Operations | Monitoring | ITSM | DevOps | Cloud
November 2023
Explore Azure Integration Environments and Business Process Tracking in Public Preview
Azure Savings Plan vs Reserved Instances
Kubeapps: An Open Source Application Dashboard for Kubernetes from Bitnami by VMware Tanzu
Kubeapps is one of the open source projects that the Bitnami team at VMware contributes to, and it is among the 100+ pre-packaged open source images present in Bitnami Application Catalog and VMware Tanzu Application Catalog (the enterprise edition of Bitnami Application Catalog). This blog presents an overview of Kubeapps and how you can use it to simplify your Kubernetes application deployments.
An overview of Azure Integration Environments & Business Process Tracking | Microsoft Ignite 2023
Azure cost management: Tips and tricks for Azure spend reduction #cloudcostoptimization
Explore more on the Cost Analyzer feature from Serverless360: https://bit.ly/3N2Uw5S
Also, check out the #1 platform to supercharge your Microsoft Azure monitoring: https://bit.ly/3EnuTbg
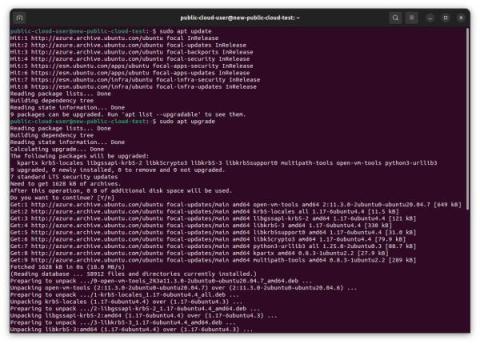
Ubuntu Pro explained in 2 minutes
Kubernetes Troubleshooting Tutorial
Multi-Cluster Observability Part 2: Developing The Right Strategy
This is the second of a three-part blog series. Prior to reading this, be sure to check out Part 1, Benefiting from multi-cluster setups requires familiarity with common variations. In your Kubernetes journey, it's highly likely that you'll encounter the need to manage multiple clusters simultaneously.
Troubleshooting Android Issues Remotely with AirDroid Remote Support | Android Remote Control
Announcing HAProxy Fusion 1.2 LTS
HAProxy Fusion 1.2 is now available, making it even simpler to adopt modern, scalable application delivery. New efficiencies, workflows, and form factors enable you to be more productive, use familiar tools, and explore powerful new use cases.
Kubernetes for Humans Podcast with ETL Shwartz
Kubernetes Unpacked: Embracing GitOps & Best-Practice Tools with Kubefirst
How we Chartered a Course to Helm's Success with CNCF with Matt Butcher - Navigate Europe 23
Future of GitOps by Kubefirst's John Dietz at KubeCon NA 23 - Civo TV
Behind the Music with Assets in Jira Service Management
10 Things to Consider before Multicasting Your Observability Data
This article was originally published in APM Digest here. Multicasting in this context refers to the process of directing data streams to two or more destinations. This might look like sending the same telemetry data to both an on-premises storage system and a cloud-based observability platform concurrently. The two principal benefits of this strategy are cost savings and service redundancy.
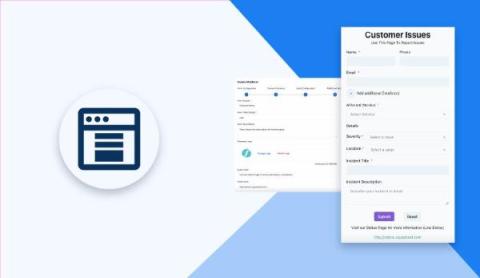
Your guide to better incident status pages
Your status page (or lack thereof) has the opportunity to signal a lot about your brand — how transparent you are, how quickly you respond to incidents, how you communicate with your customers — and ultimately, this all seriously impacts your reliability. After all, as our CEO Robert put it in a recent interview on the SRE Path podcast, you don’t get to decide your reliability; your customers do.
Common Problems with Container Platforms
Containers are nearly ubiquitous in software these days. Outside of abstractions like fully managed services (RDS, Dynamo, Cloud SQL), everything engineering teams are responsible for, mostly, land in containers. For many, deciding what platform to run those containers on is a burning question. Choosing the wrong container management solution can be a real headache.
Networks in 2030: How service providers can plan for success
By 2030, the world will look very different, not in the least because of new technological innovations. Many will expect to see a proliferation of next-generation technological solutions from smart cities, to augmented reality, to autonomous cars, to the metaverse. Service providers have a role to play in ensuring that the underlying network that we have across the UK (and beyond) has the capacity and scalability to support these solutions.
What is Squashing in Git? #shortsvideo #shorts
Elevate Your Coding Game with GitLens for Visual Studio Code! #shorts #shortsvideo
DevNext Workshop 3: Accelerate Releases with JFrog Distribution
Grafana vs. Power BI
Grafana vs. Power BI – This is often a confusing decision for people wanting to select a data visualization and analytics tool with visually appealing and interactive insights. In this article, we highlight the features and benefits of both tools —Grafana and Power BI, bringing out their key differences to help you make a better decision. If you're interested in trying it out for yourself, sign up for our free trial.
Is Cloud Infrastructure Right For You?
The Cloud infrastructure solution has been around for many years now and has been proven that it can optimize your operations, reduce costs, and boost the efficiencies of developers. Thanks to these benefits, organizations of all sizes in different industries are considering moving into the Cloud infrastructure if they haven’t. This article will explore the world of cloud infrastructure, helping you determine if it is the right fit for your organization.
Need a better tool for sprint planning? #shortsvideo #shorts
First User Panel discussion! | Netdata Office Hours #10
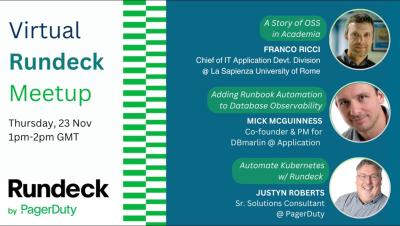
#5 Rundeck by Pagerduty Community Meetup: Automate Kubernetes w/ Rundeck (Part 3)
Orchestrating Kubernetes with Terraform: A Step-by-Step Guide to Building Your Container Empire
Guide to Office 365 Compliance and Data Governance
In the digital era, businesses face an intricate web of legal and regulatory requirements. Navigating these complexities is crucial for maintaining customer trust, protecting sensitive information, and avoiding legal repercussions. The adoption of cloud services like Microsoft Office 365 has transformed how businesses handle data, bringing both opportunities and challenges in compliance.
Generative AI explained
Azure Integration Services End to end management & monitoring scenarios -Wagner and Slava Koltovich
Challenges with Traditional SCA Tools
Application security testing tools are designed to ensure that applications are put through rigorous security assessments to identify security flaws within the application and its code. Even though applications are tested thoroughly (in static and dynamic ways), attackers always seem to find new ways of compromising them.
Top 12 Best Practices for Network Monitoring
Network monitoring is a critical component in network management, ensuring that all systems and services are running smoothly. Monitoring a network involves continuously surveilling network components to detect any potential issues or performance bottlenecks that may arise. Doing so guarantees that the network’s performance remains at its peak, providing users with a seamless experience.
Building a Network Monitoring Dashboard: A Guide
A smooth business operation hinges on maintaining a robust and efficient network. Proactively identifying and addressing issues before they impact users is critical. Network monitoring plays a pivotal role, and a network monitoring dashboard is a key tool in the arsenal.
What Temperature Should Your Data Center Be?
Over the past 5 years, the average server rack density increased from 5kW to 8-10kW, prompting temperature rises in the data center. These temperature increases can become a major issue if not handled properly. Maintaining the correct temperature is extremely important because nearly 30% of unplanned data center outages are caused by environment issues. Not monitoring and analyzing your environment can have a negative impact on energy and resource efficiency.
Flexera Vs. CloudHealth: An In-Depth Comparison
Azure Cosmos DB Monitoring
Monitor More of Your IT Infrastructure
Doing DevOps Your Way On SaaS Solutions: Custom Plugins Come to JFrog Cloud with Workers Service
Using OpenID Connect (OIDC) for Azure access
CircleCI jobs can use OpenID Connect (OIDC) identity tokens to securely access cloud providers without having to store a static credential in CircleCI. This article describes how to access Azure resources using OpenID Connect (OIDC).
Streamline your CD pipeline for Cisco Cloud Observability
Love is Blind, But your K8s Collaborative Troubleshooting Doesn't Have to be - Navigate Europe 23
Simplify Repo Management with Workspaces #shortsvideo #shorts
Want to Migrate to Cloud? Here's What You Need to Know
Making Utilities Smart
Speedscale vs. JMeter: Kubernetes Load Testing Comparison
Unlocking Visibility and Control: Introducing Squadcast's Service Graph Feature
Comparing the Top 9 Pagerduty Alternatives in 2023
Pagerduty is a popular Incident Management platform that helps teams respond to alerts and incidents quickly and efficiently. However, its pricing structure can be complex and expensive for scaling businesses and Incident Response teams. In this blog post, we will compare the top 9 Pagerduty alternatives in 2023, and help you to choose the best one for your needs.
How to Implement FinOps Successfully
This is the fifth and final part of this FinOps series, The Operate Phase. If you have missed any of my previous blogs, here is a list of posts in the series: Note: I am ex-AWS, so you will notice a lot more focus on AWS tools and services as examples here, however we are cloud agnostic and all cloud providers have similar services and tools.
