Operations | Monitoring | ITSM | DevOps | Cloud
March 2023
What Are Containers? - VMware Tanzu Fundamentals
Get More Flexible Kubernetes Security with Policy Improvements in VMware Tanzu Mission Control
Carol Pereira and Corey Dinkens contributed to this blog post. With the increasing complexity of distributed systems, it is essential to define and implement policies for Kubernetes clusters to ensure the security, reliability, and compliance of the environment—and of course to build the scaffolding for scalability. So, we are glad to announce that VMware Tanzu Mission Control now has additional policy improvements designed to enhance Kubernetes security.
Best Practices for Effective Monitoring and Observability - Civo.com
Troubleshooting Application Issues with Extended Labels
Troubleshooting issues in Kubernetes can be tough. When diagnosing these problems, you can find yourself with tons of microservices to review. Sometimes you come across the root cause straight away, but when dealing with complex issues you may lose a lot of time going back and forth, and time is a precious asset when everything goes up in flames. Sysdig Agent leverages eBPF for granular telemetry.
How to Become a Faster and More Efficient Developer?
Nir Shtein, Software Engineer 6 min read March 30th, 2023 Komodor Tutorials As software developers, we always want to improve ourselves continuously. It can be through writing cleaner and more efficient code, using new design patterns, expanding our stack, or deep-diving into a specific technology. We strive to improve; we’re encouraged to do post-mortems with action items and to keep asking what went right and what went wrong.
Containerization 102 Security Optimization and Speed
Supercharging Your Amazon Investment With EKS And CloudZero
Overcoming the Challenges of Managing Testing Environments on AWS
Comprehensive Kubernetes Observability with LogicMonitor's Kube-State-Metrics Integration
Kubernetes Troubleshooting In Action: 5xx Errors Resolved Faster
ITSM Integration in Cloud and Container Resource Optimization
5 Ways to Cure Your Tech Debt Crisis
The companies we at VMware Tanzu work with are constantly looking for new, better ways of developing and releasing quality software faster. But digital transformation means fundamentally changing the way you do business, a process that can be derailed by any number of obstacles. In his recent video series, Coté identifies 14 reasons why it’s hard to change development practices in large organizations, such as security and compliance.
Monitor Calico with Datadog
Calico is a versatile networking and security solution that features a plugable dataplane architecture. It supports various technologies, including Iptables, eBPF, Host Network Service (HNS for Windows), and Vector Packet Processing (VPP) for containers, virtual machines, and bare-metal workloads. Users can employ Calico’s network security policies to restrict traffic to and from specific clusters handling customer data and to quickly block malicious IP addresses during external attacks.
Elastic Observability: Built for open technologies like Kubernetes, OpenTelemetry, Prometheus, Istio, and more
As an operations engineer (SRE, IT Operations, DevOps), managing technology and data sprawl is an ongoing challenge. Cloud Native Computing Foundation (CNCF) projects are helping minimize sprawl and standardize technology and data, from Kubernetes, OpenTelemetry, Prometheus, Istio, and more. Kubernetes and OpenTelemetry are becoming the de facto standard for deploying and monitoring a cloud native application.
Monitoring EKS With Zenoss Service Impact
Q1 2023 Product Retrospective - Last Quarter's Top Features
Redis on Cycle: Configuration and Deployment
Redis is a powerful in-memory data store thats blazing fast. It's performant, scalable, supports a wide range of data structures, has built in caching mechanisms, and is simple to set up for Cycle users. This post will take you from deploying your first Redis instance on Cycle, through deploying highly available, stateful Redis instances that are monitored by Redis Sentinel. The companion repo for this article with configuration files and settings can be found here.
CNCF Survey Shows the Kubernetes Future Looking Bright
The annual Cloud Native Foundation (CNCF) surveys have shown Kubernetes adoption and maturity advancing rapidly, The previous CNCF Annual Survey showed that Kubernetes had crossed the chasm to become mainstream.
