implement Zero Trust in a legacy environment
Trust is a very fickle partner to rely on in the IT sector primarily due to the incessant barrage of security threats from both external and internal actors. This is why government, enterprise, and other types of organizations hold cybersecurity as a top priority as hackers discover ever more ingenious ways to stay under the radar.
SecurityDAM's NOC Management Takes Off With MoovingON.ai Platform
When SecurityDAM (acquired by Radware), a DDoS protection service provider, needed to upgrade their NOC operations, they tested out multiple solutions before choosing MoovingON.ai. From increasing efficiency and visibility to improving ticket resolution times and runbook automation, MoovingON.ai provided the NOC manager and team with everything they needed to run operations more smoothly and effectively.
Three New Standards Compound Security Engineering Challenges
A recent ESG/ISSA survey highlighted that security professionals are overwhelmed with competing proprietary data standards and integration challenges. Today’s security landscape often comprises dozens of tools, each with its own unique format. Even if the format is defined and widely adopted, like Syslog, implementations vary widely from tool to tool, or even from release to release for the same tool. How big of a problem are these differing data formats?
Debunking the Myth of XDR
One of the biggest buzzwords (or really, buzz acronyms) to pop up in the cybersecurity space in recent years is XDR, or, extended detection and response. The term was coined in 2018 by Nir Zuk, CTO and co-founder of Palo Alto Networks. It was posited as a new way to think about security, where data is taken from several platforms and it gets correlated and analyzed.
5 Questions to Ask When Developing an Automation Strategy
Automation is like running a marathon. It sounds like a great and noble pursuit until you actually go out and start pursuing it. At that point, it's easy to fail if you don't prepare yourself ahead of time for the challenges that are inherent to the process. Indeed, although automation can provide a number of awesome benefits, whether you actually reap those benefits depends on how easy it is to implement and manage automation tools. And, as many teams discover, doing these things may be harder than it often seems.
How to Prevent Ransomware? A Quick Guide to Protect Your Company Data
What is a Security Operation Center and how do SOC teams work?
5 Best Practices of Network Security Monitoring
According to Accenture’s “State of Cybersecurity Resilience 2021” report, security attacks have increased 31% from 2021 to 2022. This statistic shows that organizations are not ready with a robust security plan and lack continuous network monitoring, resulting in security loopholes. Efficient network infrastructure is crucial for the success of your enterprise.
FIPS Certified vs FIPS Compliant #security #fips #development
Everbridge Signal - Open Source Threat Intelligence to Keep People Safe and Operations Running
What is Firewall as a Service (FWaaS)?
You wouldn’t let just anyone enter your home, and your network should be no different. Here’s how Firewall as a Service (FWaaS) acts as your cloud infrastructure’s own security guard for better data protection.