Operations | Monitoring | ITSM | DevOps | Cloud
March 2023
Protect your enterprise with AI-powered anomaly detection
Building a Distributed Security Team With Cjapi's James Curtis
CFEngine: The agent is in 23 - Detecting previously hidden malware with Invary & CFEngine
Cyber Resilience: The Key to Security in an Unpredictable World
This live stream is a conversation between Ed Bailey and Jackie McGuire on the growing significance of cyber resilience in today’s digital landscape. You’ll learn what cyber resilience means, why it’s important, and how to manage and improve it in an increasingly unpredictable world. With cyber threats becoming more sophisticated and frequent, cyber resilience has become critical to protecting personal and business assets.
Dealing with Unknown Threats
The cybersecurity threat landscape facing every organization is constantly changing. Cybercriminals are always looking for new vulnerabilities to exploit or changing existing attack methods to bypass protections. They also go to great lengths to hide their activities within regular network traffic and application activity. The attack surface that organizations present to attackers is also in a constant state of flux.
The Balancing Act of Staying Secure While Working From Home | Ivanti Security Insights Podcast: Ep.4
Three Tech Options To Turbo-Charge Your New Construction Company
7 Ways to Prevent Network Security Breaches in the Workplace
Network security breaches are every business’s nightmare. A security breach could be anything from password attacks with further unauthorized system access to data leakage. Whether it is a small start-up or a large enterprise with millions of dollars in turnover, a single network security breach can be detrimental to the reputation of any company, not to mention the financial losses incurred. According to the 2021 Thales Data Threat Report, 45% of US companies suffered a data breach in 2020.
Why is EDR Important? A Business Case for MSPs
The security industry may not have been making a lot of noise about Endpoint Detection and Response (EDR) for long, but it’s not actually a new technology. Despite having been around now for roughly 10 years, it’s only recently that EDR has really come to the fore. This has been driven by the fact that traditional antivirus struggles to cope with the increasing sophistication of modern malware, and is certainly unfit to handle new types of cyber threats.
Top 5 Managed Detection and Response Services and How to Choose
Managed Detection and Response (MDR) is an approach to cybersecurity that combines advanced technologies, skilled analysts, and a proactive response process to detect, investigate, and remediate cyber threats. MDR is typically delivered as a service by a third-party provider and includes a range of security capabilities, such as threat intelligence, behavior analysis, anomaly detection, and incident response.
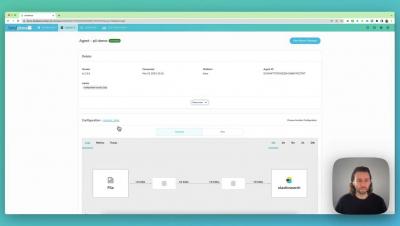
Mask PII Data With BindPlane
Best CMMS Software Features and Its Benefits | Infraon
Datadog Integration Update: Vulnerability Scanning and Audit Logs
The team at Cloudsmith is always looking for ways our customers and community can leverage adjacent technologies within the DevOps and application development ecosystem to secure the software supply chain. Cloudsmith developed the first integration with Datadog, the Cloud Monitoring as a Service solution, a few years ago! That integration was the first step in helping the community leverage both solutions simultaneously, strength for strength.
PagerDuty Announces New Automation Enhancements That Simplify Operations Across Distributed and Zero Trust Environments
Be sure to register for the launch webinar on Thursday, March 30th to learn more about the latest release from the PagerDuty Operations Cloud. Rundeck by PagerDuty has long helped organizations bridge operational silos and automate away IT tasks so teams can focus more time on building and less time putting out fires. And while this mission still rings true today, our vision is to extend this reality and revolutionize all operations while continuing to build trust.
How to properly check if files are readable
Opening and reading files may cause your program to block indefinitely, which is a major problem for configuration management tools like CFEngine. What if we make a program that can check if these file operations would block indefinitely, before using them? Unfortunately our good friend Alan Turing proved that such programs are not theoretically possible.