Hacking the Cloud and Things to Watch Out for - Civo.com
Heroku to AWS Migration Made Easy with Qovery and Cloud303
MicroK8s is now on AWS marketplace
Everyone knows that MicroK8s is an extremely lightweight, extensible, reliable, CNCF-compliant distribution of Kubernetes. What you didn’t know until now is that it is even easier to install and manage as part of your AWS marketplace experience. First, a quick reminder of why MicroK8s is great: What is new is that MicroK8s is now available on the AWS marketplace, combining all of MicroK8s advantages with the convenience of AWS.
Air-Gapped Kubernetes with D2iQ (AFCEA West 2023)
Introduction to Kubernetes Observability
Kubernetes CreateContainerConfigError and CreateContainerError
CreateContainerConfigError and CreateContainerError are two of the most prevalent Kubernetes errors found in cloud-native applications. CreateContainerConfigError is an error happening when the configuration specified for a container in a Pod is not correct or is missing a vital part. CreateContainerError is a problem happening at a later stage in the container creation flow. Kubernetes displays this error when it attempts to create the container in the Pod.
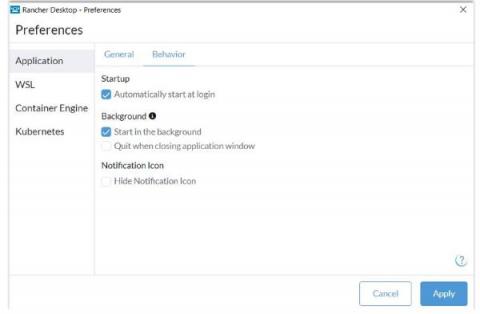
Rancher Desktop 1.8: Now with Additional Configuration Options and More
We are pleased to announce that a new Rancher Desktop version with additional configuration options, deployment profiles, a gvisor-based networking stack on Windows and several other improvements has just been released!
Is it Time to Put Your Pet Kubernetes Down? - Civo.com
Provision your Cloud Infrastructure Directly with kubectl using OpenCP - Civo.com
How to Manage the High Cost of Scaling on Heroku
Kubernetes 101: A comprehensive guide
Over time, Kubernetes has become a household name for container orchestration as organizations aim to streamline complex processes. With its rapidly growing popularity and convenient ecosystem, many organizations started using it to manage their applications and workloads. But what exactly is it, and how did it come into existence?
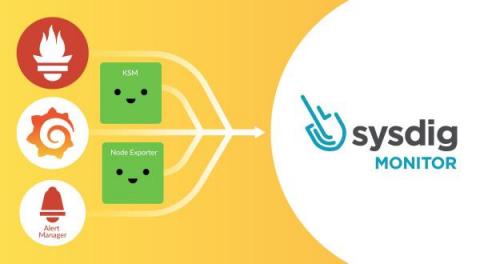
Migrating from Prometheus, Grafana, and Alert Manager to Sysdig Monitor
Are you an OSS Prometheus, Grafana, and Alert Manager user thinking about migrating to Sysdig Monitor, and don’t know about the transition details? Are you wondering what the benefits are of using Sysdig Monitor instead of DIY Prometheus, Grafana, and Alert Manager? If so, then this article is for you!
Monitoring Kubernetes Object Configuration with LogicMonitor
A Kubernetes Observability Tool to Support SRE Best Practices
Kubernetes can be tough to troubleshoot and remediate fast, especially when you have many interdependent services. This blog, part 3 of 3 in the “8 SRE Best Practices to Help Developers Troubleshoot Kubernetes” series, describes the Kubernetes observability foundation StackState has built to support SRE best practices and enable rapid remediation of issues.
Merging to Main #1: Modernizing your CI/CD
Automating deployment to an EKS cluster using CircleCI and Helm Charts
Kubernetes is a container orchestration system for automating deployment and managing containerized applications. Helm is a Kubernetes package manager that helps you define, install, and upgrade Kubernetes applications. It lets you define reusable templates for Kubernetes components (deployment, service, hpa, service account, etc.) that can be published and shared across applications. In this tutorial, you will learn how to build and install Helm charts for your application to an AWS EKS cluster.