Engineering nits: Building a Storybook for Slack Block Kit
We care a lot about the pace of shipping at incident.io: moving fast is a fundamental part of our company culture, and out-pacing your competition is one of the best ways we know to win. In engineering teams, one way to ship fast is to invest in tools that make your team more productive. We've become good at identifying small pains and frustrations that slow us down over time and – after surfacing them to the rest of the team – find solutions for them.
You Took HOW Much Money?!?
This week, we announced that Cloudsmith has taken an impressive $11M in additional funding, hot on the heels of our $15M Series A two years ago. That's not just serious cash for a startup; it's a game-changer! The natural questions are: why did we take it, and what's our big-picture plan?
Build Operational Resilience with Generative AI and Automation
For modern enterprises aiming to innovate faster, gain efficiency, and mitigate the risk of failure, operational resilience has become a key competitive differentiator. But growing complexity, noisy systems, and siloed infrastructure have created fragility in today’s IT operations, making the task of building resilient operations increasingly challenging.
Introducing Cortex Eng Intelligence
Ensuring Robust Security in Office 365
In an era where digital threats are evolving rapidly, securing your Office 365 environment has never been more crucial. Office 365, a suite known for its robust productivity tools, also demands a proactive approach to security. This blog post delves into essential practices and strategies to fortify your Office 365 setup against various cyber threats.
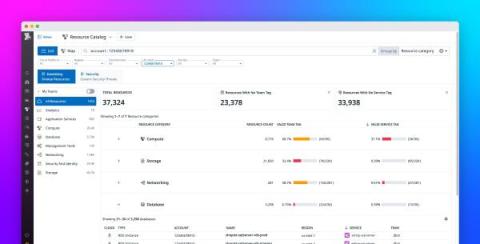
Govern your infrastructure resources with the Datadog Resource Catalog
As an administrator of an expanding, highly distributed infrastructure, you may be responsible for overseeing thousands of on-premise and cloud resources from multiple providers—governed under dozens of accounts by a complex nest of RBAC rules. To query all these resources for purposes such as compliance audits and access management, you may be required to write custom scripts and painstakingly sift through data across disparate tools.
Digital Disruption in Financial Services: Getting Ahead with Automation
The state of financial services today spotlights core banking digitization and the bigger-than-life disruption it’s causing in the industry. It makes sense that going to the bank sounds like an errand people no longer need to run. Even though 77 percent of banking consumers still use traditional banks in some capacity, 43 percent keep their funds elsewhere, and 61 percent will likely switch to a digital-only provider, Galileo Financial Technologies found.
Running Policy in Hard to Reach Places with Wasm with Charlie Egan - Navigate Europe 23
Migrating Databases Best Practice by Percona at KubeCon NA 2023 - Civo TV
Want a new way to share code? #shortsvideo #shorts
Real-time Linux: a comprehensive guide
14 DevOps and SRE Tools for 2024: Your Ultimate Guide to Stay Ahead
As we approach 2024, the DevOps and SRE landscapes continue to evolve, bringing forth a new generation of tools designed to enhance efficiency, scalability, and reliability in software development and operations. In this post, we'll dive into some of the most promising tools that are shaping the future of Continuous integration and deployment, monitoring and observability, infrastructure/application platforms, incident management & alerting, security, and diagramming.
4 Pillars of Successful DevOps Assessment
DevOps isn’t just a methodology; it’s a culture that fosters collaboration, automation, and continuous improvement within an organization. Conducting a successful DevOps assessment is crucial for understanding where your team stands in its DevOps journey and identifying areas for enhancement. To ensure a comprehensive evaluation, focus on these four pillars.
Top 5 Incident Response Tools to Watch Out for in 2024
Kubernetes vs Docker. What you need to know
What Is Cloud Scalability? Benefits And Tips For Every Organization
AI Explainer: The Dirty Little Secret About ChatGPT
Monitor and improve your CI/CD on AWS CodePipeline with Datadog CI Visibility
CI/CD services such as AWS CodePipeline enable developers to automate and accelerate the process of building, testing, and deploying code. But with the speed, scale, and complexity of the modern software development life cycle, even small performance regressions or increases in failure rates in your CI system can quickly snowball, slowing or even halting releases and causing cost overruns.
What is a Console Connect Edge Port?
Why Hourly Granularity Is Necessary For Effective Cloud Cost Management
6 Ways To Get Engineers More Involved In Cloud Costs
Azure Logic Apps Pricing
Top SRE Tools for Enhanced Site Reliability
Site Reliability Engineering (SRE) stands out as a crucial discipline, ensuring the smooth operation and scalability of intricate software systems. SREs employ a diverse toolkit, automating tasks, monitoring system health, and proactively tackling potential issues. The goal? To elevate site reliability and keep downtime at bay. In this blog, we'll dive deep into the realm of SRE tools, breaking down what each tool brings to the table.
Wasm - From your Laptop to the Cloud and Back Again by Danielle Lancashire - Navigate Europe 23
How Can You Contribute to Open-Source Projects with @salaboy - KubeCon NA 23 Insights - Civo TV
Model Deployment with CircleCI & Amazon SageMaker
Your incident declaration form is (probably) too long: The power of concise reporting
It’s 10am, your coffee is ready and piping hot, and you have just been paged. Looks like is down, and customers are starting to notice. With no time to lose, you open up your organization’s incident declaration form and you spend the next thirty minutes filling out the fifteen required fields, while the incident grows bigger and more complex, messages are rolling in, and your coffee grows cold.
Secure Open Source Consumption: Level 1 of S2C2F
Uncover how to reach Level 1 in S2C2F a framework for secure OSS consumption.
The Benefits of Cloud Computing for Small Businesses: Cost Savings, Flexibility, and Security
At one time, tech advancements were a major drain on small businesses. Housing your software and digital assets in-house once created a financial nightmare many emerging companies couldn't handle. On top of that, threats to security and a complete lack of flexibility made establishing a foothold challenging. That was especially true when going up against established industry heavy hitters.
10 Tips and Tricks for SharePoint Online Administration
SharePoint Online, a cornerstone of modern enterprise collaboration and content management, offers administrators a range of tools and features to optimize and secure their digital workspace. This article delves into several advanced tips and techniques, offering in-depth insights for SharePoint Online administrators to elevate their site management and user engagement strategies.
Why You Need Different Backup Solutions for VMs and Containers
One spot for FinOps: Introducing Cost Intelligence and Billing Engine
Overview of AirDroid Business (MDM Solution)
Hyperview DCIM 4.1 Software Release
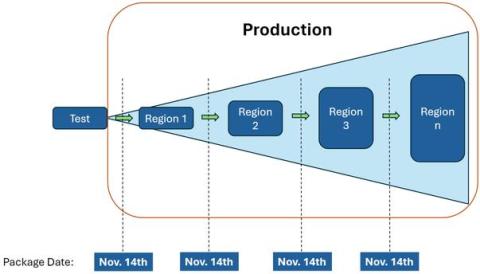
Using Amazon SageMaker orb to orchestrate model deployment across environments
This tutorial guides you on how to use the Amazon SageMaker Orb to orchestrate model deployment to endpoints across different environments. It also shows how to use the CircleCI platform to monitor and manage promotions and rollbacks. It will use an example project repository to walk you through every step, from training a new model package version to deploying your model across multiple environments.
Who loves Jira?
Stop babysitting Jira
Grafana Tutorial - Annotations
Grafana is a tool that helps users identify and fix performance issues by allowing them to monitor and analyze their database. Grafana is famous for making great graphs and visualizations, with tons of different functionalities. This Grafana tutorial is about one of these functionalities: Annotations. Grafana annotations are for users who want to make notes directly onto the graphs in their dashboards. There are various reasons a user might want to do this.
Implementing Security in your AIS Solutions - Alessandro Moura
Building Real time Analytics on Kubernetes by Robert Hodges - Navigate Europe 23
Kubernetes: Managed by Qovery vs. Self-Managed with Qovery (BYOK)
Opinionated Observability with Ralph Meijer - Navigate Europe 23
Top 3 Reasons to Use Feature Flags by DevCycle at KubeCon NA 23 - Civo TV
Improving Customer Support with Squadcast Webforms: A Smart Solution for MSPs
How To Monitor Cisco Catalyst Metrics with Grafana
In today's interconnected world, the reliability of network infrastructure, especially Cisco Catalyst switches, plays a key role for businesses. To ensure these critical components perform optimally, it's vital to monitor their metrics effectively. This article will show you how to effortlessly monitor Cisco Catalyst metrics with Grafana, a top-tier monitoring and visualization platform.
Ubuntu Explained: How to ensure security and stability in cloud instances-part 3
Building Logs to Metrics pipelines with Vector
Building a comprehensive toolkit for machine learning
Document Azure Environment to monitor Azure usage
How can you Reduce your Kubernetes Costs during Development - KubeCon NA 23 Insights - Civo TV
Farming Cloud Native Platforms Be Prepared for the Army of Chickens and Eggs! - Navigate Europe 23
Canonical Data Episode 1: Inside Spark and Kafka with Rob Gibbon and Enrico Deusebio
How can Serverless360 help me on my BizTalk to AIS journey
Introducing Workflows: Enhancing Automation in Incident Response
How to create log sinks
Kubernetes Configmap: Our Complete Guide
Web Management Address Autodetection
The release of 4.1 comes with some exciting updates. Web management address discovery now becomes a breeze with Autodetection. Firmware Updates now support Panduit Gen5 and nVent Enlogic EN2.0 rack PDUs. Not to mention, the Location Layout offers enhanced floor plan visualization with convenient export options. These updates and more provide you with better control and improved visibility.