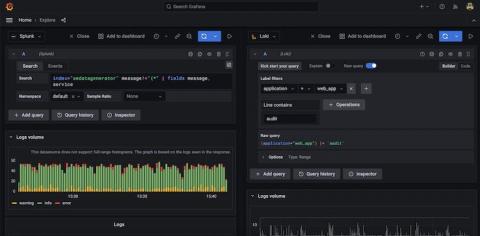
Reduce compliance TCO by using Grafana Loki for non-SIEM logs
Compliance is a term commonly associated with heavily regulated industries such as finance, healthcare, and telecommunication. But in reality, it touches nearly every business today as governments and other regulatory agencies seek to enact tighter controls over the use of our collective digital footprint. As a result, more and more companies need to retain a record of every single digital transaction under their control.
Best Practices for SOC Tooling Acquisition
Your Security Operations Center (SOC) faces complex challenges for keeping corporate data safe and in the right hands everyday. The right tooling is critical for success. Deciding when—and how—to make investments in SOC tooling is complex and challenging across organizations. There’s a ton of vendor spin out there and it’s important to understand what’s real and what isn’t.
Hacking the Cloud and Things to Watch Out for - Civo.com
What is System Hardening? Definition and Best practices
System hardening means locking down a system and reducing its attack surface: removing unnecessary software packages, securing default values to the tightest possible settings and configuring the system to only run what you explicitly require. Let’s take an example from daily life.
Securing Your Monitoring Software With mTLS
Mutual transport layer security (mTLS) is an important subject among security, reliability, and engineering professionals who need to secure API communication as well as communication between machines and the applications and services they run. And for good reason: in 2022, the global average cost of a data breach was US$4.35 million, and almost double that in the United States at US$9.44 million.
How Domain Name Security Helps Prevent DNS Hijacking
You're probably aware of some security best practices to keep your business's digital presence safe. This might include uptime monitoring, security checks, and many others. But what about domain name security? Securing your business's domain name helps prevent commonplace domain hijacking and the associated chaos that comes with this specific type of cybercrime.
How to Build a Cybersecurity Culture in Your Business
In IT, the latest tools are a must to keep companies safe. But here’s why culture is just as important – and how you can foster a safer workforce.
Empowering SecOps Admins: Getting the Most Value From CrowdStrike FDR Data With Cribl Stream
In this live stream, Sidd Shah and I discuss how Cribl Stream can empower Security Operations Admins to make the most of their CrowdStrike FDR data. They address the challenges faced by CrowdStrike customers, who generate a vast amount of valuable data each day but struggle to leverage it fully due to complexity and size.
Air-Gapped Kubernetes with D2iQ (AFCEA West 2023)
Security and real-time Linux in a shifting automotive world
How Are SASE and SD-WAN Related?
Outlook Zero-Day (CVE-2023-23397) Fix for N-central and N-sight
As you likely be all too aware, there is a Microsoft Outlook zero-day vulnerability listed under CVE-2023-23397. With the increased attacks on Outlook this month, Microsoft has pushed out fixes for about 80 Windows flaws. More information on some of those patches can be found in my colleague Lewis Pope’s March 2023 Patch Tuesday blog. Lewis was also kind enough to send over the remediation script for both N-able N-central and N-able N-sight.
Control and Audit Remote Control Actions for Security
In an article a few months ago, my colleague covered the functionality within eG Enterprise that ensures secure and traceable audit trails for both users and admins of eG Enterprise allowing automated auditing and reporting for regulatory compliance and security, see Auditing Capabilities in IT Monitoring Tools | eG Innovations. Today, I will follow from this article and cover how eG Enterprise also controls and audits the execution of Remote Control Actions and scripts.
5 tips on how Developers, DevOps and security teams can work together
In the World of Privacy, Nothing is Free - Including Social Apps | Security Insights Podcast: Ep3
Map cloud security risks and visualize anomalies with Spot Security
What is Penetration Testing?
Penetration Testing -- also known as “pentesting” -- are used by cybersecurity professionals and managed service providers to identify vulnerabilities present in a system before a cybersecurity incident takes place. You will often come across clients asking you to perform penetration testing, especially as emerging government regulations begin to make the practice mandatory.
What is SOAR (Security, Orchestration, Automation, and Response)?
As a managed service provider, you know that cyberthreats are increasing in frequency, sophistication, and impact. In recent years, we have seen a dramatic increase in the number of cyber-attacks targeting businesses, governments, and individuals. This explosion of cyberthreats highlights the need for businesses and individuals to take cybersecurity seriously and implement modernized security measures to protect themselves against these threats.
