Operations | Monitoring | ITSM | DevOps | Cloud
January 2023
The KPIs of improved reliability
For many businesses, prioritizing reliability is an ongoing challenge. Building reliable systems and services is critical for growing revenue and customer trust, but other initiatives—like building new products and features—often take precedence since they provide a clearer and more immediate return. That's not to say reliability doesn't have clear value, but proving this value to business leaders can be tricky.
Azure Blob Storage Tiers Overview
Azure Blob storage has several storage tiers that offer different performance and cost characteristics. The storage tiers available are: Customers can move data between these tiers based on their access patterns, which can help reduce costs while still meeting performance requirements.
The Case for IT Remote Support in Education Institutions
A few years ago, the school’s technical support could still cope with its tasks. Help with technology in the classroom, maintenance of educational platforms, statistics, accounting – all these were difficult, but it was still possible to handle a few people and the IT department of the school. But the pandemic has shown how educational institutions, from elementary schools to universities and academies, need more time to be ready for large-scale work in the digital space.
Selecting the Best Azure VM Type for Your Workload
Terraform Time with Jon Bass from Sym
Does Cloud Have a Storage Problem?
Too often, when organizations migrate workloads to the cloud or build new cloud-native applications, they don’t really think about storage. The cloud provider takes care of all that, right? Well, yes and no. There are cost implications to cloud storage that many don’t adequately anticipate—until they get the bill, that is.
Azure Application Insights vs Log Analytics: Which one should you choose?
MetTel and Megaport Enable High Performance Applications in the Cloud
Before Megaport, MetTel’s customers battled impaired application performance and deployment delays when moving to the cloud. Now, their connectivity enables high-performance applications in the most distributed cloud environments. Here’s how.
Analytics in Squadcast | Visualize Team and Organization Level Analytics | MTTA MTTR | Squadcast
Delete Multiple Text Messages SMS on iPhone #shorts
#iphonetipsandtricks #imessages #iphonetips
What is Spot PC?
GitHub Tried to Change the Checksum for Release Archives. You Should Start Hosting Your Own.
Kubewarden v1.5.0
We’re pleased to announce the availability of Kubewarden 1.5.0! This release brings the usual amount of small bug fixes, dependency updates, and a major security enhancement. Let’s take a closer look!
LIVE NOW: State of DevOps | A Look Ahead at 2023
Webinar: State of DevOps | A Look Ahead at 2023
3 Key Questions to Ask Before Getting Started with Kubernetes
If you need to deploy a lot of microservices at once and manage them at scale, Kubernetes is hard to beat. But Kubernetes also brings additional complexity that you just might not need. You would be smart to ask yourself these three questions before getting started with Kubernetes.
What are Network Operation Centers (NOC) and how do NOC teams work?
Modern-day markets are highly competitive and in order to foster stronger customer relations, we see businesses striving hard to be always available and operational. Hence, businesses invest heavily to ensure higher uptime and to have dedicated teams that constantly monitor the performance of an organization's IT resources. In this blog, we will explore what NOC teams are and why they are important.
AI at the Edge Ushers in the Hyperconnected Era
We have entered the next phase of the digital revolution in which the data center has stretched to the edge of the network and where myriad Internet of Things (IoT) devices gather and process data with the aid of artificial intelligence (AI).
The Business Case for CAPI: Enhanced Kubernetes Management and More
There are instances in which organizations miss the opportunity to improve their infrastructure and gain competitive advantages by clinging to entrenched, well-worn technologies with which they are comfortable. This is the case with Terraform and Cluster API (CAPI). When explaining to various organizations the benefits they could gain through CAPI, I have heard hesitant responses such as.
Cloud desktop misconceptions: Dispelling the myths for MSPs
4 Ways To Help Engineers Understand How Their Choices Affect Cloud Costs
Why Platform Engineering Teams Are the Key to Unlocking DevOps
Building digital platforms, and platform engineering teams to support them, isn’t new. The platform approach first emerged more than 20 years ago and predates the DevOps movement that began in the mid-2000s. But the recent surge in popularity of platform engineering has caused some to argue that “DevOps is dead” and modern platform engineering has replaced it. Here’s what we found in the 2023 State of DevOps Report to counter that argument.
What's New and Coming to Spot PC (January 2023)
Deciphering container complexity from operations to security
Kubernetes turns 9 this year and with its maturity each year, it brings new challenges that drive seismic influence across the rapidly changing cloud native ecosystem. Each year we see new tools created and existing solutions optimized from new lightweight distributions, new features across Kubernetes management platforms, and container security solutions, all adding value to users but simultaneously contributing to the complexity are facing to run Kubernetes successfully.
Network and Infrastructure Monitoring - Is Every Tool the Same?
Every organization reaches a certain size where network and infrastructure monitoring becomes a necessity. And while that “certain size” will depend on whether you’re running a private company, non-profit organization or government agency, the time to act always comes. Network and Infrastructure Monitoring tools enable organizations to harness greater benefits from their computing infrastructures. How you use these tools can even give you a competitive advantage.
Are VMWare snapshots backups?
A VMware snapshot is a point-in-time copy of the virtual machine’s disk files and memory state. These snapshots are used to capture the state of a virtual machine at a specific point in time and allow users to revert to a previous state if necessary. They are commonly used for testing, patching, recovery, or rollback, but can also be used for taking backups of virtual machines.
Tips for Reduce Eye Strain on iPhone
Cutting Cloud Costs: 5 Strategies We Use at Qovery
What Is A DevOps Pipeline? A 2023 Beginner-Friendly Guide
Bob Walker - Why work with Redgate?
James Phillips - "a huge risk reduction we've been able to gain"
Chris Yates - How has Redgate helped us?
Kubernetes in the Enterprise Virtual Roundtable
4 DevOps KPIs to Measure How Well Your DevOps is Working
DevOps is an approach, not a prescriptive ideal. Still, every organization needs to be able to measure the impact and effectiveness of their investment in DevOps tools and practices. That's why we collected the top DevOps KPIs from a combination of our own research into the latest DevOps trends in the State of DevOps (including surveys of more than 4,000 people) and stories shared with Puppet.
Monitor Boundary on the HashiCorp Cloud Platform with Datadog
HashiCorp Boundary provides a secure way to manage remote access to applications and infrastructure without exposing the underlying network or credentials. Launched two years ago as an open source solution, HashiCorp recently announced a fully managed version on the HashiCorp Cloud Platform (HCP), enabling you to manage identity-based authorizations, user and target onboarding, and more for dynamic environments.
JFrog Quick Tip - How to create a virtual (maven) repo
Better Together: Accelerate feature velocity with Atlassian and LaunchDarkly
Better Together: Decoupling deployment and release with Atlassian and Split
Unified event & alert visibility - across your entire technology stack
How Ubuntu Pro delivers enhanced security and manageability for Linux Desktop users
At the end of last year Canonical announced that Ubuntu Pro, our expanded security maintenance and compliance subscription, is now available for data centers and desktops as a public beta. This week, Ubuntu Pro entered general availability, giving Ubuntu users access to extra hardening and security patching. If you’re a developer using Ansible, Apache Tomcat, Apache Zookeeper, Docker, Nagios, Node.js, phpMyAdmin, Puppet or Python 2, you’ll want to read on.
Ubuntu Pro enters general availability
Ubuntu Pro, Canonical’s comprehensive subscription for secure open source and compliance, is now generally available. Ubuntu Pro, released in beta in October last year, helps teams get timely CVE patches, harden their systems at scale and remain compliant with regimes such as FedRAMP, HIPAA and PCI-DSS. The subscription expands Canonical’s ten-year security coverage and optional technical support to an additional 23,000 packages beyond the main operating system.
Introducing version 19: New upgrades for our API server
We’re excited to announce even more new upgrades for our API servers - let’s get into the details!