Terraform Time | Let's move on with PagerDuty Incident Workflows for Incident Response automation
Introducing Squadcast Workflows | Automating Incident Response | Squadcast
How to Combine Speed and Trust in Enterprise Software Development
How to unlock your leadership potential on a cloud migration project: A guide for the DBA, part 2
Bringing Product Thinking to Your Platform by Abby Bangser - Navigate Europe 23
2023 CI/CD Challenges from Solomon Hykes at KubeCon NA 2023 - Civo TV
A Beginner-Friendly Guide To Azure Cloud Management
The Role of Containers and Kubernetes in DevOps Transformation
Containers and Kubernetes has become the cornerstone of modern DevOps practices. As organizations strive for agility, scalability, and seamless collaboration between development and operations teams, the adoption of Containers and Kubernetes has emerged as a transformative force. This blog explores the pivotal role these technologies play in the DevOps journey, unlocking new possibilities and efficiencies for software delivery.
What's new and upcoming in Azure Event Grid - George Guirguis
Functions, power up your troubleshooting toolkit! | Netdata Office Hours #9
7 Ways to Optimize Kubernetes Workloads for Efficiency
2bcloud Appoints Hemant Javeri as New Global Head of Solution Architecture
Landing safely with Azure Integration Services - Dan Toomey
See how Kleinschmidt achieved centralized visibility for their Azure environment. #azuremonitoring
Learn more about Serverless360 - Azure monitoring tool, start a free trial today at: https://bit.ly/47ULrFl
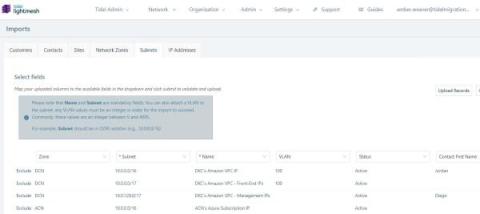
Streamlined Subnet Imports and Collaborative Support Teams
Discover LightMesh’s latest IP address management upgrades, featuring streamlined subnet imports and collaborative Support Teams, transforming network efficiency. Exciting news from LightMesh! We’ve enhanced our IP address management (IPAM) solution, offering powerful upgrades for efficient network management.
DevOps Vs Platform Engineering: Is There a Difference?
Navigating Security Challenges in Kubernetes Orchestration Platforms
As Kubernetes solidifies its position as the standard for container orchestration, it’s imperative to examine the associated security challenges. Kubernetes brings powerful capabilities to the enterprise and introduces new attack vectors and potential vulnerabilities. Here at Kublr, we sat down with our best experts to discuss how our team solves security challenges and how Kublr helps clients mitigate them.
Turkeys, Tech, and Table Settings: A Humorous Guide to IT Security at Thanksgiving Dinner
Let’s set the table a bit. As you know, in the U.S., Thanksgiving is coming up. And recently I had a conversation with my 83-year-old mother about Thanksgiving. Of course, we came across the inevitable parallels between Thanksgiving dinner and network security! That’s what you would be thinking when talking about Thanksgiving dinner with someone right? Before we dive into the feast, let me set the table.
Better when closer: the role of the data centre in your network
For those who remember the tech world before the COVID digitalisation gold-rush, the 2019 assertion by Gartner that 'The Data Centre Is (Almost) Dead, ruffled feathers. The report warned that by 2025, 80% of enterprises will shut down their traditional data centres. In fact, 10% of organisations already have. Then the pandemic hit and the global demand for world-class user experiences (for workforces and customers alike) exploded.
A Quick Guide To Google Cloud Platform (GCP) Tools
Mitigating Cloud Environmental Impact with Kepler, Kube Green, and Beyond - Navigate Europe 23
Kasten's Guide: Scaling Kubernetes Efficiently - KubeCon NA 23 Insights - Civo TV
Canonical releases Charmed Kubeflow 1.8
Azure Key Vault Certificate Expiration Monitoring
AI and the evolution of learning: Insights from Coding with Lewis
[Webinar] Optimize Your Infrastructure for Black Friday and Beyond
Resilience Engineering in 2024: Challenges, Trends, & Priorities
How to Mock gRPC APIs
Multi-Cluster Observability Part 1: Building A Foundation
In the world of modern Kubernetes, things have come a long way from the days of a single cluster handling one app. Now, it's common to see setups that span multiple clusters across different clouds. Initially, managing those clusters was a complicated operation with many moving parts. Using tools such as SUSE Rancher, RedHat OpenShift or AWS EKS, made managing multiple clusters somewhat easier.
Top 5 Financial Services Trends IT Leaders Must Know to Accelerate Digital Transformation
We could probably sum up the direction the financial services industry is headed in just two words: digital transformation. It’s the buzzy, all-encompassing focus and end goal of financial services organizations near and far, and it’s the big reason why many organizations are thinking about process automation with a greater sense of urgency.
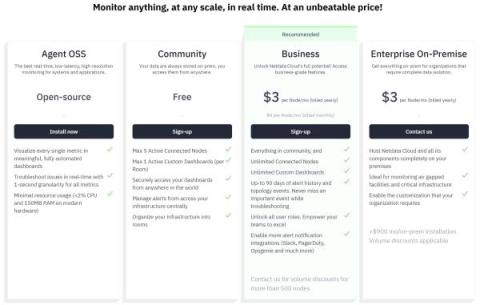
SaaS Monitoring with Levitate
Demystifying FEDRAMP and NIST for Continuous Compliance
Today, federal agencies rely extensively on Cloud-based SaaS applications for everything from payment processing and document management, to data security and employee workflow automation. These tools help departments to function very efficiently, but because they are being used for essential government functions, it’s vital that they are safe and secure. For example, personnel at The Pentagon or The Department of Homeland Security can’t just choose any software vendor in the marketplace.
Deploy a containerized .NET Core app to Azure Kubernetes Service (AKS)
Microsoft Azure provides an all-encompassing service that allows you to host Docker containers on the Azure Container Registry (ACR), deploy to a production-ready Kubernetes cluster via the Azure Kubernetes Service (AKS), and more. Using CircleCI, you can automatically deploy updates to your application, providing a safer and more efficient CI/CD process for managing your software. This article shows you how to automate deployments for a.Net application to Azure Kubernetes.
15 Crucial Azure Tools You Need To Know Now
Engineering-Led Optimization: How To Proactively Manage Cloud Costs Without Slowing Down Innovation
ISO 27001 Compliance: Everything You Need to Know
Let’s talk about what ISO 27001 compliance means for the tech team. If you’re a CTO, DevOps team lead, or cyber security specialist, you’ll have a lot of plates spinning at any given point in time. You need to ensure and maintain security protocols and compliance without hindering the development team’s ability to test and deploy new code (often at scale). It’s a constant battle to align development speed with governance tasks like audit, compliance, and security.
Weathering Black Friday and Other Storms Reliably
Ubuntu Explained: How to ensure security and stability in cloud instances-part 2
Cloud backup: improve your disaster recovery plans
The only way to measure developer productivity without causing a revolt
Should data teams consider incident management tools to respond to pipeline issues?
Data teams are adopting more processes and tools that align with software engineering, and from talks at the dbt Coalesce conference in 2023, there’s clearly a big push towards adopting software engineering practices at enterprise scale companies. At the moment, there are a lot of tools in the data space for identifying errors in data pipelines, but no tools for responding to these errors, such as coordinating fixes. This is exactly where an incident management platform makes sense to implement.
Scaling Engineering Teams
The software engineering world has become a place where compute, storage, and availability have become the cornerstones of scale. As an industry and as individuals, we should stop to take a closer look at scaling the most important of all resources… our people. In this post I’ve modeled a team with 6 engineers, 2 Sr, 3 Mid, and 1 Jr. This team is getting 450 “units” of work done ( where a unit is just some measure of throughput ) per interval (2 months).
GraphQL at scale with Azure API Management - Toon Vanhoutte
How to effectively monitor PowerShell Jobs running on VM or Azure?
IPO Growth: Scaling Engineering Orgs with Marty Weiner & Nick Caldwell - Navigate Europe 23
Getting Started with Istio with Marino Wijay Insights from KubeCon NA 2023 - Civo TV
Guide To Best Incident Management Software
Why every user can now fly first class with Flyway
3 Simple EC2 Strategies To Ensure Cost Efficiency
What is a Remote Repository? #shortsvideo #shorts #coding
What is CI/CD observability, and how are we paving the way for more observable pipelines?
Observability isn’t just about watching for errors or monitoring for basic health signals. Instead, it goes deeper so you can understand the “why” behind the behaviors within your system. CI/CD observability plays a key part in that. It’s about gaining an in-depth view of the entire pipeline of your continuous integration and deployment systems — looking at every code check-in, every test, every build, and every deployment.
From Cloud to AI: The Evolution of IT Infrastructure
Captains Log: How we are leveraging CEL for Signals
As engineers, we didn't want to make Signals only a replacement for what the existing incumbents do today. We've had our own gripes for years about the information architecture many old companies still force you to implement today. You should be able to send us any signal from any data source and create an alert based on some conditions. We're no strangers to building features that include conditional logic, but we upped the ante when it came to Signals.