How To Better Handle Data Online
Why is cyber security crucial to the manufacturing industry?
Canonical joins the confidential computing consortium
Canonical is committed to enabling Ubuntu users to leverage the strong run-time confidentiality and integrity guarantees that confidential computing provides. That is why we are happy to announce we have joined the confidential computing consortium, a project community at the Linux Foundation that is focused on accelerating the adoption of confidential computing and driving cross-industry collaboration around relevant open source software, standards and tools.
Qovery and Doppler Join Forces to Empower Developers with Next-Level Cloud Deployment and Security
Top 6 Cybersecurity Best Practices for MSPs and Enterprises
MSPs own and process large amounts of sensitive data and act as gateways to the sensitive data and infrastructure of their clients, which is why cybercriminals view them as good potential targets. To adequately protect this sensitive data from today’s sophisticated attacks, it is crucial that MSPs leverage cybersecurity best practices to ensure the safety and security of their own systems and their customers’ systems.
How To Find A Good And Affordable Edge Protection Supplier
Secure Your Crypto Assets with Cloud-Based Encryption: An Expert Guide
The Ransomware Pandemic | Security Insights Podcast: Ep. 2
Automotive consortiums: Setting new standards for safety and cybersecurity
Canonical strongly believes that the future of automotive will rely on open source to define and run the next generation of vehicles. To drive this transition, state-of-the-art cybersecurity and functional safety are critical. To learn more about the industry’s specific constraints, we are actively involved in several automotive consortiums and are contributing to automotive-related standards.
Avoid kubernetes security risks with hardening best practices
3 Effective Tips for Cloud-Native Compliance
Using RapidSpike to Support PCI DSS 4.0 Compliance
The latest version of the PCI DSS (Payment Card Industry Data Security Standard) is version 4. We are currently in the transition period following the publication of the new standard, heading towards full implementation.
How RapidSpike Cookie Monitoring Can Support Managing GDPR
When the General Data Protection Regulations (GDPR) and ePrivacy Directive (EPD) updated we saw a proliferation of “cookie consent” banners crop up on websites as a direct result. The key parts of the GDPR relating to this change are from Recital 30: Natural persons may be associated with online identifiers provided by their devices, applications, tools and protocols, such as internet protocol addresses, cookie identifiers or other identifiers such as radio frequency identification tags.
Configuring Single Sign-On (SSO) for Uptime.com
Check out our free trial, no credit card required: https://uptime.com/go/home
#monitoring, #saas, #downtime, #uptime, #nomore404, #outage, #enterprisesbusiness
DevSecOps in Practice with VMware Tanzu - A Discussion with the Authors - Tanzu Talk
Securing Your Network Against Attacks: Prevent, Detect, and Mitigate Cyberthreats
As networks become distributed and virtualized, the points at which they can be made vulnerable, or their threat surface, expands dramatically. Learn best practices for preventing, detecting, and mitigating the impact of cyberthreats. As networks become distributed and virtualized, the points at which they can be made vulnerable, or their threat surface, expands dramatically.
What is Patch Management?
In today’s digital world, software vulnerabilities have become a widespread concern. Cybercriminals are always looking for ways to exploit these vulnerabilities, resulting in devastating security breaches. That’s where patch management comes in. In this article, we’ll discuss what patch management is, its importance, and best practices to implement it.
Forget the pretenders. Get in the Cove
Top 5 Must-Have Home Security Gadgets in 2023
How Hackers Can Hack Your Phone & How To Prevent It
The Evolution of Security: From Good to Better to Best
What is SOC 2 Compliance? | A Guide to SOC 2 Certification
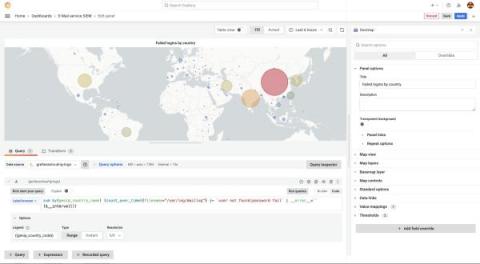
Protect PII and add geolocation data: Monitoring legacy systems with Grafana
Legacy systems often present a challenge when you try to integrate them with modern monitoring tools, especially when they generate log files that contain personally identifiable information (PII) and IP addresses. Thankfully, Grafana Cloud, which is built to work with modern observability tools and data sources, makes it easy to monitor your legacy environments too.
