AWS ECR Scanning with Sysdig Secure
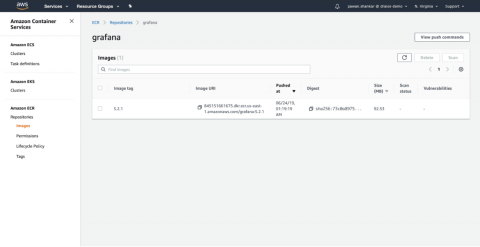
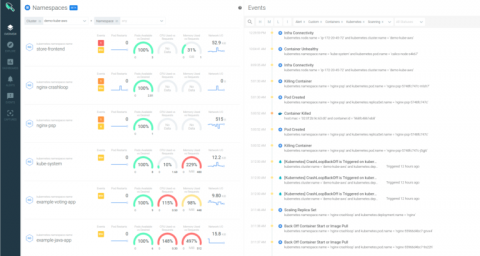
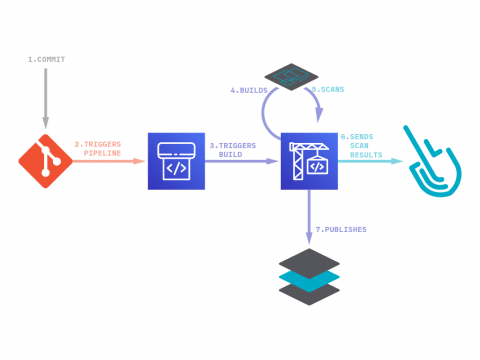
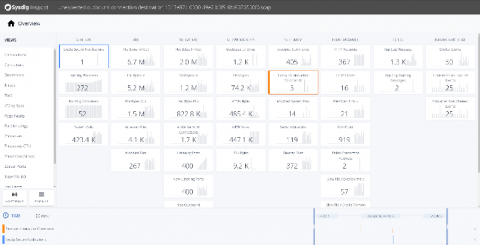
As container adoption in AWS takes off, ECR scanning is the first step towards delivering continuous security and compliance. You need to ensure you are scanning your images pulled from AWS ECR for both vulnerabilities and misconfigurations so that you don’t push applications running on AWS that are exploitable.