Deploy with Slack
Ship code via Slack approvals
Kublr Release 1.27
Kublr team is happy to announce the new release 1.27, which we have been carefully crafting in previous months. At Kublr, we support six different versions of Kubernetes and a bunch of different clouds, so our team is focused on thoroughly testing each changed component and maintaining backward compatibility.
Demo: running Ubuntu Core on Intel IoT platforms
Does Your API Need a REST? Check Out GraphQL
Real time event stream processing and analytics - Kevin Lam and Ajeta Singhal
Azure Integration Account Certificate Expiration Monitoring
Unlocking Career Wisdom with Kelsey Hightower - Navigate Europe 23
Latest Innovations and Projects by the Civo Team at KubeCon NA 23 - Civo TV
The pocket guide to engineering metrics
Access Control: Key Strategies for System Security - Insights from KubeCon NA 2023 - Civo TV
Onward a Continuously Updated Kubernetes Marketplace by Olivier Vernin - Navigate Europe 23
Software Test Automation: Benefits, Use Cases, and Choosing the Right Tools
The Limitations of Microsoft Teams
Microsoft Teams has emerged as a cornerstone of modern workplace collaboration, offering a suite of tools designed to streamline communication and project management. Despite its widespread adoption, it’s crucial to acknowledge that no platform is without its limitations. Understanding these constraints is essential for organizations to navigate potential roadblocks effectively and make informed decisions about their communication infrastructure.
Building Cloud-Ready Applications
Deployment Frequency (DF) Explained
Why C and C++ programmers should use a package manager
Discover the risks and drawbacks of developing and distributing software without the support of a C++ package manager.
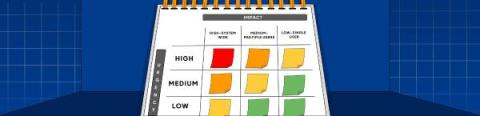
Incident Priority Matrix: A Comprehensive Guide
When multiple users are affected by an incident, it can quickly escalate into a chaotic situation. To effectively manage and prioritize such incidents, organizations need a robust incident priority matrix. An incident priority matrix is a tool organizations use to deal with critical issues quickly. It’s a roadmap for handling incidents efficiently.
Strengthen operational resilience with Service Chain Mapping. Watch our 60 second overview.
Moving MongoDB Workloads to Postgres with FerretDB with Peter Farkas - Navigate Europe 23
Optimizing your Kubernetes Costs with Finout - Insights from KubeCon NA 23 - Civo TV
ML for software engineers ft. Gideon Mendels of Comet ML
How to automate Snyk container scanning of your production environments
If you’re using containers to deploy your software, it is important to be aware of potential vulnerabilities within your container images. These may be introduced through dependencies in your built image, or perhaps through dependencies within the base image(s) used to build your image.
Cortex awarded 2023 Innovation Leader for Internal Developer Portals
Optimizing Data Management with Azure Files Snapshots
Introduction Azure Files snapshots are a crucial component in the landscape of cloud computing, offering robust solutions for data protection and management. These snapshots capture the exact state of SMB file shares at distinct moments, providing a critical safety net against data loss and corruption. Understanding their functionality and proper utilization is essential for any organization leveraging Azure cloud services for file storage and management.
Resolve Systems Recognized as a Representative Vendor in the 2023 Gartner Market Guide for Network Automation Platforms
Gartner®, in its latest Market Guide for Network Automation Platforms released November 2023, followed the company’s track record of research that provides recommendations to industry leaders, showcases market trends, and shares next-level automation insights.
Power Automate Monitoring
Apache Kafka Real Time Personalisation
Implementing edge computing for V2X use cases in automotive
Beta Announcement: Bring Your Own Kubernetes with Qovery
AI Explainer: What Are Neural Networks?
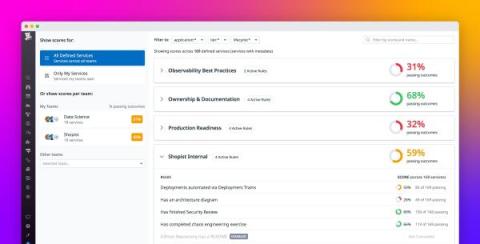
Introducing Custom Reliability Test Suites, Scoring and Dashboards
Security - A Pillar of Reliability
Terraform Time | Automate incident response using PagerDuty Incident Workflows
NVIDIA H200 Power Requirements: Can Your Racks Support Them?
This week, NVIDIA unveiled what they are calling “the world’s most powerful GPU for supercharging AI and HPC workloads,” the H200 Tensor Core GPU. There is much hype around the H200 as it is the first GPU with HBM3e. The larger and faster memory will further enable generative AI, large language models, and advance scientific computing for HPC workloads. Read the NVIDIA press release.
Goodbye, GitOps: Getting to green in an AI-powered world
The cognitive bias known as the streetlight effect describes our desire as humans to look for clues where it’s easiest to search, regardless of whether that’s where the answers are. For decades in the software industry, we’ve focused on testing our applications under the reassuring streetlight of GitOps. It made sense in theory: wait for changes to the codebase made by engineers, then trigger a re-test of your code. If your tests pass, you’re good to go.
How To Create a DevOps Implementation Roadmap
You’ve done your research and decided to use the DevOps approach for your software development process and IT operations. However, before you start tossing around terms like “continuous integration” and “containerization,” there’s an important starting point on your DevOps journey — creating a DevOps implementation roadmap.
Infrastructure Management & Lifecycle Explained
Unleash the potential of intelligent, context-aware automation with BigPanda and Ansible
Many ITOps organizations we speak with want a state of self-healing systems capable of identifying and resolving issues without human intervention. Thanks to the progress in AI and ML, AIOps has made significant advancements in areas that automate many of the steps involved with identifying and triaging incidents. We ask ITOps leaders why they aren’t taking the next step with auto-remediating incident response workflows.
The Power of LowOps
I'm Konner, a Strategic Sales Executive here at Cycle.io. With a background rooted in DevOps and CI/CD, I've dedicated over three years to engaging with developers and the DevOps community, consistently learning and gaining insights from each conversation.
How software company security priorities are changing
The cyberthreat landscape continues to change along with technological advancements. Industry thought leaders expect to see changes in software companies’ approach to security and the defenses they put in place to protect their businesses and their users. Here are five of developers’ cybersecurity priorities for 2023 and predictions for how software companies will adapt their processes to address them.
How to unlock your leadership potential on a cloud migration project: A guide for the DBA, part 1
What is Git Pull? #shorts #shortsvideo #git
Proactive monitoring with automated alerts
Transform Your Kubernetes Troubleshooting With Powerful Data Correlations
Mastering Multi-Cloud Management: Advanced Tagging, Expense Monitoring, and Resource Visualization
Serverless & Chill: Stressfree Container Hosting by Steve Judd - Navigate Europe 23
Platform Engineering: Insights from Giant Swarm at KubeCon NA 23 - Civo TV
Product Release Notes October 2023
Deploy and manage AI workloads on Scaleway infrastructure with CircleCI
With automation and CI/CD practices, the entire AI workflow can be run and monitored efficiently, often by a single expert. Still, running AI/ML on GPU instances has its challenges. This tutorial shows you how to meet those challenges using the control and flexibility of CircleCI runners combined with Scaleway, a powerful cloud ecosystem for building, training, and deploying applications at scale.
Optimize your MLOps pipelines with inbound webhooks
In a traditional DevOps implementation, you automate the build, test, release, and deploy process by setting up a CI/CD workflow that runs whenever a change is committed to a code repository. This approach is also useful in MLOps: If you make changes to your machine learning logic in your code, it can trigger your workflow. But what about changes that happen outside of your code repository?
Ep 9: The Power of Lightweight Endpoint Security featuring Zach Wasserman
Mattermost v9.2 Changelog
AWS Region vs Availability Zone: What is the Difference?
The Challenges of Collecting Runtime Data
Collecting data in real-time plays a crucial role in securing, monitoring, and troubleshooting applications. This real-time data, often referred to as ‘runtime data,’ provides unique insights into the application’s behavior, which aren’t available through other collection techniques. But the tricky part is that collecting runtime data comes with challenges.
Navigating the Migration to SharePoint
In the realm of digital transformation, migrating to SharePoint stands out as a pivotal step for organizations seeking to enhance collaboration, streamline data management, and boost operational efficiency. SharePoint, a robust platform by Microsoft, offers a plethora of features that cater to diverse business needs, from document management to team collaboration.
System Center Orchestrator to Azure Automation Migration Guide
For companies using Microsoft System Center Orchestrator versions 2016, 2019 or earlier who are looking for a replacement for their aging Orchestrator systems, they have an option to migrate to a new 64 bit version Orchestrator 2022 (more details on this can be found in the Kelverion Orchestrator Best Practices Guide) but many companies are considering replacing their Orchestrator system entirely and are looking for guidance.
Canonical unveils MicroCloud
Innovate at speed with open source AI
How to ensure business continuity with IT infrastructure support
Understanding Zero-Day Vulnerabilities in Software Supply Chain
Deploy a Node app on AWS EC2 Linux
Amazon Web Services (AWS) provides a vast ecosystem of products that make DevOps an absolute dream. Products like AWS Elastic Beanstalk have ready-made services for autoscaling, deployment, and logging (to name a few). However, teams may prefer to take a barebones approach and build incrementally - in which case AWS Elastic Compute Cloud (EC2) would be the preferred option.