GitOps The Planet #6 - K3s, Rancher, and now Acorn - Dev Productivity Nirvana with Darren Shepherd
SRE Dashboards
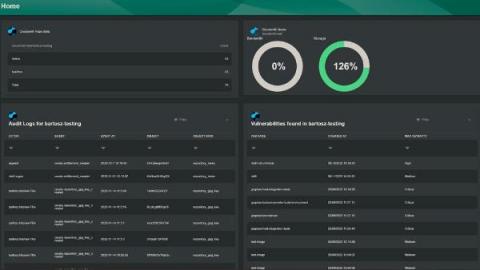
Why You Need Continuous Compliance and Risk Management
Continuous compliance and risk management can help keep your organization safe as the threat landscape changes and expands each year. IT Ops teams aren’t just working on a single machine, or even a few; they are working across technologies, across teams, at scale and expected to work fast while also considering the requirements of cost and compliance and trying to navigate around skills gaps that continue to appear.
Observability Innovation Report 2023
StackState commissioned Techstrong Research, a strategy and technology analyst firm, to delve into the current state of observability. The resulting report, “Observability Innovation Report 2023,” provides insightful information. 543 IT professionals were surveyed, globally, across 20 industries. The largest concentration of respondents were in the telecommunications, technology, Internet and electronics sectors, followed by financial services.
Config Policies & Latest Security Features
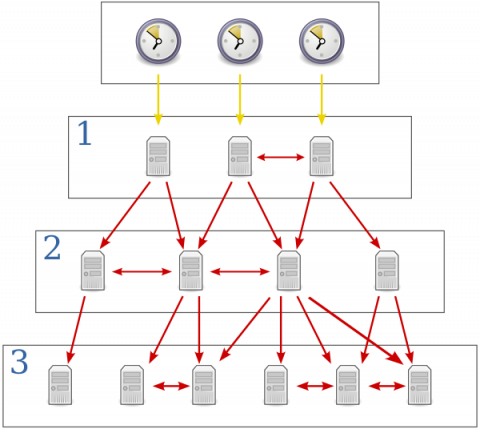
Kubernetes vs Mesos vs Swarm
5 Important Data Center Management Trends for 2023
As we reflect on 2022, it’s important to identify the latest data center trends that will continue to impact how data centers are managed in 2023 and beyond. You must stay up to date on new industry trends in order to better support your organization and customers while staying competitive in your field. Here are five data center management trends that you should know about going into the new year.
Leveraging WebAssembly for improved performance in Kubernetes
Over time, limitations were found with the programming languages responsible for creating web applications, leading to the development of WebAssembly (WASM). You can leverage WASM to create applications for web browsers using other high-level programming languages than those traditionally used for web development. As a result, developers can now build cloud-native applications that can work more efficiently with Kubernetes and other cloud-native technologies.
Optimizing DevOps Workflows with Helm Charts and Qovery's New Jobs Feature
5 Proven Ways to Better Protect Customer Data
Technology and innovation have made access to customer data a walk in the park for many businesses. In today’s world, access to customer data is one significant way businesses can provide services that their customers will find acceptable. It helps you provide personalized services and offer customers products and services they will find relevant, which will lead to increased sales conversion. But, unfortunately, most good things have their downsides, and access to customer data is not excluded.
Do DORA metrics spy on you?
An In-Depth Overview of Azure Storage Accounts & Services
Azure storage accounts offer powerful, cost-effective options for managing your data and applications. With various services such as blobs, queues, files, and tables, you can use Azure Storage to store and access virtually limitless amounts of data effectively. This guide will walk you through all the basics of setting up and using an Azure Storage Account.
Kubecost Vs. Cast.ai: Battle Of The Kubernetes Cost Tools
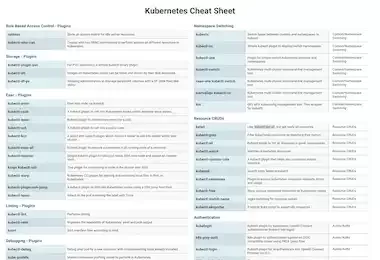
Kubectl Cheat Sheet
In the world of container orchestration, Kubernetes has become the de facto standard. Despite its simplicity in some respects, it has also introduced new levels of complexity in the deployment and management of distributed applications and services. To assist you with understanding the most common kubectl commands & plugins, we've created a cheat sheet as a reference for operations engineers, software engineers, and cloud infrastructure managers who use Kubernetes primarily.
7 Powerful DevOps Tools You Should Know in 2023
Have you ever wished that software development could be faster and focused on quality? Then DevOps may be the answer for your organization. DevOps is a set of practices that combine software development and IT operations to facilitate collaboration between teams. The industry is constantly evolving, and new tools are being introduced daily. With so many options, it can take time to determine which ones are worth your time and money.
Announcing Wildcard SSL Support
Hey everyone, We've got some exciting news to share - wildcard SSL certificates are now available on Cloud 66! If you're not familiar with wildcard SSL certificates, they allow you to secure multiple subdomains under a single certificate. Our options for adding an SSL certificate to your application are now updated to include the following: To set up a Wildcard certificate on Cloud 66, just open your app on your Dashboard and click Network, then SSL Certificate, and then "Add SSL".
Building and deploying Ubuntu FIPS containers on EKS
Deploy s3gw in Digital Ocean
In this tutorial, we will walk through the setup of a single-node K3s Kubernetes cluster with Rancher, together with the S3 Gateway (s3gw) and a Longhorn PV (Persistent Volume). This guide will use Digital Ocean, but these instructions will likely work with other cloud providers as well.
Outgrown your ELK self-managed clusters and not sure what to do about it?
As data volume grows, managing your ELK stack can become resource-intensive. Organizations outgrowing ELK are often using multiple different tools, experiencing performance issues, paying too much in log storage, and spending significant time troubleshooting. But while the pain is real, many are hesitant to make a change. The thought of migration yields fears of lost productivity, performance and financial risks, and disappointment in losing some things you love that you worked hard to create.
How Quantum Computing Can Better Protect Your Data
Bringing the power of quantum encryption to the cloud, we take a look at the emerging technology that’s changing how we protect our data.
How digital twins enable data-driven automotive supply chains
The automotive industry is facing one of its biggest revolutions since the advent of automation. In this post, we will go through the Industry 4.0 aspects and how OEMs can turn these challenges into opportunities. To put it simply, the first Industrial Revolution relied on steam power, the second one on electricity and the third one on computers. What about the fourth Industrial Revolution everyone is talking about? I would describe it as a data-driven revolution.
Unsolicited Opinions About the Latest Forrester Wave on AIOps, Part 2 - A Closer Look Into the Evolution of AIOps
An Overview of Traffic Mirroring Options in Kubernetes
The business value of frequent deployments
Getting started with unified observability for Azure in less than 10 minutes using terraform
Honeycomb, Meet Terraform
Most SaaS products have nice, organic growth when they work well. Employees log in, they click around and make stuff, then they share links with others who do the same. After a few weeks or months, there are thousand of objects. Some are abandoned, and some are mission-critical. Different people also bring different perspectives, so they name things that are relevant to their role and position in the team, which may be confusing to others outside their realm.
5 Exciting Predictions for SRE in 2023
Ubuntu on WSL | An FAQ for Data Scientists and Developers
Tanzu Application Platform 1.4 Reduces Developer Toil, Enhances Operations and Security Outcomes
VMware has released new capabilities in VMware Tanzu Application Platform that can continue to elevate the developer and IT operations experiences, as well as ease security management. This blog post outlines the new functionality included in Tanzu Application Platform 1.4, which is generally available now.
Runbook Automation as a Baseline for Controllability and Observability
Some of the highest priorities for engineers - from NOC Engineers, DevOps & Site Reliability Engineers - are the automation and optimization of their production environments. Many companies today face tough challenges with their Network Operations Centers (NOCs) or production environments. These challenges fall into the hands of engineering teams.