The Importance of Observability Pipelines in Gaining Control over Observability and Security Data
Today’s enterprises must have the capability to cope with the growing volumes of observability data, including metrics, logs, and traces. This data is a critical asset for IT operations, site reliability engineers (SREs), and security teams that are responsible for maintaining the performance and protection of data and infrastructure. As systems become more complex, the ability to effectively manage and analyze observability data becomes increasingly important.
Automatically manage keys and secrets on CircleCI
Data Shredding vs. Recycling: What's the Difference and Why Does it Matter?
6 Signs Your Company is Experiencing Data Breaches
Beyond Logging: The Power of Observability in Modern Systems
Empowering Security Observability: Solving Common Struggles for SOC Analysts and Security Engineers
5 Tips to Improve Network Security Monitoring
Optimizing network security monitoring requires pursuing continuous improvement. Even when people have monitoring tools or processes, it’s always advisable to identify weak spots and look for ways to reduce or eliminate them. Here are five options to consider.
Empower growth with full-stack data security
The volume of data collected by organizations is a goldmine of information that, when leveraged correctly and securely, can positively impact growth.
The FireEye/SolarWinds Cyber Attack | Security Insights Podcast: Ep. 1
4 Tools to Help Protect Against Online Identity Theft
Online identity theft has become a significant concern for everyone, especially as we rely more on the internet for various activities such as shopping, banking, and socializing. Identity theft occurs when someone steals personal information, such as name, address, social security number, or credit card details, to commit fraudulent activities. The consequences of identity theft can be severe: $15.1 billion in monetary loss in a given year alone!
Deploying Mattermost with Zarf for highly secure air-gapped collaboration
Mission-focused teams that operate in contingency environments – think military branches, the intelligence community, NASA – increasingly depend on collaboration software. They need to share information quickly, nimbly, and securely. And they want to carry that out in contextual channels that enable them to see the right content at the right time to make informed, accurate decisions.
Why Automation is Critical for Improving an Enterprise Security Posture
Cybersecurity threats are coming in hot and have quickly become an urgent concern for organizations of all sizes. In response, security teams are shifting away from homegrown security solutions and towards automation using commercially available tools. As organizations seek to improve their security resilience, they find themselves also needing to scale their security teams more efficiently as they address continuous staffing shortages.
Zero Trust Network Access
SSL Certificate Monitoring: A Vital Component of Website Security
Are you concerned about the security of your website or online business? Do you want to ensure that your customers can trust your site and transact with you safely? If so, then you need to know about SSL certificate monitoring! SSL certificate monitoring is the process of continuously monitoring SSL certificates for potential vulnerabilities or incidents, such as certificate revocation or expiration, and other security issues.
We're SOC 2 Type 2 compliant!
Checkly Completes SOC 2 Type 2 Audit
In August 2022, Checkly's security team successfully implemented and documented all necessary security controls to be SOC 2 compliant for the first time. To get our SOC 2 Type 1 report we had to prove that our engineering, HR, operational, and IT security processes met the high level of information security SOC 2 compliance demands to an accredited auditing firm.
CI/CD and Supply Chain Security w/ Anaïs Urlichs
Built on ServiceNow Q&A: Samsung SDS Zero Touch Mobility
Business leaders continue to face new pressures and challenges—from ongoing global uncertainty and increased geopolitical instability to tightening budgets and having to do more with less. To thrive, enterprises must invest for the future while simultaneously finding ways to operate more efficiently. At ServiceNow, we believe partnerships are the answer.
Unlocking the Value of Your Data with Cribl Search: A Journey with Darmar the Security Analyst
Those of you in the know, have already met Darmar, our Security Analyst at the Cribl University campus. (If you aren’t in the know, check out our newly rolled-out CCOE Stream Admin training to meet our beloved – & fictitious – goat). Hang with me, while I recount Darmar’s journey to unlocking the full value of their data.