Batch comments in Bitbucket Cloud code review | Bitbucket Cloud demos | Atlassian
What is DevOps? Grafana for Beginners Ep.2
10 Practical Machine Learning Use Cases in Observability - Navigate Europe 23
Kubernetes Security Challenges with Armo - Insights from KubeCon NA 2023 - Civo TV
What to Expect from Your Application Platform
How companies have saved millions by adopting cloud FinOps at scale
How To Save Money On Your Observability Costs
In today's digital age, the complexity and scope of dynamic system architectures are expanding at an unprecedented rate. As a result, IT teams find themselves grappling with the challenge of monitoring and addressing conditions across multi-cloud environments. With the increasing complexities, IT operations, DevOps, and SRE teams are searching for enhanced observability within these multifaceted computing environments.
Modeling and Unifying DevOps Data Part 3: Pipelines
When AWS Won't Work: 10 AWS Alternatives Worth Considering Now
Understanding Software Development Sprint Health With Backlog View in Team Insights for Jira
How Migration and Modernization Minimize Environmental Impact
Businesses are prioritizing sustainability to minimize their environmental impact. Since we started, we’ve completed over 130 migration projects with regional and international customers. These projects generally involve right-sizing resources, moving to major cloud providers like Microsoft Azure and Amazon Web Services, and modernizing applications.
DevOps Automation and DevOps Best Practices
In the dynamic landscape of software development, the adoption of DevOps has become a cornerstone for organizations aiming to deliver high-quality products at a rapid pace. DevOps, a fusion of development and operations, emphasizes collaboration, communication, and automation throughout the entire software development lifecycle.
Hot topics from KubeCon North America 2023
As another year at KubeCon + CloudNativeCon (CNC) draws to a close, the latest installment in Chicago might be one of our favorite ones so far! With talks having an ever greater focus on the impact of sustainability and inclusion within the community, we loved getting involved in the conversation about how we can make the cloud a better solution for all.
Deploy and re-evaluate LLM-powered apps with LangSmith and CircleCI
In part 1 of this tutorial, we showed you how to build a large language model (LLM) application that uses retrieval-augmented generation (RAG) to query your own documentation and then test it using a CircleCI continuous integration (CI) pipeline.
You Don't Need Kubernetes to Be Cloud Native
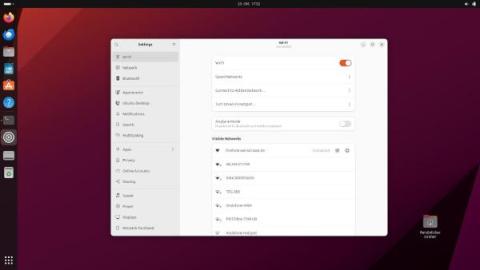
Netplan brings consistent network configuration across Desktop, Server, Cloud and IoT
4 Reasons Why NOCs Need Incident Response Automation
Incident response in a Network Operations Center (NOC) is cumbersome and time-consuming. There are many steps, many sources where incidents come from, and a long, long list of complexities involved. For instance, for incident response with a NOC, there’s the initial monitoring – Tier 1 functions of “eyes on glass” work of looking at alerts coming in and what they’re for, such as a security breach, performance issue, a hardware failure, among others.
Databases: Cloud-Native Modernization with David Walker - Navigate Europe 23
Exploring CNCF's Latest Certifications - Insights from KubeCon NA 23 - Civo TV
Driving Efficiency and Advanced Insight - Explore Virtana's Latest Innovations
Virtana is proud to announce a series of new capabilities focused on empowering our customers with advanced AI-driven capabilities, enhanced user interfaces, and deeper integrations, all aimed at optimizing application and infrastructure observability. Let’s dive into these innovations and see how they revolutionize the way IT professionals interact with their environments.
What is subsetting, what are the advantages, and how does it make test data management easier?
Demo: New AI plugin interface improvements
Microsoft Teams New Release 8 Great Tips for Using the New Teams
Ribbon has multiple solutions for Microsoft Teams Calling - https://ribboncommunications.com/solutions/enterprise-solutions/microsoft-solutions-teams-direct-routing
How to Access Powerful IDEs and Containers on Any Device with Rizel Scarlett #shorts #shortsvideo
The Power of Fusion: Enhancing Productivity with Jira Git Integration Insights
If your team has ever struggled with seamlessly integrating Git and Jira, you’re not alone. Managing code repositories, tracking issues, and streamlining workflows can be challenging. Git Integration for Jira combines the power of Git and Jira, enabling development teams to collaborate more efficiently. In this article, we’ll explore the features and benefits of Git Integration for Jira, how it bridges the gap between Git and Jira, and how it can improve your development process.
Incident management really can be for everyone
Incident management tools are often built for engineers to solve technical issues. On the surface, thinking of incident management as an engineering problem makes sense, and it’s an approach that’s widely used by many organizations from small startups to large enterprises. When there's a problem like a checkout page failure or a server crash, it’s natural for engineers to spring into action, declaring and resolving these incidents.
New in pull requests: Batched comments
Azure Logic Apps Monitoring
KubeCon NA 2023: Celebrating Innovation and the K8s Community
The sun has officially set on KubeCon North America 2023, but the CNCF's flagship event has left a lasting impression on us. Roughly 9,000 Kubernetes enthusiasts descended on Chicago's McCormick Place West to see the K8s community's latest innovations. DevOps professionals, engineers, and architects alike were eager to share and boost their K8s knowledge. Overall, HAProxy joined over 250 other sponsor organizations to celebrate open-source, cloud-native technologies over four activity-packed days.
Out-of-band communication: Maintaining business continuity
Today, most organizations rely on several different secure communication mediums — like email, real-time chat, video calls, and SMS — to transmit information, collaborate, and keep teams aligned. While modern communication tools help teams stay connected, the digital landscape is not without its challenges. For most organizations, it’s only a matter of time before network disruptions, security breaches, and system failures impact main lines of communication.
Serverless Workflows using Durable Functions and Logic Apps in Azure - Jonah Andersson
Bringing automation to telco edge clouds at scale
Introducing Workflows: Enhancing Automation to Incident Response
InoNet and Canonical partner for seamless Edge AI deployment
Why Automatic Cloud Cost Optimization Isn't Enough
Unlocking Git's Power with GitLens: A Visual Studio Code Extension Guide
In the dynamic world of software development, where collaboration and version control are paramount, it’s important to have the right tools to be able to support you. GitLens is a powerful Visual Studio Code extension that can help shed light on the intricacies of your Git workflow. In this blog post, we will introduce you to GitLens and some of its amazing features.
Succeeding with Backstage 3: Improving Adoption
This third installment of the “Succeeding with Backstage” series explores how you can improve the adoption of Backstage within your organization. The previous two parts dealt with customizing the look and feel of Backstage and creating and maintaining custom plugins.
Succeeding with Backstage 4: Backstage as Part of a Broader Developer Productivity Engineering (DPE) Initiative
This final article in the “Succeeding with Backstage” series focuses on how you can incorporate Backstage as part of a broader developer productivity engineering (DPE) initiative. The previous parts dealt with customizing the look and feel of Backstage, creating and maintaining custom plugins, and improving Backstage adoption.
Advanced Search Capabilities in SharePoint Online
When you enter a query in SharePoint Online‘s search box, you are tapping into a complex system designed to interpret your needs and retrieve the most relevant content. It’s a system built not only to understand what you’re looking for but also to respect the security and organization of your company’s data. By mastering SharePoint Online’s advanced search capabilities, you unlock the potential to transform vast data stores into actionable insights swiftly.
AI for Software Development | Dharmesh Shah: The Future of Software, GitKon 2023
Open Source Developer Portals
7 Most Common Pitfalls When Choosing the Right Internal Developer Platform
Forget Inbox Zero, try PR Zero!
Try PR zero
Treat reliability risks like security vulnerabilities by scanning and testing for them
Finding, prioritizing, and mitigating security vulnerabilities is an essential part of running software. We’ve all recognized that vulnerabilities exist and that new ones are introduced on a regular basis, so we make sure that we check for and remediate them on a regular basis. Even if the code passed all the security checks before being deployed, you still perform regular security tests to make sure everything’s secure.
International data protection with EU-entities of US-headquartered IaaS providers
The General Data Protection Regulation (GDPR), a legal mandate across the EU, requires enhanced protection for EU personal data transferred to countries with inadequate levels of data protection safeguards—including the US. The EU-US Privacy Shield, which was in place until 2020, facilitated these protections but was invalidated by the Schrems II ruling as a result of US surveillance concerns.
Overcoming Inconsistent Environments with Cycle
Maintaining a consistent environment from development to production is one of those challenges that's always easier said than done. It used to be that a small hiccup—like a version mismatch or a misconfigured setting—could have you scrambling to figure out why everything worked perfectly on your local machine but started falling apart elsewhere.
Career Ownership: The Open Source Way by Nikita Koselev - Navigate Europe 23
What do we Expect from the Future of Wasm by Fermyon at KubeCon NA 23 - Civo TV
What is a Pod? Kubernetes for Beginners
The Future of Serverless is AI WebAssembly by Matt Butcher - Navigate Europe 23
How to Automate Change Management for DevOps
Until fairly recently, software releases happened once or twice a year, maybe once a quarter. This gave IT teams plenty of time to verify and manually sign off on every change before they were released in big batches during a bank holiday weekend or off-peak hours. Typically, they’d produce paperwork to show that all changes had been properly tested, and then those changes would be approved for release in a change advisory board meeting (CAB).