On-Premises vs Cloud MDM deployment: Key Differences between them
On-premises vs cloud MDM deployment With the rise of SaaS application management, mobile device management (MDM) services have gained popularity among IT professionals. Modern computing environments rely on the efficient use and provisioning of resources. But which one is right for your business: on-premise or cloud MDM deployment? While this may seem like a simple question, there are many factors that come into play when deciding which method to go with. This article discusses the differences between on-premises vs. cloud MDM deployment. It will also present examples, use cases, and pros and cons of these two deployment options.
7 Container Orchestration Tools for Managing Microservices Efficiently
When people hear ‘containers,’ they don’t immediately think about an IT solution that helps businesses create and distribute applications seamlessly. However, the container concept has been around for a long time, helping companies in various industries globally. Containers continue to change the landscape of app development and deployment. This guide below will help you understand containerization and the best orchestration tools to manage containers.
What is MLOps going to look like in 2023?
While AI seems to be the topic of the moment, especially in the tech industry, the need to make it happen in a reliable way is becoming more obvious. MLOps, as a practice, finds itself in a place where it needs to keep growing and remain relevant in view of the latest trends. Solutions like ChatGPT or MidJourney dominated internet chatter last year, but the main question is…What do we foresee in the MLOps space this year and where is the community of MLOps practitioners focusing their energy?
Provision and manage Elastigroup with the new AWS Quickstart Guide
What is Observability Engineering all about? One minute overview.
Understanding Cloud Costs In 2023
Guest blog post: Don't use your distro's package manager
I have stopped using my Linux distro’s package manager, and you should, too. Maybe I should clarify that. I don’t install software with my distro’s package manager any more. I still upgrade my system. I became influenced by a few different factors. Top among these is something required in certain industries called a change advisory board or committee.
Why Performance And Cost Are Two Sides Of A Coin
Applying Lessons Learned from Baking Pizza to Kubernetes Observability
Baking a delicious pizza in a wood-fired oven requires a combination of skill, experience and the right tools. The same is true for achieving optimal observability in a Kubernetes environment. In this post, we'll explore some of the lessons learned from baking pizza in a wood-fired oven and apply them to the world of Kubernetes observability.
Modernizing LinkedIn's Traffic Stack | Sanjay Singh & Sri Ram Bathina
Hosted StatsD vs. StatsD
When you are designing and building applications, you should consider how to monitor them once they become live. You do not want to be blindsided by errors and degrading performances as you operate them. When your applications fail to provide optimal performance, it can broadly impact your business. Engineers will often be distracted to investigate and fix the issues. Customers will complain. It can eventually hit your bottom line.
Logic App Best practices, Tips, and Tricks: #20 Accessing Runtime Settings (Part I) - Logic App Consumption
JFrog Connect IoT Device Management Solution
How we approach integrations at incident.io
If you pick a random SaaS company out of a jar and go to their website, chance are they integrate with another tool. Typically, the end goal of integrations is to meet users in the middle by working with other tools they’re already using on a day-to-day. Put another way, integrations are a strategic business decision. But the question remains: why don’t companies just build a tool with similar functionality in order to make the product stickier?
What are Azure Native Services?
Azure native services are cloud-based solutions that are developed, managed, and supported by Microsoft. These services are designed to help organizations build and deploy applications on the Azure cloud platform, and take advantage of the scalability, security, and reliability of the Azure infrastructure. In this blog post, we’ll take a look at some of the key Azure native services that are available, and how they can be used to build and run cloud-based applications.
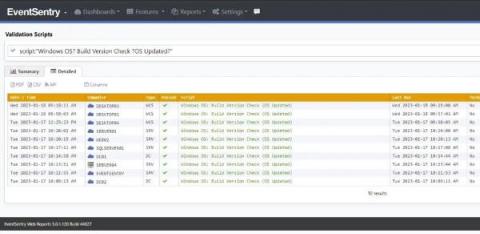
The Life of the Sysadmin: A Patch Tuesday Story
The System Administrator! AKA the Sysadmin. The keeper of the network, computers – well basically all things technology. The one who is hated for imposing complex passwords and other restrictions, but taken for granted when everything works well. They are the first to be called when “facebuuk.com” reports: “domain does not exist”.
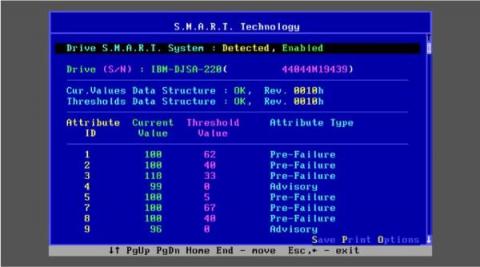
How to monitor and troubleshoot S.M.A.R.T. attributes
Understand what makes a storage device S.M.A.R.T and how to monitor a self monitoring component using Netdata.
How to monitor and troubleshoot BIND 9
Find out how to effectively and easily monitor and troubleshoot BIND 9 using Netdata.
Platform.sh is always one step ahead: Announcing PostgreSQL 15, Python 3.11, and Ruby 3.2 for our users
As a developer, it’s important to stay up-to-date with the latest programming languages and updates. But this is no easy task with the fast-paced nature of our techy industry - so we thought we’d do some of the work for you! We’re excited to announce the release of the latest versions of Python, PostgreSQL, and Ruby which our users can already benefit from via our platform.
How do your DevOps plans really measure up?
iPhone Markup Tips You Should Know #iphonetips
#iphonetipsandtricks #shorts #markup
CircleCI New Feature: An Overview of Container Runner
Get in Front of Delivery Risks by Managing Work in Progress: Turn Your DORA Metrics into Trip Wires
What are Webhooks and why should developers use them?
Ubuntu 18.04 LTS End Of Life - keep your fleet of devices up and running
Ubuntu 18.04 ‘Bionic Beaver’ is reaching End of Standard Support this April, also known sometimes as End Of Life (EOL). This distribution of Ubuntu was installed by millions of users and powers up thousands of devices. From kiosks and appliances to IoT devices and robots, 18.04 helped many companies deploy innovations to the world. As with all other Ubuntu LTS releases that reach their end of standard support, Bionic Beaver will transition to Extended Security Maintenance (ESM).
A DWDM Guide: Definition, Benefits, and When You Should Use It
Today’s telecom, cable, and data providers constantly compete to provide the best, most reliable service to customers, while investing in the right technologies to maintain the integrity of data and enable the separation of users. Because of this, service providers often spend countless hours searching for cost-effective, yet future-proof solutions that fit their business needs. This is where DWDM comes in.
Introducing Project and Workspace Access Tokens
Supercharging ITSM Collaboration with Mattermost and ServiceNow
Mattermost’s core mission is to provide secure collaboration for technical teams. To do so, we concentrate on providing a collaboration layer that powers key technical and operational workflows for our customers. A prime example of this focus is the new ServiceNow integration for Mattermost, which weaves together key ServiceNow ITSM features such as Incident, Change and Problem management with Mattermost’s rich collaboration features.
Kubecost Vs. OpenCost: What's The Difference?
How Bitnami Uses VMware Image Builder to Deploy 60k Apps Per Month and How You Can Do the Same
Have you ever wondered what it takes to build, deploy, and verify 2,000 applications every single day? In this blog post, we will delve into this specific challenge and take a look at how VMware’s Bitnami can dramatically boost productivity by using VMware Image Builder for automating content production. But let’s start from the beginning, and explore what it takes to build and ship software to users.
Best SRE Practices to Help Developers Troubleshoot Kubernetes
What is a NMS?
A powerful new incident analytics experience is now generally available for Enterprise customers
Automatically measure MTTR, impacted infrastructure, task completion, and more with new incident analytics.