Qovery and Doppler Join Forces to Empower Developers with Next-Level Cloud Deployment and Security
Practical tips for rightsizing your Kubernetes workloads
When containers and container orchestration were introduced, they opened the possibility of helping companies utilize physical resources like CPU and memory more efficiently. But as more companies and bigger enterprises have adopted Kubernetes, FinOps professionals may wonder why their cloud bills haven’t gone down—or worse, why they have increased.
Measure Your Container-Management Maturity and Up Your Cloud-Native Game
D2iQ has made available a new assessment tool that enables you to gauge your container management maturity level. By taking a 1-minute quiz, you can identify where you fit within the five levels of cloud-native container-management maturity–Explorer, Beginner, Intermediate, Advanced, and Master. The maturity model is based on the wisdom of D2iQ Kubernetes experts with more than a decade of experience building and deploying Kubernetes platforms for customers.
Turning Kubernetes into a Developer-Friendly Product
Create a streaming dataset for Apache Kafka with Docker
Enlightning - Develop at Lightning Speed on Kubernetes with DevSpace
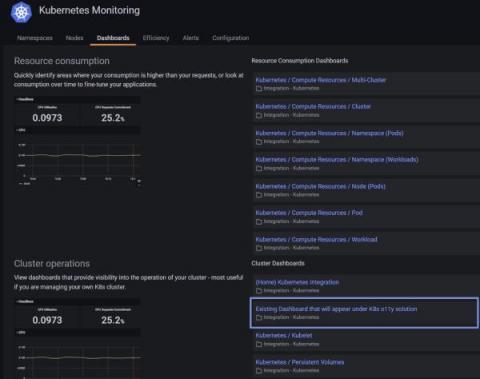
How to migrate existing Grafana dashboards and alerts into Kubernetes Monitoring in Grafana Cloud
Kubernetes Monitoring in Grafana Cloud is already an observability Swiss Army knife: You can monitor your Kubernetes fleet performance, nodes, pod logs, resource utilization, and overall infrastructure health all in one hosted platform that comes with prebuilt Grafana dashboards to visualize all the important telemetry you need. All of this sounds great … but what if you already have Grafana dashboards and alerts that are custom to your fleet and the way you do business?
DevSecOps in Practice with VMware Tanzu - A Discussion with the Authors - Tanzu Talk
Integrating Komodor with PagerDuty
PagerDuty provides a SaaS-based platform that enables developers, DevOps, IT operations, and business leaders to prevent and resolve incidents that could potentially impact customer experience. This platform allows organizations to proactively manage events that may affect customers across their IT environment, which is crucial for maintaining customer satisfaction, revenue, and brand reputation.
Kubernetes vs OpenStack: which one to choose?
Kubernetes vs OpenStack is a common dilemma that organisations face when considering the modernisation of their IT infrastructure. Both are well-established open-source technologies for building cloud infrastructure, and both bring tangible benefits, especially when used in combination. Yet, they differ significantly and need to be properly bundled to feel like a fully-integrated solution. What does this mean in practice? Let’s take a look!
Kubernetes CPU Requests & Limits VS Autoscaling
In a prior blog post, we discussed the basics of Kubernetes Limits and Requests: they serve an important role to manage resources in cloud environments. In another article in the series, we discussed the Out of Memory kills and CPU throttling that can affect your cluster. But, all in all, Limits and Requests are not silver bullets for CPU management and there are cases where other alternatives might be a better option.
The Cost of Cloud - Mark Boost
What is Helm? A complete guide
Helm is a tool that automates the creation, packaging, configuration, and deployment of Kubernetes applications by combining your configuration files into a single reusable package. In a microservice architecture, you create more microservices as the application grows, making it increasingly difficult to manage. Kubernetes, an open source container orchestration technology, simplifies the process by grouping multiple microservices into a single deployment.
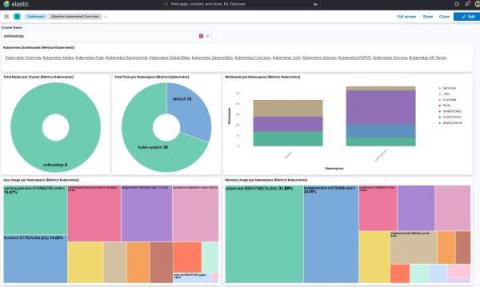
Using Elastic to observe GKE Autopilot clusters
Elastic Agent provides a new observability option for fully managed GKE clusters
Deploy Open Telemetry to Kubernetes in 5 minutes
OpenTelemetry is an open-source observability framework that provides a vendor-neutral and language-agnostic way to collect and analyze telemetry data. This tutorial will show you how to integrate OpenTelemetry on Kubernetes, a popular container orchestration platform. Prerequisites.