OAuth 2.0 and OIDC Best Practices by Rajesh Muthusamy - Navigate Europe 23
Keeping Stakeholders Notified of Incidents With Squadcast
Enterprise Hosting: A solution for the ever-changing digital world
Having your websites and apps run smoothly at all times is crucial to the success of your brand, and having something go wrong can be catastrophic. But getting bogged down in all of the things that go into setting up and managing them is time-consuming and complicated—especially if your tech team's capabilities are on the lighter side. With an enterprise hosting solution, everything is handled for you. You get infrastructure, management, security, scaling, and more all rolled into one.
Making the most of bandwidth on-demand: What is flex bandwidth?
Creating Ephemeral Environments for CI/CD Pipelines with Kubernetes
A story about HTTP status codes and why you should read documentation
Since 2020, I’ve been working on an Express (Node.js framework) application to power viewer interactions and events that happen whilst I’m streaming live coding on Twitch — my Twitch bot. Since using Sentry for error monitoring and crashes using the Sentry Node SDK, I’ve already squashed quite a few bugs that were entirely a result of my own terrible code.
Finally Revealed: The New Insights Driving Peak Dev Productivity with Kevin Bost & Jeff Schinella
When Workflows Don't Feel like Work: A Lesson in Simplifying PRs with Jason Gates & Jonathan Silva
The Time Capsule: Code History Deciphered with GitLens with Chuck, Melese & Keith
How Much Does Remote Access Software Cost?
Remote access software has risen to prominence as a vital tool, enabling organizations to bridge geographical distances and empower remote workforces. However, as businesses embrace the convenience and flexibility that remote access solutions offer, they are also confronted with an essential consideration: understanding the true cost of remote access software. In this article, we embark on a comprehensive exploration of the financial dimensions surrounding remote access solutions.
K8s Exercise Labels and Annotations
Kubernetes, often abbreviated as K8s, has revolutionised the way we manage containerized applications. It provides a robust platform for orchestrating and managing containers at scale. One of the key features that sets Kubernetes apart is its powerful metadata system, which includes labels and annotations. In this blog post, we’ll take a comprehensive look at how labels and annotations work in Kubernetes and how you can leverage them to enhance the management of your applications.
What is MLflow?
Succeeding with Backstage 2: Building and Maintaining Custom Plugins
This second installment of the “Succeeding with Backstage” explains how to create a custom Backstage plugin. For many use cases, customizing the platform’s look using the methods from the last part and integrating existing plugins will be enough to align Backstage with your organization’s needs. But what happens when the plugin directory doesn’t have a plugin that solves your particular problem? You create a custom plugin, of course.
Succeeding with Backstage 1: Customizing the Look and Feel of Backstage
This is the first article in the “Succeeding with Backstage” series. This series is for those with a working Backstage implementation who want to ensure smooth adoption and ongoing successful use of the tool. If you’re still trying to decide if Backstage is for you, you can check out the first article in the “Evaluating Backstage” series.
Is Wasm Too Soon or Too Late by Ashwin Kumar Uppala - Navigate Europe 23
Azure Event Grid Monitoring and Alerting
Azure Logic Apps deep dive - Slava Koltovich and Wagner Silveira
Platform.sh Welcomes Two New C-Level Executives; Chief Financial Officer, Caroline Bec Cox, and Chief People Officer, Caroline Leroy
6 Golang Testing Frameworks for Every Type of Test
What's New in Serverless360: Azure SQL Elastic Pool Support, Monitor Virtual Network Gateway & more
AI Explainer: What Are Reinforcement Learning 'Rewards'?
Cycle vs. Kubernetes: Why I See Organizations Making the Switch
Greetings! My name is Matt Krauser and I’m a Strategic Sales Executive here at Cycle. After participating in nearly a hundred demos of the platform, I wanted to step back from my day to day grind and share a little about my experience thus far. My goal in writing this is to compare Cycle and Kubernetes, discuss the primary pain points I hear from prospects and K8s users on a daily basis, and explain how Cycle can alleviate these challenges.
Enrich Kubernetes with New Deployment Tracking Capability
When things go wrong, we’d all love the ability to go back in time, return things to the way they were, and fix whatever issues pop up at the start so they never happen in the first place. This is no different when maintaining complex microservices-based architectures. With any complex system, things are bound to go wrong from time to time.
The Advanced Features of SharePoint Online
In the labyrinthine corridors of modern enterprise software, SharePoint Online stands as a beacon of collaboration and efficiency. It’s not just a tool; it’s a multifaceted platform that has been meticulously refined to meet the multifarious demands of today’s businesses.
Cortex Initiatives: When scorecards need a deadline
More is More - A Case for Dynamic Observability
Dynamic observability is the concept that the amount of data collected should scale based on signals from your environment. Elastic infrastructure is not a new concept. Much of the internet is powered by services that provision more resources based on signals derived from metrics like cpu load, memory utilization and queue depth. If we can use tools to right size our infrastructure, why can’t we also use tools to right size the amount of data we collect?
Unleashing the Power of Network Innovation in Healthcare
OpenTelemetry vs. OpenCensus
Why Implementing App Security Can Lead To Spiraling Costs
Robust app security is non-negotiable, but the spiraling costs that can come with it are. In the context of application delivery, security plays a pivotal role in maintaining business continuity, protecting sensitive data, and upholding a solid reputation. However, the journey to build a formidable defense at the load balancing and reverse proxy layer can quickly become costly with a few wrong turns. Security is important, but buyers don’t have to break the bank to implement it.
Creating Ephemeral Environments for CI/CD Pipelines with Kubernetes and Qovery
Treating Company Culture as a Product with HubSpot's Dharmesh Shah #GitKon #startups #interview
Peek into the Palantir: GitKraken's Vision for the Future of Developer Experience ft. Justin Roberts
DevSecOps the VMware Way
Modernize as You Migrate: Scale Your Migration Teams with JIRA Integration and Project Templates
Webinar: Managing High Cardinality Workshop
Router Monitoring with Grafana
Routers are essential for connecting devices. Routers decide where the internet goes and how fast it should be. Because they play such a crucial role, it's vital to keep an eye on them and make sure they're doing their job well. This act of keeping an eye on routers is what we call "router monitoring." Monitoring routers isn't just about checking how the routers are doing; it's about making sure the whole network works well.
Turbocharge your API and microservice delivery on MicroK8s with Microcks
What Is Server Virtualization?
Server virtualization is a transformative technology that has revolutionized data centers, streamlined operations, and enhanced efficiency. This guide aims to provide an understanding of server virtualization, its significance, benefits, and its pivotal role in modern IT environments.
What Is a Load Balancer?
In today’s hyper-competitive landscape, constant connection is vital for consumers, partners, and employees alike. Cloud-based architecture not only provides an elixir against downtime but is helping organizations unlock further streams of revenue. Today, the workload requirements of AI, application development and global service delivery have each individually been drivers for nearly 40% of multi-cloud adoption.
What BCDEdit Does and How To Use It
Every interaction with a Windows operating system begins with a successful boot process, paving the way for a stable user environment. Central to this process is the Boot Configuration Data (BCD) store, which houses the essential boot information that guides the system during the boot process. Managing this crucial data is the command-line utility BCDEdit, or “Boot Configuration Data Editor”.
High performing Engineering Teams and the Holy Grail by Zan Markan - Navigate Europe 23
BizTalk Server to Azure Integration Services migration - Sandro Pereira
The No-Nonsense Guide to Migrating On-Prem Deployments to the Cloud
Top 5 API Testing Tools & Methodologies
The Complete Traffic Capture and Replay Tutorial using Speedscale
What is Docker Network Host?
Docker is a platform as a service for deploying applications in Docker containers. Containers are software "packages" that bundle together an application's source code with its libraries, configurations, and dependencies, helping software run more consistently and reliably on different machines. To start using Docker containers, you need to be familiar with Docker networking. Below, we'll answer the question: "What is a Docker network host?".
Building a trust-centric culture for success
What’s important when building a new business? A good idea is vital, obviously, plus the right people, hard work, experienced investors, and so on. Building trust is important, but probably far down the list. It’s not that trust isn’t important, it’s just likely to be put aside while working on tasks that are perceived as more time-sensitive or of a higher priority, especially those which directly and noticeably impact the bottom line.
Getting started with PostgreSQL for SQL Server Developers | PostgreSQL 101
Comparing SQL Server and PostgreSQL | PostgreSQL 101
Trusted open source for everyone
Captains Log: A first look at our architecture for Signals
Welcome to the first Signals Captain’s Log! My name is Robert, and I’m a recovering on-call engineer and the CEO of FireHydrant. When we started our journey of building Signals, a viable replacement for PagerDuty, OpsGenie, etc, we decided very early that we would tell everyone what makes Signals unique, and what better way than to tell you how we’re building it (without revealing too much 😉). Let’s jump in.
Solving Common System Center Orchestrator Problems
Sometimes, when building Runbooks in Orchestrator, it can feel like you’ve hit a dead end with no way to achieve the functionality or automation you require. For newer users, Orchestrator can be daunting because it is a completely blank canvas; there are no sample runbooks included or out-of-the-box automations. In addition, with a shift in focus to cloud automation, there is limited guidance and ‘how to’ advice available to help users.