2bcloud Supports Stor.ai with AWS Adoption in Multi-Cloud Environment
Stor.ai is a retail market ecommerce solutions provider. Its state-of-the art white label retail platform allows clients to quickly and easily connect to inventory, position their brands to develop customer loyalty, and boost average order value. Running a large cloud-based operation requires a well-provisioned cloud platform capable of managing the load and delivering peak performance.
What Millions of Requests per Second Mean in Terms of Cost & Energy Savings | Willy Tarreau
How to monitor and troubleshoot Memcached
Find out how to effectively and easily monitor and troubleshoot Memcached using Netdata.
How to set up a developer portal
Azure Cloud Automation with Cloudify
If you are reading this, you’re likely familiar with Azure’s cloud solution advantages. Now think how powerful it would be if you could tie them together with the enhancements of the Cloudify platform. You’ll be able to create one great Azure deployment automation solution. It would take advantage of everything you love about Azure while not getting in the way when you move your workloads between private, public, and hybrid clouds.
CloudHedge is Gartner Cool Vendor in Cloud Native Computing
Iselin, New Jersey – 19th January 2023 – CloudHedge Technologies, an industry pioneer with its end-to-end Continuous Application Modernization platform, OmniDeq™, has been named Cool Vendor in Cloud-Native Computing by Gartner. The report acknowledges CloudHedge’s ability to securely deliver agile digital transformation and modernization journeys for large-scale enterprises, enhancing their efficiency.
How to Assess Current Workloads for a Cloud Migration
Cloud storage pricing - how to optimise TCO
The flexibility of public cloud infrastructure allows for little to no upfront expense, and is great when starting a venture or testing an idea. But once a dataset grows and becomes predictable, it can become a significant base cost, compounded further by additional costs depending on how you are consuming that data.
Maximize Cloud Savings: Advanced Cost Reduction Strategies
Cloud migration can be a powerful way for organizations to reduce costs and improve efficiency. However, simply moving to the cloud is not enough - there are a number of tactics that teams can adopt to maximize cost savings. In this article, I will first explore some common tactics that cloud migration teams use to reduce costs, then share advanced strategies that our most successful customers use to truly take advantage of the cloud for all of its far-reaching benefits.
Guided Kubernetes Troubleshooting: How to Reduce Toil for Dev Teams
This blog post is a how-to guide for Kubernetes troubleshooting. Our vision is that any engineer can keep Kubernetes-based applications up and running smoothly, regardless of their level of Kubernetes expertise and their knowledge of the services in the environment. Right out of the box, StackState aims to monitor, alert and then guide an engineer directly to the problem, helping them remediate the issue quickly.
Heroku Enterprise vs. AWS: What to choose as a business?
An internal developer portal
2023 State of DevOps Report Finds Platform Engineering Unlocks DevOps Success in the Enterprise
Website downtime and ways to prevent it from happening
7 Effective Ways To Reduce Cloud Waste In 2023
Reliability and SRE in the 2022 State of DevOps Report
Learn more about the connection between SRE, DevOps and reliability.
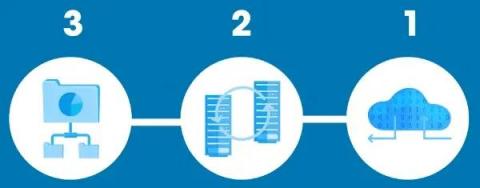
Understanding the 3-2-1 Backup Rule
While data disasters are inevitable, having a planned backup strategy can mitigate its damaging effects. According to the Cybersecurity and Infrastructure Security Agency, businesses and organizations should observe the 3-2-1 backup strategy for assured data safety. Superficially, the 3-2-1 backup rule is a backup strategy that increases and diversifies the number of backups used.
How do you connect an Azure Storage Account to Active Directory?
Azure Storage Authentication is the process of verifying the identity of a client that is requesting access to an Azure storage account. Azure Storage supports several authentication options that can be used to secure access to storage accounts, such as: Choosing the best authentication option depends on your requirements such as security, ease of use and ease of integration with existing systems or platforms.
Optimizing Build Time and Getting Results Using Test Splitting
Boosting Developer Welfare: The Power of Community
Since the onset of the pandemic and the changes in working patterns that resulted from it, employee welfare has been boosted to the top of the agenda, with this new mindset seeming to be lasting. According to the UK’s Chartered Institute of Personnel and Development, 75% of employees believe senior leaders prioritize well-being as part of business operations.
Containerization vs. Virtualization : understand the differences
Over the last couple of decades, a lot has changed in terms of how companies are running their infrastructure. The days of dedicated physical servers are long gone, and there are a variety of options for making the most out of your hosts, regardless of whether you’re running them on-prem or in the cloud. Virtualization paved the way for scalability, standardization and cost optimisation. Containerization brought new efficiencies.
How to monitor and troubleshoot NTPdaemon
Find out how to effectively and easily monitor and troubleshoot NTPdaemon using Netdata.
Mattermost mobile v2 is now generally available
Mattermost mobile v2.0 is a major update to the iPhone and Android apps bringing support for multiple workspaces and intuitive navigation improvements so you can be more productive on the go. We began rolling out the update this week, so you simply need to update to the latest version of Mattermost in the Apple App Store or Google Play Store. The update will be coming to everyone by the end of January.
New Relic Pricing Explained: A 2023 Guide To New Relic Costs
Efficiently Upgrading Infrastructure with Qovery: Syment's Success Story
APIs Impact on DevOps: Exploring APIs Continuous Evolution
An application programming interface (API) is a set of rules and protocols that enables different software applications to communicate and share data and functionality. The concept of an API has been around for a long time. However, APIs as you know them emerged in the late 1990s and early 2000s with the rise of the internet and web-based services. As more businesses began to offer online services, the need for a standardized way for these services to interact and share data became apparent.
Challenges and Solutions with Cloud Native Persistent Storage
Persistent storage is essential for any account-driven website. However, in Kubernetes, most resources are ephemeral and unsuitable for keeping data long-term. Regular storage is tied to the container and has a finite life span. Persistent storage has to be separately provisioned and managed. Making permanent storage work with temporary resources brings challenges that you need to solve if you want to get the most out of your Kubernetes deployments.
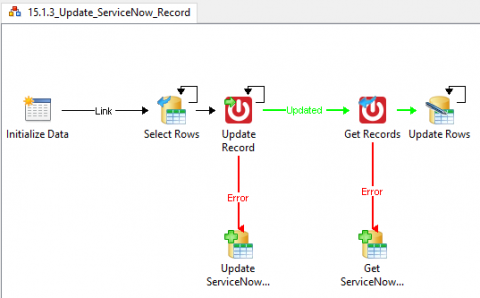
Process Automation Release Notes v4.9.0
5 DCIM Software Success Stories as Told by Real Customers
Managing a data center is not easy. Today’s data center professionals must maintain uptime, increase the efficiency of capacity utilization, and boost the productivity of people in more complex and more distributed environments than ever before. Legacy management tools like Excel, Visio, and homegrown systems no longer get the job done for the modern data center. They are hard to use, difficult to maintain, time-consuming, and error-prone.
Using distributed tracing to identify bottlenecks in your app flows
As an engineer building a distributed application, every now and then I need to look for and analyze bottlenecks in our system. There can be several triggers for conducting a bottleneck analysis, for example: In this blog post I’ll share how I’ve been using our own product, Helios, and the power of distributed tracing, to help pinpoint bottlenecks in our system and resolve them fast.
Logic App Best practices, Tips, and Tricks: #19 Protect your Logic Apps (Part II)
Resolve Systems is Named a Leader in IT Automation by Zinnov
Megaport Simplifies AWS Outposts Networking
Combining AWS Outposts Rack with Direct Connect optimizes performance for demanding enterprise workloads. Megaport’s Outposts Ready Direct Connect solution simplifies the networking side.
Interlink Software arrives on the Cisco AppDynamics Marketplace!