How to choose the right cloud provider?
With the need for cloud computing and cloud-native technologies, many businesses are moving workloads to the cloud. Hence, there will be a need for a cloud service provider. This blog will cover the steps to choosing the perfect cloud provider and how a multi-cloud approach can reduce costs. In our meetup with Mark Boost, Dinesh Majrekar, and Saiyam Pathak, they discussed the current state of the cloud industry, why costs are so high, how to reduce your spending, and looking at how Civo can help.
AWS recognizes Sysdig as an Amazon Linux 2023 Service Ready Partner
Sysdig is pleased to announce that we’re now recognized as Amazon Linux 2023 Ready as part of the Amazon Web Services (AWS) Service Ready Program. Amazon Linux 2023 (AL2023) is the newest Linux operating system from AWS available to support your workloads running on Amazon EC2. The team at Sysdig validated AL2023 with Sysdig Secure and Sysdig Monitor to ensure full support for our container security and cloud-native monitoring capabilities with this latest OS.
Create Git Repositories and CI/CD Pipelines with the Terraform Provider for Codefresh
The Codefresh User Interface allows all application stakeholders to view and manage their applications in a user-friendly manner with comprehensive dashboards and detailed overview screens. It is not however the only way of managing Codefresh. Codefresh also comes with a powerful CLI as well as an extensive API that allows developers and operators to completely bypass the UI and create their own automated workflows with their favorite tools.
Introducing Native IPSec Support
Today, we are thrilled to announce a major upgrade to the security of your networks and infrastructure on the Cycle platform. With the most recent update, our team has added IPSec support to Cycle’s Compute layer. If you’re not familiar with IPSec, it’s a suite of different encryption and authentication protocols which enables secure communication between servers.
From Kubernetes Out Of Kubernetes Observability and Shifting left chaos testing
VMware Application Catalog Extends Support to Google Artifact Registry
VMware Application Catalog (formerly Tanzu Application Catalog) is a catalog of trusted, continuously maintained, and verifiably tested open source images that is custom-built to enterprise specifications, and privately delivered directly to a customer’s registry of choice. Recently, we added JFrog Container Registry and Amazon Elastic Container Registry to our list of supported registries, in addition to Google Container Registry, Azure Container Registry, and Harbor.
Terraform, GitOps, Helm: Automation and package management with VMware Tanzu Mission Control
Sneha Narang, Carol Pereira, and Lauren Britton contributed to this blog post. Kubernetes adoption is on the rise because it helps organizations improve software development with increased flexibility and efficiency while controlling cloud costs. In fact, our State of Kubernetes 2022 report shows 62 percent of respondents claiming that Kubernetes increases the flexibility of applications and 54 percent agreeing it offers better developer efficiency.
How to Create a Kubernetes Preview Environment
If The Beatles Were Your Retail IT Consultants, You'd Be Ringing Up the Hits
In a relatively short period of time, from 1962 to 1969, The Beatles produced a volume of work that made them the most successful recording artists of all time as measured by their volume of record sales, number-one hits, and duration of hits on the charts.
How CloudZero Unlocks Kubernetes Costs Better Than Anyone
Enlightning - Kustomize Demystified
k3s vs k8s - The Difference Between k3s vs k8s
Our CTO Andy Jeffries explains how k3s by Rancher Labs differs from regular Kubernetes (k8s). Since we launched the world’s first k3s powered, managed Kubernetes service – we’ve had a lot of questions from our members on what the differences are between k3s and k8s (full blown Kubernetes), aside from the choice from each on how to capitalise a "K" (or not).