Downsampling & Aggregating Metrics in Prometheus: Practical Strategies to Manage Cardinality and Query Performance
Git leaks, FTW
Azure Service Bus Monitoring and Alerting
Event Hubs Kafka and event streaming at high speed - Kasun Indrasiri and Steve Gennard
Software Development Life Cycle: Day 1 Best Practices
5 AWS Tagging Challenges - And How CloudZero Solves Them
ITIM and the Public Sector: How Network Monitoring Rises to the Challenge
Government agencies and public sector organizations are a tantalizing hacker target. Cybercriminals go after public sector organizations because they hold confidential, often classified, information – the exact data state-sponsored and other criminal groups salivate over. The Cybersecurity and Infrastructure Security Agency, or CISA, along with the United States Computer Emergency Readiness Team, or CERT, have warned public sector IT of key threats.
Formalize your organization's best practices with custom Scorecards in Datadog
The Datadog Service Catalog is a centralized hub of information around the performance, reliability, security, efficiency, and ownership of your distributed services. By using the Service Catalog, teams can eliminate knowledge silos and realize seamless DevSecOps workflows.
Canonical joins Open Networking Foundation
The New SEC Rules and You
Why Databases Don't Cloud Well and What To Do About It by David Stokes - Navigate Europe 23
The pivotal role of network automation software in your network environment
Today, automation has shifted from being a luxury to an absolute necessity, especially within the realm of networks. This shift is driven by the rapid evolution of network technologies, compliance standards, and evolving business needs, placing an increasingly daunting burden on network administrators to manage these tasks manually.
AR Meets DCIM: A New Age in Data Center Management
What is a Pragmatic DevOps Engineer?
CloudZero's New Logo: A Commitment To Finding Order Within The Chaos
Mastering Root Cause Analysis: A Guide for Site Reliability Engineers
Site Reliability Engineers (SREs) play a vital role in ensuring the stability and performance of web services and are key in incident management. One of the core skills SREs need is the ability to conduct effective Root Cause Analysis (RCA) when issues arise. This guide is about how to improve your RCA skills for more effective post-incident analysis.Let's dive in.🔖 What is Prometheus Alertmanager? Read here!
Achieve Optimal Performance with Nginx and Micro-Caching
The word "cache" is used in many different contexts. Typically, a cache is a small chunk of data stored locally for quick access. In this case, it’s about computer caches, i.e., the data stored in memory. Micro-caching is a technique where a programmer uses this cached data to do some quick computations, which can lead to some amazing solutions. In micro caching, dynamically generated content is cached for only a brief period rather than full-page caching.
Value Stream Management: A Brief Explainer
3Pillar Global picks Mattermost for open source adaptability
As a software product company that helps customers bring new products to market, 3Pillar Global relies on tight-knit coordination and communication to move projects forward. When the team was looking for a new collaboration solution that would enable them to communicate in real time, they looked for an open source option.
Unveiling Rancher 2.8 and Rancher Prime 2.0: Advancing Interoperability and Efficiency
The Rancher by SUSE team has been dedicated to fortifying the Rancher platform to be the most interoperable and adaptable platform for our customers and the wider community over the past year. In late 2022, we introduced the ‘Extensions Catalog.’, and earlier this year at KubeCon Europe in Amsterdam, we revealed our Rancher UI Extensions framework. Continuing this momentum, we are thrilled to announce the release of Rancher 2.8 and Rancher Prime 2.0.
Real world examples of Business Activity Monitoring with Serverless360 - Michael Stephenson
Connect to AWS in 60 Seconds
Innovating on Azure: How Spot by NetApp is the one Spot for automating and optimizing your Azure infrastructure
Build and evaluate LLM-powered apps with LangChain and CircleCI
Generative AI has already shown its huge potential, but there are many applications that out-of-the-box large language model (LLM) solutions aren’t suitable for. These include enterprise-level applications like summarizing your own internal notes and answering questions about internal data and documents, as well as applications like running queries on your own data to equip the AI with known facts (reducing “hallucinations” and improving outcomes).
The Art of Event-Driven Observability with OpenTelemetry with Henrik Rexed - Navigate Europe 23
Cilium + eBPF Community Unveils Thrilling Developments at KubeCon NA 2023 - Civo TV
Configuration Drift: How It Happens, Top Sources + How to Stop It for Good
It Never Goes to Plan: How to Adapt When Facing the Unknown with Kyle Fransham and Adam Wride
Common Datadog Errors and What to Do About Them
Datadog is one of the most known tools for monitoring. It’s widely popular for its single pane of glass solution. However, many people have complaints about Datadog. One example of an issue many people have with using Datadog is the number of errors people find when getting started.
4 Important IT Automations Explained for Success in 2024
It’s safe to assume that planning ahead is everything to business leaders right now, as the start of 2024 is right around the corner. It’s a strategy-backed priority to get proactive and ahead of challenges that might be ahead of us. As IT’s role in driving business success continues to expand, putting automation to work inside of IT departments and functions today better positions organizations to reach goals and overcome future obstacles.
A guide to PostgreSQL documentation and useful resources | PostgreSQL 101
Why PostgreSQL in 2023 | PostgreSQL 101
The Journey Towards PostgreSQL - Tips and Lessons | PostgreSQL 101
10 PostgreSQL extensions you need to know about | PostgreSQL 101
Software Observability from the Lens of Radar and a Black Box
For the Kubernetes Value Line Look to Open Source Innovation
Kubernetes has emerged as a transformative force, reshaping the way organizations develop, deploy, and manage applications. Adoption of containers and Kubernetes has ballooned in the past years, as heralded by everyone from the Cloud Native Computing Foundation (CNCF) itself, to the vendors offering their Kubernetes wares, to the research firms that track trends in enterprise technology adoption.
Fullstack Preview Environments with Neon and Qovery
Mastering Open Source Security: Your Guide to S2C2F
Welcome to our 2nd blog in our series on how to securely consume Open Source Software (OSS). Attacks targeting OSS are on the rise, making the security of your software supply chain a top priority. The 1st blog gave an overview of some of the most common types of attacks. Today we’ll explore the Secure Supply Chain Consumption Framework (S2C2F) that can help you mitigate against these attacks.
AI Explainer: What Are Generative Adversarial Networks?
A Simple Guide To AWS Lambda Rightsizing
Stop bugging devs for PR NITs
How I stopped bugging devs for PR format NITs
Rancher Desktop 1.11: Introducing Snapshots, Container Dashboard and More
We are delighted to announce the release of Rancher Desktop 1.11.0! This update comes with new features, Snapshots and the Container Dashboard, along with other important bug fixes.
Kubernetes Clusters: Everything You Need To Know
Kubernetes is an open-source container orchestration platform that automates the deployment, scaling, and management of containerized applications. It allows you to create and manage clusters of machines, called Kubernetes clusters, to run your applications in a scalable and highly available manner. Kubernetes clusters provide a distributed and scalable platform for running containerized workloads.
AIOps in DevOps: Advantages, Obstacles, and Best Strategies
AIOps for DevOps. This is a phrase that you’ll hear a lot often in the coming years. Leveraging AIOps is becoming an emerging practice for DevOps. And why not? After all, AIOps offers so many benefits for DevOps, making it a must have for every business. But what exactly are these benefits? To know more, keep reading this blog where we will discuss everything about AIOps for DevOps including its.
Modernising the supply chain with Logic Apps and EDI - Martin Abbot & Bill Chestnut
Mastering Prometheus Relabeling: A Comprehensive Guide
Multi Cluster Observability With Service Mesh by Ryota Sawada - Navigate Europe 23
GCP Vs. Azure: Choosing the Best Cloud Provider for Your Needs
Kubernetes Scheduler - A Comprehensive Guide
In the world of Kubernetes, where applications are encapsulated within containers and seamlessly distributed across diverse clusters of computers, the enigmatic Kubernetes scheduler takes centre stage. Think of it as the orchestra conductor of your Kubernetes cluster, orchestrating a symphony of resources to ensure seamless operations. This unassuming yet powerful component leverages a sophisticated algorithm to perform the intricate dance of optimizing resource allocation.
Computer Vision at the Edge with K3s and NNAs with Sergio Méndez - Navigate Europe 23
Why Cloud-Based Solutions Could Be the Right Move for Your Health Business
How We Speed Up Deployments By 30%
Fullstack Preview Environments with Neon and Qovery
Understanding the Netdata Methodology: A Different Take on Monitoring
In the dynamic landscape of modern infrastructure and multi cloud environments, observing and understanding system performance requires a new breed of tools—ones that keep pace with the 'living' nature of modern infrastructure. This is the inflection point at which Netdata steps in, and aims to bring a fresh perspective to monitoring.
Evolving Gateway API from the Cloud to On-prem & the Edge - Navigate Europe 23
Suppressing Alert Noise during Scheduled Maintenance
Kubernetes Load Balancers: A Beginner's Guide
In the earlier days of the internet, organizations faced resource allocation challenges when running applications on physical servers. They initially resorted to running individual applications on separate physical servers, which was costly and not scalable. As the internet continued to evolve, organizations sought more efficient ways to manage their applications and workloads.
Adopt a 'GDPR everywhere' strategy
Companies used to have an easier time complying with regulations, but compliance has really never been a straightforward endeavor. In the past, there was one set of rules for businesses to obey, the local rules in the place where companies do business. If the business expanded into new parts of the world, they would have to comply with new rules, but these would apply only to those new territories. The global economy means an end to this approach.