We are delighted to share the news that our integration with leading, real-time Application Performance Monitoring (APM) vendor Cisco AppDynamics is now listed on the AppDynamics Marketplace.
6 Strategic Reasons Why Businesses Need Remote IT Support
Why Remote IT Support: Many businesses across a variety of different sectors are choosing to outsource their technology needs through remote IT support. As a result, you tend to get quicker response times and sector-specific help when you work with remote teams. Additionally, remote work is highly attractive to a lot of skilled professionals, so you are much more likely to work with an expert in the field.
Mattermost v7.7 is now available
Mattermost v7.7 is generally available today. With this latest release, we’ve added new functionality to help teams accelerate productivity while ensuring data and infrastructure control to reduce security and compliance risk. The following new features are included (see changelog for more details).
ITIL vs. DevOps: What is best for your organization?
When it comes to managing IT services, there are two schools of thought: DevOps and ITIL. DevOps is a newer approach, while ITIL has been around for decades. Both have their pros and cons, but which method is the right one for your business? Is ITIL still relevant in an era of cloud computing, artificial intelligence, blockchain and IoT?
DKP 2.4 Takes Multi-Cloud Kubernetes Management to New Heights
With the release of the D2iQ Kubernetes Platform version 2.4 (DKP 2.4), the best Kubernetes platform just got better, particularly the ability to manage Kubernetes clusters across multi-cloud and hybrid cloud environments. What makes DKP so special? D2iQ’s business is focused solely on creating a container management platform that is as complete and reliable as possible.
How to monitor and troubleshoot MongoDB
Find out how to effectively and easily monitor and troubleshoot MongoDB using Netdata.
Spot Ocean CD is now live for all Spot users
Ubuntu 22.04 LTS Jammy Jellyfish is Now Supported!
Announcing support for Ubuntu 22.04 LTS Jammy Jellyfish on all Cloud 66 products (including registered servers). From this point onward, brand-new applications will have Ubuntu 22.04 installed. We will continue to install Ubuntu 20.04 when scaling up servers in an existing application. Don't forget, you can control your target Ubuntu version through your manifest! Ubuntu 22.04 is a Long-Term Support (LTS) release and will receive ongoing app updates and critical security fixes till April 2027.
ServiceNow and Mattermost Playbooks Demo
Mattermost Mobile 101
Mattermost Mobile Demo
3 tips for reducing stress during incident response efforts
Panic takes time and energy away from swift incident response, leading to second-guessing, a higher likelihood of mistakes, and analysis paralysis. Here are three tips to minimize it.
AWS Elastic Load Balancing: Classic Load Balancer vs. Application Load Balancer
ChatOps Explained and Why DevOps Teams Should Care
Why the cloud does not have to be a costly venture
Looking back on the last 18 months, it is abundantly clear that one piece of technology found its moment more than any other: cloud. Essential to modern computing, cloud provides the capacity for businesses to run workloads with the flexibility and scale many firms would struggle to achieve with on-premise infrastructure. According to Flexera’s 2021 State of the Cloud Report, 90% of firms slightly or significantly increased their cloud usage due to the pandemic.
What is Platform Engineering?
In this blog, we’ll define platform engineering, outline its benefits for software development, explain how it intersects with DevOps, and identify the key components platform engineering needs to be successful.
How To Optimise Your Cloud Infrastructure In 2023
Understanding Site Reliability Engineering (SRE)
Success in this modern age of digital services and operations is found when businesses are able to prioritize effective digital processes. Because of this, IT teams are constantly looking for ways to improve their IT operations by making them efficient, reliable, and scalable. One way this is accomplished is through site reliability engineering (SRE). LinkedIn listed SRE as the 21st fastest growing job in the U.S. in January 2022. What is SRE, and why is it in such high demand?
How To Reduce Strife Between Engineers And Finance
Cloud optimisation: cut your 2023 cloud spending by two-thirds
Cloud optimisation enables organisations to significantly lower their cloud spending while ensuring the desired performance and necessary compliance. It’s a process that every business should adopt when choosing cloud infrastructure as a foundation for their applications. It’s been proven that applying cloud optimisation best practices leads to a total cost of ownership (TCO) reduction of two-thirds under certain circumstances. But let’s step back for a second.
Getting started with ROS security scanning
It’s a new year, and an especially great time to reflect on the security of your robots. After all, those interested in breaching it are probably doing the same. In previous articles, we discussed ROS security by detailing practical steps for securing your robots on Ubuntu and the challenges the community faces. In this blog post, I’ll give you some strategies, tips and open-source tools you can integrate into your development process today to ramp up the security of your project.
How to Preview and Diff Your Argo CD Deployments
Adopting Kubernetes has introduced several new complications on how to verify and validate all the manifests that describe your application. There are several tools out there for checking the syntax of manifests, scanning them for security issues, enforcing policies etc. But at the most basic case one of the major challenges is to actually understand what each change means for your application (and optionally approve/reject the pull request that contains that change).
Mattermost Boards 101
Mattermost Channels 101
Ubuntu Desktop on Amazon Workspaces: A quick start guide
How to setup and use Azure SFTP Service with Azure Storage.
Azure SFTP (Secure File Transfer Protocol) is a service provided by Microsoft Azure that enables you to transfer files securely to and from Azure storage. The service is built on the SFTP protocol, which provides a secure way to transfer files over the internet by encrypting both the data in transit and the data at rest. Azure SFTP allows you to easily automate the transfer of large amounts of data such as backups and log files, to and from your Azure storage account.
How to Check Screen Time on Android Phone | Android Screen Time Tracker
IT Workflow Explanation
10 Points of consideration for investing in an Observability Platform for your organization.
Cultural drivers of DevOps success
Learn more about how culture is the true driver of DevOps success.
What's next for the Cloud Native industry? Civo's predictions for 2023
As we enter a new year, our team has made predictions for the coming year in the Cloud Native ecosystem.
New data reveals challenges and opportunities in DevOps
MongoDB Pricing Explained: A 2023 Guide To MongoDB Costs
What is Azure Automation?
As Microsoft Azure continues to be developed and more automation options become available; Azure Automation, Logic Apps, ARM (Azure Resource Manager) and Azure Function Apps to name a few. The question is quickly turning from ‘how do I automate with Azure?’ to ‘what automation type do I use in Azure?’. Across our next few blogs, we will seek to delve into the options available and look to define how they stack up against Azure Automation.
Guide to Platform Engineering: Goals and Best Practices of Platform Engineering Team
CircleCI incident report for January 4, 2023 security incident
On January 4, 2023, we alerted customers to a security incident. Today, we want to share with you what happened, what we’ve learned, and what our plans are to continuously improve our security posture for the future.
How to Mirror iPhone to iPhone? Quick & Simple Way
Techstrong TV Interview: Toffer Winslow Talks Observability
MetricFire in 2023
As we welcome a new year, many people set goals, refresh their schedules, and look forward to making the most of 2023. At Metricfire, we think it’s important to reflect on the past and plan for the future. So we’re looking forward to creating goals for our company while sticking to our core values. In this article, we’ll briefly cover some of our company goals for 2023, specifically for our culture, our roadmap, and our growth as a company.
PagerDuty Status Pages Enable Real-Time, Proactive Customer Communication During Incidents
Easy to manage fine-grained access control and roles
A neatly setup access control telling which user can do exactly what on an incident management platform can save a lot of time and hassle in the future. In the past, Spike.sh had only 2 roles - Admin and Member. The only difference in these roles were that only Admins can remove members. It was fairly simple and most users liked it. However, with larger teams coming onboard, it gets a little difficult to control for admins. So, we have empowered the existing system by adding two more roles.
Kubernetes Preview Environments - Adoption, Use Cases & Implementations
Software supply chain security: How to audit a security bill of material (SBOM)
A security bill of material (SBOM) is an inventory of the entire building components of a software application. These components include open source libraries, dependencies, commercial components, licenses, patch status, version information, upgrades available, CVEs, etc. Having an SBOM of a codebase or piece of software provides deep visibility into core components that help quickly identify and mitigate the security and licensing risks associated with the software supply chain.