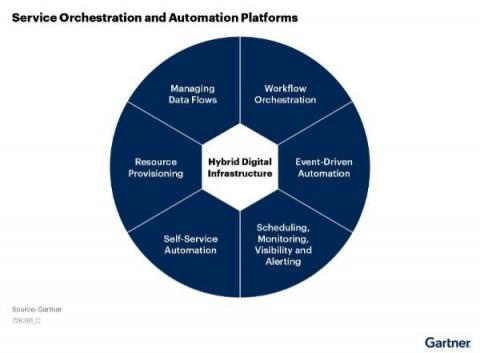
Maximizing Efficiency: How SOAP Can Transform Your Enterprise Automation Strategy
Rajeev Kumar, Automation Product Leader at Broadcom, explores the 2023 Gartner® Market Guide for Service Orchestration and Automation Platforms. He reveals how Automation from Broadcom embraces the concepts of SOAP, driving a modern workload automation strategy.
Why Is Kubernetes Troubleshooting So Hard?
Maintaining reliable Kubernetes systems is not easy for anyone, especially for team members with less in-depth knowledge of Kubernetes itself and the overall service environment. This blog, part 1 of 3 in the “8 SRE Best Practices to Help Developers Troubleshoot Kubernetes” series, outlines the key challenges SREs and developers face when they need to quickly troubleshoot and remediate issues in applications running on Kubernetes.
How vcluster is Changing the Game
Easily Monitor Google Cloud with Sysdig's Managed Prometheus
Google Cloud provides its own set of metrics for monitoring applications, services, and instances. There are a huge number of metrics – more than 1,500 different ones just for GCP monitoring! While this is great, dealing with such a number can also be overwhelming. Filtering, pulling, exploring, and storing the metrics that you really need can be an enormously time-consuming task, and a big challenge.
Network Policies in K3s
In this post we want to give a simple introduction for using network policies in a sample project and explaining how it works in K3s to help improving the security of your deployments. There is a common misunderstanding about K3s support for network policies, as K3s is using flannel CNI by default, and the Flannel CNI doesn’t support network polices.
A Guide to Using Rancher for Multicloud Deployments
Rancher is a Kubernetes management platform that creates a consistent environment for multicloud container operation. It solves several of the challenges around multicloud Kubernetes deployments, such as poor visibility into where workloads are running and the lack of centralized authentication and access control. Multicloud improves resiliency by letting you distribute applications across providers.
6 Best AWS Deployment Options to Consider in 2023
Bypassing Network Detection with Graftcp
What is the difference with similar tools? Detect graftcp with Falco Conclusion A new network open source tool called graftcp (GitHub page) has been discovered in everyday attacks by the Sysdig Threat Research Team (TRT). Nowadays, threat actors try to improve their techniques by using new tools (as we mentioned in the PRoot article) to enhance the compatibility of their code to hit as many targets as possible and hide their traces properly.
Top Trends in DevOps - Serverless Computing
The world of DevOps is constantly evolving and adapting to the needs of the software development industry. With the increasing demand for faster and more efficient software delivery, organizations are turning to modern technologies and practices to help them meet these challenges. In a series of articles on the Kublr blog, we will take a look at some of today’s top DevOps trends.
Deploying Kubernetes at the Edge with VMware Tanzu Using Single Node Clusters
Managing Kubernetes Edge Locations at Scale with VMware Tanzu Mission Control
Tips and best practices for Docker container management
K8s Control Plane - Securing Kubernetes API with Intel SGX
Security in the cloud has become an increasingly important topic over the years, with the move to more managed services, additional trust is being handed over to cloud providers. With this being said, we must begin to pay closer attention to the security surrounding cloud computing, especially when it comes to Kubernetes. Join me as I explore the concept of confidential computing and a new use case we at Civo have been working on related to the Kubernetes control plane in managed clusters.