Building a Culture of Reliability: Why SREs Can't Do It Alone
Deploy a Dockerized Spring Boot app to Azure App Service
Incompatible hardware is a common cause of application failures for distributed teams. Most teams depend on containerization tools like Docker to prevent these failures. But is there any way to automate the deployment of Docker images more efficiently and intuitively? In this article, I will show you how simple it is to do this by combining CircleCI and Microsoft Azure to build a CI/CD pipeline for a Dockerized Spring Boot project.
Metric Cardinality Explorer to understand and Manage High Cardinality
Introducing the World's First Dashboard for GitOps Environments
Defining multiple environments in Argo CD and promoting an application between them is one of most popular questions for companies that adopt GitOps for their applications. While we have offered several guidelines in the past for organizing your GitOps environments, today we are taking it further by announcing a complete product that helps you visualize the full lifecycle of an application as it moves through different stages. Meet the new Codefresh GitOps Environment Dashboard!
AWS vs Azure: Choosing the Best Cloud Provider for Your Needs
Server Monitoring with Graphite
Server monitoring is a crucial technique to learn these days to work efficiently with servers. It helps optimize the performance of a server and diagnose issues productively. One useful tool used these days is Graphite, which helps monitor a server’s performance and provides graphing solutions by gaining valuable insights into your server. You can explore MetricFire’s Hosted Graphite service today by signing up for a free trial or booking a demo session.
Top 10 Container Monitoring Tools
Containerization has significantly improved the way we deploy and manage applications over the past years. It has enabled agility, scalability, and efficiency in modern software development. However, the dynamic nature of containers requires robust monitoring solutions to ensure optimal performance and reliability. In this article, we will discuss the top 10 container monitoring tools that are essential for anyone navigating the containerized landscape.
Netdata Best Practices: Optimizing Your Monitoring Setup
Effective system monitoring is non-negotiable in today's complex IT environments. Netdata offers real-time performance and health monitoring with precision and granularity. But the key to harnessing its full potential lies in the optimization of your setup. Let’s ensure you are not just collecting data, but doing it in the most optimal way while gaining actionable insights from it. The starting point for optimization is a robust setup.
I've Made a Huge Mistake: Implementing Agile on Infrastructure Teams
Beyond Code: A Conversation with Sean Astin on Mental Health
CircleCI Product Roadmap Webinar
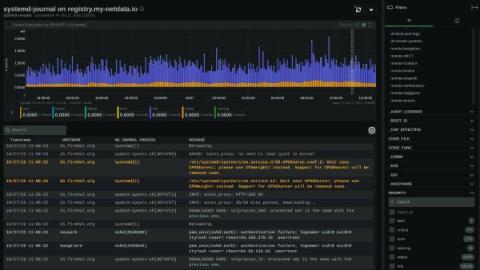
System Operators: Unlock Log Management Mastery with systemd-journal and Netdata
System operators know the drill: as the complexity of systems scales, so does the deluge of logs. Traditionally, taming this relentless tide demands a concoction of costly tools and laborious configurations—until now. The dynamic duo of systemd-journal and Netdata is revolutionizing log management, turning what was once a Herculean task into a streamlined, powerful, and surprisingly straightforward process.
How to use the View Mode to remote monitor my devices on AirDroid Business
Meet Cyber Essentials requirements with Ubuntu Pro
Using Azure App configuration with Azure Integration Services - Bill Chesnut
Exploring Open Source: Challenges, Ethics & Opportunities - Navigate Europe 23
Application Observability on RKE2 With SUSE Rancher and StackState
Container Security in DevOps: The Role of SSL/TLS Certificates
Staying Ahead of the Curve: Understanding the Latest Data Storage Technologies
Leveraging DevOps Principles for Streamlined SMS Campaigns
Status Pages That Deliver: Top 10 Favorites
11 facts about real-world container use
In this year’s report, we see how organizations are using containers not just to solve their day-to-day infrastructure needs. Rather, customers are exploring the next technology frontier of containers by building next-generation applications, enhancing developer productivity, and optimizing costs.
AI Explainer: What Is Data Cleaning?
Helios Runtime for AppSec: The missing link in application security
Modern development teams increasingly rely on open-source packages to rapidly build and deploy applications. In fact, most, if not all applications consist of far more open-source and 3rd-party code than the code that’s written by their dev teams.
Mastering Kubernetes Node Management with the `kubectl cordon` Command
For many developers and engineers, Kubernetes is the de facto choice for container orchestration. That’s primarily because of its efficiency in handling and scaling container workloads. However, the complexity of managing nodes in a Kubernetes cluster can cause recurring headaches for even the most experienced and skilled IT teams. This is where `kubectl cordon` comes into play.
Real-Time Canary Deployment Tracking with Argo CD & Levitate Change Events
Choosing A Container Platform
The journey to selecting a container platform is a fun and exciting time in any organization. Container technology abstracts away so many problems from cloud 1.0 VM based approach, and puts engineering teams back in the distributed drivers seat. As containers continue to mature and adoption becomes ubiquitous, there are many lessons to learn and ideas to consider before inevitably choosing Cycle. Let's take a look at Cycle alongside the other types of container platforms.
Status Pages 101: How to Create a Status Page You and Your Customers Will Actually Want to Use
This blog post is adapted from my talk at SRECon EMEA 2023 - original slides are available here! Status pages are a simple yet underutilized element of incident communication. Done well, they’re a low-lift way to keep your customers and stakeholders informed when incidents impact them. But without a solid approach, updating status pages can easily become a tedious and often neglected task during incidents. In this post, we’ll cover some tips to get your status page right.
DevNext Workshop: Mastering DevOps Package Management with JFrog Artifactory
Netdata vs Prometheus? Deep dive performance analysis! | Netdata Office Hours #8
Upcoming changes to Netdata Cloud plans
For full details on the plans and prices, check out the FAQ section of the pricing page. We continue to look for ways to make Infrastructure monitoring a reality for teams and organizations of all sizes. For users to get started with monitoring, relatively small infrastructure for Home labs, students and Non profit organizations with no investment, Netdata offers the Free Community Plan.
Enterprise Collaboration with Advanced Workflows
As a secure collaboration hub built for technical and operational teams, Mattermost is filled with features designed to help employees do their best work every day. Organizations looking to unlock even more value from Mattermost may be best off investing in Mattermost Enterprise Edition, which offers advanced functionality for enterprises with strict security and compliance requirements.
Building AI bots on your private data with an open source stack
Chiselled Ubuntu Containers
How to Share App Manager Permissions in Git Integration for Jira
From Open Source to Tomorrow: The Evolution of Dev Collaboration with Docker CTO Justin Cormack
The Evolution of DevOps with Modern Tooling - Civo.com
Eliminate scaling lag without overprovisioning Kubernetes
What is an internal developer portal?
Security in DevOps Best Practices to Keep Your Pipeline Secure
Software development, DevOps practices have become a cornerstone for organizations looking to streamline their processes and deliver high-quality software. While the agility and efficiency DevOps brings to the table are undeniable, it’s essential to remember that security should never be compromised in the pursuit of speed. In fact, it should be an integral part of the entire DevOps lifecycle.
Logic App Best Practices, Tips, and Tricks: #37 How to get distinct values from an array?
Choosing the Right PDU for Your Data Center
There are two main categories of PDUs: Basic PDUs and Intelligent PDUs. Basic PDUs are simple devices that provide power outlets from an input source, such as a wall socket or a UPS. They do not have any intelligence or monitoring capabilities, and they are usually mounted on racks or cabinets. Basic PDUs are suitable for low-density and low-complexity applications that do not require advanced power management features.
The Future of Machine Learning and AI Panel Discussion - Navigate Europe 23
How to create/update Kubeconfig file for the AWS EKS Cluster
Mastering Version Control with SharePoint Online Versioning
In today’s digital workspace, managing document versions is crucial for maintaining data integrity and fostering effective collaboration among teams. SharePoint Online, a premier collaboration platform from Microsoft, has embedded a robust versioning feature that significantly elevates document management to a new level.
Basics of Incident Management
Life is full of unexpected incidents. From the coffee spill that disrupts your morning routine to the sudden traffic jam that transforms a 20-minute commute into an hour-long ordeal. Much like these challenges, most of our systems and infrastructure also constantly face these tiny glitches. If ignored, they can have a significant impact. Unlike minor inconveniences, these glitches we call Incidents have the potential to disrupt your business, frustrate customers, and eat into your revenue.
Risks and rewards of generative AI for software development
Generative artificial intelligence (AI) is a form of AI that can create new, original content such as text, code, images, video, and even music. Generative AI-powered tools like GitHub’s Copilot and OpenAI’s ChatGPT have the potential to revolutionize the way you develop software, enabling you to be more efficient and creative. Used in the right way, generative AI can streamline workflows, accelerate development cycles, and unlock the potential for innovation.
The Future of Software: A Conversation with HubSpot CTO Dharmesh Shah & GitKraken CEO Matt Johnston
Announcing support for Spark Connect in Spot Ocean for Apache Spark
Replay Specific Messages in Azure Service Bus
Monitor Google Cloud Functions using Pushgateway and Levitate
How to monitor serverless async jobs from Google Cloud Functions with Prometheus Pushgateway and Levitate using the push model.