Trust Me - I'm a SASE Solution
As we get ready to wish the term SASE a happy 4th birthday, it seems odd that there is still a great deal of confusion in the market about what SASE really is and how it relates to a ‘Zero Trust’ architecture. For many, SASE is a framework for secure network design; for others, it’s seen more as an architectural approach to delivering Zero Trust. So why do we have this confusion when Gartner defined SASE back in 2019?
Need your own incident post-mortem template? Here's ours
Having a dedicated incident post-mortem is just as important as having a robust incident response plan. The post-mortem is key to understanding exactly what went wrong, why it happened in the first place, and what you can do to avoid it in the future. It’s an essential document but many organizations either haphazardly put together post-incident notes that live in disparate places or don’t know where to start in creating their own post-mortems.
5 best incident management tools of 2023
Put simply, managing incidents—big or small—is good for business. Not only is it a regulatory requirement, but also a factor in your profits. Your customers expect smooth operations, good customer service and protection. A dedicated incident management tool can help protect all of these. While many may think of incidents as an IT or DevOps issue, it’s hard to over emphasize that they can happen in any department.
Unsolicited Opinions About the Latest Forrester Wave on AIOps, Part 1
Why DevOps needs an AIOps approach?
Incident Management Tools - Do I Even Need Them?
A guide to successfully onboarding a developer
Integrating Cloudsmith with Your Roadie Developer Portal
Customers can now integrate Cloudsmith with Roadie, letting users monitor key Cloudsmith data within the Roadie developer portal. Cloudsmith has just announced an exciting new integration with Roadie, a start-up that provides SaaS for Backstage, a service catalog open-sourced by Spotify that automatically tracks your microservices. Organizations use Roadie to build a software catalog and developer portal for internal systems, centralizing information in one convenient location.
Cycle Podcast | EP 16 | Tom Daly | Simplifying Global Networks + Insights into Startup Investing
Overview of Folders in Azure Blob Storage
Azure Blob Storage is a fully managed, scalable, and reliable object storage service provided by Microsoft Azure. One of the key features of Azure Blob Storage is the ability to create and organize data in containers called “folders.” In this blog post, we’ll take a closer look at how folders work in Azure Blob Storage and how you can use them to organize and manage your data.
What is Azure Files and what are they used for?
Azure Files is a fully managed, cloud-based file storage service provided by Microsoft Azure that allows you to share files across multiple servers and platforms. One of the key features of Azure Files is the ability to create and organize files in folders, similar to how you would on a traditional file server. In this blog post, we’ll take a closer look at how folders work in Azure Files and how you can use them to share files with others.
NOAH 2022 Zurich: You Don't Need Another Server
Applying AIOps: Sending alerts from Moogsoft to Mattermost
SUSE Receives 15 Badges in the Winter G2 Report Across its Product Portfolio
I’m pleased to share that G2, the world’s largest and most trusted tech marketplace, has recognized our solutions in its 2023 Winter Report. We received a total of 15 badges across our business units for Rancher, SUSE Linux Enterprise Server (SLES), SLE Desktop and SLE Real Time – including the Users Love Us badge for all products – as well as three badges for the openSUSE community with Leap and Tumbleweed.
How to Troubleshoot Slow Services in Your Kubernetes Cluster
To get the best performance out of your Kubernetes cluster, SREs and software engineers must have enough knowledge and instruments to find misconfiguration and bottlenecks. At the same time, thanks to Kubernetes’ ever-growing popularity, there is a global shortage of expertise on the platform.
Deploying Hanami 2.0 Ruby application on AWS
The deployment of Ruby on Rails and Rack frameworks is embedded in Cloud 66’s DNA, but we are always interested to see other Ruby frameworks becoming popular, and happy to support developers who prefer to use them instead of Rails. In this post, we’re going to show you how easy it is to deploy a Hanami Ruby application on AWS cloud with Cloud 66. The recent Hanami v2.0 release brought a lot of incremental upgrades to the framework, which made it more mature.
How To Deploy Node.js To Production Kubernetes In Seconds
GitOps The Planet (E5) | Homelabs with K8s@home
A practical guide for implementing SLO
How to set Service Level Objectives with 3 steps guide.
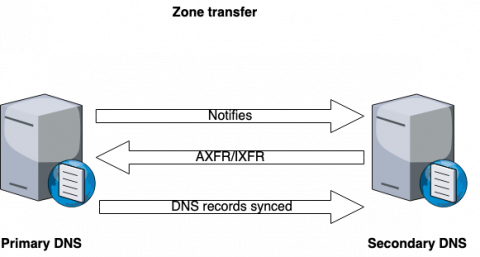
DNS redundancy: What are secondary DNSs and zone transfers?
The primary DNS server hosting a zone or multiple zones acts as an authoritative DNS through which DNS administrators manage zone files and perform DNS changes like adding, deleting, and updating DNS records.
Git vs GitHub
Sophia Diachenko is a PR Manager at Syndicode,a leading digital transformation and products delivery company focused on marketplace creation, SaaS development, and web application development. In her free time, Sophia enjoys broadening her knowledge in the IT sphere. Git and GitHub are two powerful tools widely used in software development. Both can help manage code, but they have different purposes and capabilities.
Predictions for 2023
In 2022, Kubernetes continued to mature and gain widespread adoption as it crossed the chasm into the mainstream. Following are the predictions we see for Kubernetes in 2023.
Recap of Serverless360's journey in 2022
Maximizing cloud savings: Strategies to optimize your cloud costs
Public cloud users continue to get stung by unexpected costs due to the challenges faced when working with or moving workloads into the cloud. When organizations see this surge in their costs, it typically requires the process of cloud cost optimization to tackle the problem. Cloud cost optimization is the task of minimizing cloud spending by enforcing best practices and appropriate cost-efficient resources.
The 10 Best Multi-Cloud Management Tools In 2023
The Role of Traffic Replay in Production Traffic Replication
How Augmented Reality Can Change Physical Repair
Augmented Reality for Industry Repair When augmented reality emerged onto the scene, most people anticipated that it would primarily change consumer industries, like gaming. This idea was seemingly confirmed with the explosive popularity of Pokémon Go, the 2016 AR game that saw gamers capture virtual pokemon out in the real world, using only their phone. But some of the most powerful applications of augmented reality are in industry.
I/O Wait Time: A Guide to Improving Linux Performance
I/O wait is a plaguing issue in Linux. Speaking in layman terms, I/O wait is the time taken by the processor (here, CPU) to complete an input service request. Ideally, our CPU doesn't seem to do any work when it is processing one input request at a time, thus the duration between your input and the output provided by the system can be treated as the I/O wait time.
Why SREs need better visibility, not more tools
Overcoming The DevOps Shortage: The Power of Tools and Technologies
How to Get Call History | Call Details of Any Mobile Number in 2023
Introducing Levitate: 'uplifting' your metrics woes because self-management sucks like gravity
Managing your own time series database is painful. We’ve moved from servers to services, and yet, monitoring metrics data is primitive. Our managed time series database powers mission-critical workloads for monitoring, at a fraction of the cost.
Resolve Systems Appoints Natalie Padula as Vice President of Sales as Company Scales for Growth
The Definitive Guide to Traffic Replay
DIY chiselled Ubuntu: crafting your own chiselled Ubuntu base image
In a previous post, I explained how we made our Ubuntu image 15 times smaller by chiselling a specific slice of Ubuntu for.NET developers. In this blog, I will provide step-by-step instructions on customising your chiselled Ubuntu base images for any use case. I don’t believe in a perfect container base image anymore.