Data Pipelines on DKP: Building a a big data pipeline with NiFi, Kafka, and Elastic
Adding Kubeflow to the D2iQ Kubernetes Platform (DKP) Catalog
Adding JupyterHub the D2iQ Kubernetes Platform (DKP) Catalog
FULL EKS & Kubernetes Debugging Journey with Coralogix
Clone Service vs Clone Environment with Qovery
Kubecost and Qovery Team up to Offer Cost Monitoring for DevOps Teams
How to optimize resource utilization with Kubernetes Monitoring for Grafana Cloud
Overprovisioning or underprovisioning your Kubernetes resources can have significant consequences on both your budget and your app performance. By underprovisioning your Kubernetes infrastructure, you’ll end up with lagging, underperforming, unstable, or non-functional applications. On the opposite end of the spectrum, overprovisioning is a costly issue: Organizations spent almost $500 billion on cloud resources in 2022, yet an estimated 30% of those were wasted.
How We Designed Qovery To Manage Thousands of Kubernetes Clusters with a Single Control Plane
Prometheus Exporters in Sysdig Monitor
Nowadays, it is rather common to see companies adopt several monitoring solutions based on Prometheus, but this is not exempt from pain. A huge number of systems, applications, and third-party software are not instrumented to expose Prometheus metrics natively. Here is where Prometheus exporters come into play.
Sysdig Live: Three Cloud Adoptions Trends of 2023
Kubernetes Logging
You'll notice that monitoring and logging don't appear on the list of core Kubernetes features. However, this is not due to the fact that Kubernetes does not offer any sort of logging or monitoring functionality at all. It does, but it’s complicated. Kubernetes’ kubectl tells us all about the status of the different objects in a cluster and creates logs for certain types of files. But ideally speaking, you won't find a native logging solution embedded in Kubernetes.
CI/CD and Supply Chain Security w/ Anaïs Urlichs
Millions wasted on Kubernetes resources
Content The Sysdig 2023 Cloud-Native Security and Container Usage Report has shed some light on how organizations are managing their cloud environments. Based on real-world customers, the report is a snapshot of the state of cloud-native in 2023, aggregating data from billions of containers.
Heroku vs Elastic Beanstalk: What to choose?
Elevate Kubernetes Security with Zero Trust
The theme of this year’s Rocky Mountain Cyberspace Symposium was " Post-Pandemic Zero Trust." In General Dynamics Information Technology’s 2022 report, “ Agency Guide to Zero Trust Maturity,” 63% of respondents from federal civilian and defense agencies said they believed their agencies would achieve specific zero trust security goals by the end of fiscal 2024.
How Delivery Hero uses Kubecost and Datadog to manage Kubernetes costs in the cloud
As the world’s leading local delivery platform, Delivery Hero brings groceries and household goods to customers in more than 70 countries. Their technology stack comprises over 200 services across 20 Kubernetes clusters running on Amazon EKS. This cloud-based, containerized infrastructure enabled them to scale their operation to support increasing demand as the volume of orders placed on their platform doubled during the pandemic.
Managing Rancher Kubernetes Engine (RKE/2) with the D2iQ Kubernetes Platform (DKP)
Managing Open-Source K3s with the D2iQ Kubernetes Platform (DKP)
Monitoring with Custom Metrics
By kickstarting a monitoring project with Prometheus, you might realize that you get an initial set of out-of-the-box metrics with just Node Exporter and Kube State Metrics. But, this will only get you so far since you will just be performing black box monitoring. How can you go to the next level and observe what’s beyond? They are an essential part of the day-to-day monitoring of cloud-native systems, as they provide an additional dimension to the business and app level.
Epinio Meets s3gw
Since the very first version, Epinio has made use of an internal S3 endpoint to store the user’s projects in the form of aggregated tarballs. Those objects are then downloaded and staged by the internal engine’s pipeline and, finally, they are deployed into the Kubernetes cluster as consumable applications. Epinio makes use of S3 as an internal private service. In this scenario, S3 can be thought of as an internal ephemeral cache with the purpose of storing temporary objects.
Kubernemlig's Multi-Cluster DNS Setup
Moving Fast and Cutting Costs in a Billion-Dollar Organization: Containers in the Automotive Industry
One may say that competitive dynamics in the automotive space are constantly changing, and they would not be wrong in the slightest. As retailers face the daily battlefield of getting their customers’ attention with the right mix of products at the right price and on the right platform, their technology infrastructure must be lean and efficient while achieving those goals—and that is no easy feat.