Android Geofencing Guide: Track & Secure Devices with AirDroid Business
Many of our customers have already embraced mobile transformation and are sending them out in the field to give employees better productivity. For instance, truck drivers now use Android devices for communication and managing their logistics delivery; health organizations use Android tablets to track the location and health status of patients.
Top 10 DevOps Challenges & How AIOps Can Help
SRE Report 2023: Are we Aligned? Yes. No. Maybe.
Each year of the SRE Report, there’s a trend or anti-pattern that leaps out and makes us pause and reflect. Last year, for example, we found a huge drop in global toil levels. With the whole world working from home for a full year, it made sense that global toil levels would drop, right? But this year, despite the great reopening underway, toil levels dropped even further - it's a paradox, one which no doubt will require its own scrutiny.
Introducing CloudZero Support For New Relic: Enabling A More Efficient Approach To Observability
Ndustrial Expands Globally with Help from JFrog Connect
9 Go-To SysAdmin Password Generators
The Most Reliable WordPress Hosting Providers. The Study Based on Real Outage Data
According to data from W3Techs, more than 40% of all websites are built on WordPress. Therefore, it’s no surprise that WordPress hosting has skyrocketed in popularity recently and hosting providers have proliferated. With so many choices, it’s important to understand just how reliable WordPress hosts are, especially when it comes to downtime. Web hosting downtime can have significant consequences such as business loss, brand damage, and missed opportunities.
What Databases Taught Me About Scaling Observability
It's Time To Stop Pitting On Prem and Cloud Against Each Other
Most sentences that include both on premises and cloud usually put the word “or” between them, or perhaps “vs.” But most enterprises operate in the world of “and.” In other words, they have workloads on premises and in the cloud—and that little three-letter word makes a world of difference.
The ten habits for highly successful compliant database DevOps
Komodor Goes Freemium
I’m so excited to share with the world that today Komodor has officially transitioned to a freemium model, and made all of its great features available to small teams for FREE! Now, every developer can use Komodor to observe, manage, and troubleshoot Kubernetes with ease. By simplifying K8s operations and injecting our own expertise into the product we’ve created a better dev experience that reduces toil and sparks joy.
Value Stream Management Adoption Increases in 2023 According to Broadcom's 2nd Annual VSM Trends Report
Beginners Guide To Automation Runbooks
Automation and it’s use of the term Runbooks can be confusing and difficult to understand, especially when first starting out. We’ve put together some frequently asked questions and answers to help beginners get started.
Lessons from the CircleCI Security Incident
In some respects, security and reliability are competing priorities. Security controls may reduce reliability, and responding to security incidents may require mission-critical systems to be paused or shut down until they're secure. The recent security incident involving CircleCI, however, shows that it's not always necessary to choose between prioritizing security or reliability.
Chiselled Ubuntu containers: the benefits of combining Distroless and Ubuntu
In this blog, I explain the idea behind Distroless container images, which inspired us to create chiselled Ubuntu images — adding the “distro” back to distro-less! In a follow-up blog, I will then provide a step-by-step example of how you can create your own chiselled Ubuntu base container images, built for your specific needs.
How to create a Weekly On-call Schedule for Business & Non-Business Hours | Squadcast
How to Create Weekly On-Call Schedules in Squadcast | SRE | Squadcast
How to Create Weekend On-Call Schedule on Squadcast | Squadcast On-call Schedules | Squadcast
How to Create Schedule Overrides in Squadcast | Override an existing On-Call Schedule | Squadcast
How to Create a Daily On-Call Schedule | On-Call Rotation | Squadcast
How to adjust Day Light Savings in Squadcast's On-Call Schedules | Squadcast
Unified IT Operations Management: What It Is and Why It Matters
When IT teams and departments aren’t on the same page, they unintentionally create blockers and other issues that negatively affect the entire organization. To prevent these troublesome issues from occurring, CIO recommends looking into a few ways to make IT operations more efficient, such as automating processes or adopting a new IT approach.
Longhorn 1.4 - Starting A New Year With A New Release
The team are excited to start the new year with the latest release for Longhorn 1.4. This latest version is packed with new features and enhancements designed to help make cloud native enterprise storage simpler and more accessible to the cloud native community. For existing users of Longhorn, this latest release is focused on helping you build better value and resiliency across your storage strategy.
How To Incorporate FinOps Into The DevOps Lifecycle
Power-up your local development with DDEV
Have you ever had to set up and/or maintain a local development environment using Docker that mirrors your production environment as much as possible? Setting-up and supporting such a docker-based local environment is no easy feat! Common problems include: performance issues, broken dependencies, broken relationships between your services and uncontrolled updates of your docker images, among many other issues. So, the question is, what can we do about that?
MetricFire Platform Overview
An Introduction to Service Installer for VMware Tanzu
Build apps, not platforms: Optimized DevOps without platform engineering
Announcing HAProxy Data Plane API 2.7
HAProxy Technologies is proud to unveil the 2.7 release of HAProxy Data Plane API. This release was a huge undertaking, and as with the 2.6 release, we focused on extending support for configuration keywords. We are happy to announce that with this release we support all HAProxy configuration keywords in the Data Plane API. Along with enhanced keyword coverage, we’ve added the ability to specify multiple named defaults sections through the API.
Efficiently Managing Multiple Environments Using GitLab CI
Power-up Your Local Development with DDEV | Platform.sh
Have you ever had to set up and/or maintain a local development environment using Docker that mirrors your production environment as much as possible? Setting-up and supporting such a docker-based local environment is no easy feat! Common problems include performance issues, broken dependencies, broken relationships between your services and uncontrolled updates of your docker images, among many other issues. So, the question is, what can we do about that?
Artificial Intelligence vs. Machine Learning vs. Deep Learning
Spot Eco: Introducing a faster, more flexible dashboard
Kubescape brings a new level of security to Charmed Kubernetes
The popular open-source platform Kubescape by ARMO has been recently announced as a fully managed operator called a Charm for Canonical’s Charmed Kubernetes distribution. This collaboration between Canonical and ARMO is exciting for the solution it enables for end users, ultimately resulting in hardened and more secure Kubernetes environments.
Top 9 DevOps Monitoring Tools in 2023
DevOps has evolved in terms of its tools, techniques, and culture. Software developers can gain a completely new perspective when operations and development work together. The tech sector now depends heavily on DevOps. It is essential in enterprises, from software delivery to project planning. Businesses in DevOps employ a variety of monitoring tools for a range of activities, including development, testing, and automation.
Best AirDrop for Android Solution #shorts
Monitor Tanzu Kubernetes Grid on vSphere with Datadog
With vSphere and Tanzu Kubernetes Grid (TKG), VMware enables enterprise organizations to combine the economic advantages of virtual machines (VMs) with the agility, portability, and scalability provided by Kubernetes. vSphere is VMware’s platform for the provisioning and management of VMs.
Best Practices to Ensure Sustainable, Enterprise-Wide Open Source Software Adoption
Over the past two decades, adoption of open source software (OSS) among enterprises has become commonplace. In fact, because of the many advantages of open source, it is now almost impossible to find a business that does not rely on OSS. And with the proliferation of modern cloud native apps and microservices, this is only more true. Modern applications are built with open source, and you wouldn’t want to do it any other way.
JFrog Quick Tip How to install and connect the JFrog CLI
Spot Security - Understand your Cloud Security Posture
Cloud Monitoring: Create custom notification channels
8 Best Endpoint Management Solutions
Most modern organizations would benefit from the use of an endpoint management solution. Any business that uses computers, printers, tablets, or other such IT devices -- the titular endpoints -- need an efficient and reliable way to maintain, monitor, and secure those devices.
Terraform With Multiple Environments: Key Benefits & Use Cases
How To Manage Multiple Environments With Terraform in 2023
How to use the Grafana Ansible collection to manage Grafana Agent across multiple Linux hosts
Anyone who is trying to set up monitoring for multiple machines knows how tough it can get to manage multiple Grafana Agents across them. To make things easier, we recently added the Grafana Agent role to the Grafana Ansible collection, which will help users manage the Agent across multiple Linux hosts. (Need to know how to get started with the Grafana Ansible collection for Grafana Cloud?
Civo January 2023 Newsletter
With less than one month to go, we are counting the days until our first Civo Navigate event in Tampa Bay, Florida. Mark Boost, CEO of Civo, recently explored the motivation behind Civo Navigate, what attendees can expect, and the industry reaction in our blog. If you're joining us for the event, why not check out the Synapse Florida Summit? You can use code "CIVO" to get a 10% discount on all Synapse Summit tickets here.
Security in the smart home: considerations for device makers
When people think of home security they usually think of an alarm system with a keypad next to the door. These days, however, home security should have two meanings. I’m here to talk about the second: cybersecurity. In other words, security in the smart home.
Simplifying Kubernetes DevSecOps Through Platform Engineering
DevSecOps–short for development, security, and operations–is a trending practice that introduces security testing, triage, and risk mitigation as early as possible in the software development lifecycle, rather than bolting on security in the final stages. DevSecOps requires a shift (also known as “shift-left”) in culture, process, and tools across development, security, and operations teams to make security a shared responsibility.
2022 at Cortex: A year in review from our CTO
Playbooks: A new superpower for designers
From one designer to another, you should know why Playbooks is a fantastic addition to your design tool belt. Playbooks were designed with technical workflows in mind, from incident response to release management, but its flexibility makes it a perfect fit for any repeated process. I love it for creating reusable templates of design checklists and an excellent way to do design review sign-off.
Failure Analysis: Engineering incidents are a bigger problem than you think
Why SRE Benefits Your Organization's Teams & Your Customers
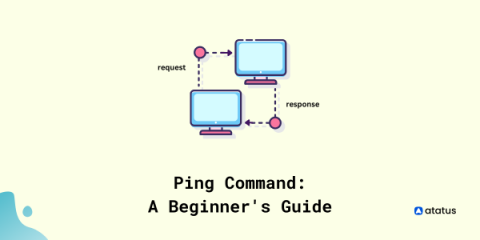
Ping Command: A Beginner's Guide
One of the most continually used tools by network administrators is the ping command. Over a half-century has passed since it was unleashed, and unsurprisingly, it has proven effective in troubleshooting networks. Testing the availability of a networking device on a network (mostly computers) can be done by employing the ping command. In order to check the connectivity between hosts and servers, the PING (Packet Internet Groper) command is utilized.
CircleCI Breach: How to Rotate All Stored Secrets ASAP
Yesterday, CircleCI, a Continuous Integration/Continuous Delivery (CI/CD) service, notified the world it had been breached via a critical advisory from its CTO. As a major software delivery pipeline service, CircleCI users store myriad credentials for various services in CircleCI’s “Secrets Store” infrastructure.
Critical Metrics and Alerts in the Continuous Delivery Process
Continuous delivery is a software development approach in which code changes are automatically staged for production release. A foundation for modern application development, continuous delivery extends continuous integration by automatically deploying code changes to test and production environments after the build phase. When properly implemented, developers have deployable build artifacts that have passed a standardized testing process and can be deployed to environments as needed.
View and Access iPhone Photos from a PC without iTunes or iCloud #shorts
Puma + Sleuth = The Swiss Army Knife of Deployment Pipeline Orchestration
A Fully Argo-Based Ecosystem For Continuous Delivery and Deployment
Better DevOps makes for more efficient engineering teams and more reliable releases, and when it comes to DevOps, it doesn’t get better than GitOps. According to DevOps-As-A-Service: One of the many goals of DevOps is to reduce Time To Value (TTV) and to provide faster feedback while enabling developers to easily self-service or not have to engage to get a service at all.
Realtime performance alerts for cloud desktops
DataOps vs. DevOps - Similar or Completely Different?
Join Rotem Refael from ARMO
Managed Service Providers (MSPs): How Can They Help Scale Your Business?
The A to Z of Devices You Can Remote Control
When most professionals hear the term “mobile device management,” they generally assume that an MDM can only remote control company-issued phones. Several years ago, this idea may have been accurate. But as the digital devices in our world have exploded in number, so, too, has the umbrella of what an MDM can remotely control. Now the right MDM can remote control practically any device with a screen and an interface.
Encouraging Employee Movement and Growth Benefits Everyone
From hybrid work opportunities to celebrating milestones, we share best practices from our experience.
5 open source projects to contribute to in 2023 | Open Source Matters
Welcome to Open Source Matters, where we cover the latest developments in open source technology. In this special edition, we’re covering 5 open source projects you should consider contributing to in 2023. I’m your host, Ben Lloyd Pearson — now, in no particular order, let’s dive in!
WSL and Ubuntu: 2022 year in review
In 2022, Windows Subsystem for Linux (WSL) exploded in popularity, with millions of users taking advantage of the ability to develop, create and administrate inside a native Linux environment deeply integrated with Windows. This is thanks in large part to continued investment from Microsoft, consistently rolling out new features and updates for the platform on both Windows 10 and Windows 11.
Cloud security: How remote work created a new problem
Amazon Sagemaker Pricing Explained: A Guide For 2023
Zero Trust for Kubernetes Environments (D2iQ + Thales TCT)
GitOps The Planet (E4) | GitOps at Edge
The State of AIOps: A New Years' Message from Chief Moo Phil Tee
Well, that was fast! Another year has come and gone. It is safe to say 2020, ‘21 and ‘22 were exceptional, and only sometimes for good reasons. But I take heart in society’s steady progress toward digital maturity through it all. Nearly 100% of IT leaders say the pandemic accelerated their organization’s rate of digital transformation.
5 Open Source Projects To Contribute to in 2023 | Open Source Matters
Top 5 challenges in Hyper-V performance monitoring that you need to know
A better way: 3 incident response areas prime for automation
By automating some rote parts of incident response, you reduce decision fatigue and help responders get to solving the problem faster with less stress. In this post, we talk about three areas of the incident response process that are prime for automation.
How communication can make or break your incidents
In this episode, Pete and Lisa discuss why great communication (both internally and externally) is essential to the success of any incident management process. From keeping your wider team in the loop to minimise disruption, to using customer communication to strengthen your brand when things go wrong, the team share their experiences and top tips for having a transparent incident communication culture.
Kubernetes Monitoring: 4 Data Types to Increase Insights
Having a deep understanding of a Kubernetes cluster is important: the right insights allow you to monitor the performance and health of the cluster, which is necessary for ensuring that applications are running smoothly and that any potential issues can be identified and addressed quickly. As your Kubernetes cluster develops, so does the need for monitoring and troubleshooting.
DevOps Security: Challenges and Best Practices
With the shift from traditional monolithic applications to the distributed microservices of DevOps, there is a need for a similar change in operational security policies. For example, how do you secure a disparate number of micro-systems operating with multiple access credentials across a multi-level organization? DevSecOps (Devops security) answers this question by integrating security at every level of your development process.
The Optymyze CEO Explains 5 Ways To Automate Your DevOps Workflow
The 7 Best FinOps Blogs, Books, And Other Resources
Hybrid cloud infrastructure modernisation
Public clouds enabled digital transformation at unprecedented speed. But their operational costs over time can be exacting as compute needs increase. Hybrid clouds emerged as an alternative to gain the benefits of both worlds: private infrastructure that allows for lower operational expenditures and tighter control, and public clouds that can scale with ease.
Microservices Monitoring: Cutting Engineering Costs and Saving Time
As businesses are planning for 2023, many are adopting a more conservative mindset when it comes to their resources. In light of the recent market fluctuations and the uncertainty of if and how a recession will affect them, they are looking for ways to cut costs and increase their efficiency. But despite the spending slowdown, development velocity can’t slow down.