Risk Management for Enterprise System Migration Project
Migrating enterprise systems is considered one of the riskiest things a company can do. New system developments are considered less risky mainly because teams design the system considering the new constraints; whereas in case of migration, one has to deal with all the backlogs of technical debt, overlooked dependencies, and convoluted business processes which have been taking advantage of old infrastructures for a long time.
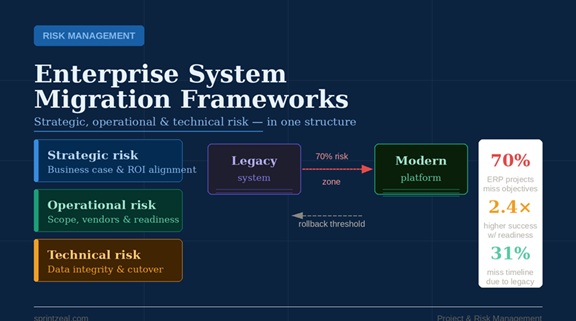
The numbers reflect this complexity. According to Gartner's 2025 analysis, 70% of ERP implementations fail to meet their stated objectives, and 25% fail catastrophically. Even when migrations don't collapse entirely, McKinsey reports that inefficiencies in data migration cost enterprises 14% more than their planned spending, and 38% of companies experience delayed migration efforts by over a quarter. These outcomes aren't inevitable — they are, in most cases, the product of risk management applied too late, too narrowly, or structured around the wrong framework.
Knowing the scope of a legacy system migration, whether it is lifting and shifting cloud moves or full platform replacement, is really the first step of developing a reliable risk strategy. The decision of the technical approach dictates which risk categories will be the main focus, how long the project expected to last, and where different regulatory authorities are necessary. Failing to this will result in risk registers that turn out to be some kind of theoretical exercises which are far from the reality of failure.
Why Standard Risk Frameworks Fall Short in Migration Contexts
Most enterprise project teams apply risk management methods drawn from PMI's PMBOK® Guide or ISO 31000 without modification. Both are sound frameworks in general project contexts. Both tend to underperform in system migrations.
The reason is category depth. Generic frameworks treat "technical risk" as a single line item, when migration risk is better understood as a cluster of at least four distinct sub-categories: data integrity risk, integration continuity risk, service availability risk, and organizational change risk. Collapsing these into a single register entry produces a response plan that is either too vague to action or, more commonly, assigns ownership to the wrong team.
Consider how a manufacturing company discovered that their inventory data was so corrupted during migration that they couldn't trust basic stock levels — products listed as available didn't exist, while items marked as discontinued were their best sellers. The ERP system itself functioned correctly. The failure was a data integrity risk that had not been scoped, owned, or tested. No amount of technical architecture review would have caught it without a dedicated data risk stream operating independently of the delivery team.
A Layered Risk Framework for Migration Programs
Effective risk management for enterprise migrations is about managing risks on three different levels at the same time: strategic, operational, and technical. Consider them as a sequence of phases, analyze, then prepare, then implement, is actually a risk in itself. Instead, all three must be done concurrently, with proper communication between them.
Strategic Risk: The Business Case Layer
Strategic risks are risks through which the migration's purpose can be negated. For example, the migration may be addressing an issue that no longer exists or being done based on assumptions about user adoption that have not been validated. Domain 1, Risk Strategy and Planning, of the PMI-RMP framework is a good fit for this. It is the step where a program sponsor identifies what business failure means in concrete terms: a contractually binding go-live date, zero downtime in a highly regulated environment, or cost limit that will lead to executive involvement. Risk responses end up being aligned with what the project team can bear rather than what the business needs. In simple words
Operational Risk: The Delivery Layer
Operational risk factors are those which hinder operations, scope creep, vendor dependencies, out-of-stock of human resources, and forced shortening of testing windows right before go-live are examples. IDC data shows that 31% of migration projects overrun schedule, complexity of legacy systems being the leading factor. Late emergence of a scoping problem is often mistaken for a scheduling problem.
The best operational risk management option for migrations is organizing a pre-migration readiness assessment quite thoroughly. The organizations that carry out a readiness assessment in advance of migration are likely to achieve success by a factor of 2.4. The assessment should focus three aspects: the level of data quality and completeness in the source system, extent of documentation of current integrations, and the ability of the organization to administer dual operations during transition.
Closeness of delivery models to Agile cause introduction of an operational risk that needs to be highlighted: rapid, sprint-based work cycles exert pressure to treat migration workstreams as features that can be descoped. They are not. Whereas a new feature can be deferred to a later one, the migration has to either be done as a whole or remain undone. Risk management should explicitly shield migration-critical workstreams from sprint-level prioritization decisions.
Technical Risk: The Architecture Layer
Technical risk in migrations divides cleanly into two phases: pre-cutover and post-cutover. Before go-live, the dominant risks are data loss, integration failure, and environment mismatch — all of which are discoverable through disciplined testing. After cutover, the risk profile shifts to performance degradation under production load, edge-case failures in business logic, and the organizational stress of users operating an unfamiliar system on production data.
TOGAF's Architecture Development Method (ADM) provides a useful structure for technical risk governance in this phase. The Opportunities and Solutions phase of the ADM explicitly requires architects to assess risk across current and target state architectures before any implementation begins — a step that many migration programs skip in the rush to start building. The ADM also mandates a formal Architecture Contract, which creates documented, auditable commitments between the project team and the business stakeholders on what the target state will and will not deliver.
One underused technical risk control is the rollback threshold — a pre-defined, agreed condition that automatically triggers a return to the legacy environment rather than forcing a real-time escalation decision during cutover. Industry data shows that 18% of migration projects require rolling back at least some workloads due to performance, cost, or compatibility issues. Organizations that define rollback criteria before go-live recover faster and with less business disruption than those that make rollback decisions reactively.
Risk Ownership: The Governance Gap
One thing you see again and again in post-migration reviews: people spot the risks, but nobody actually owns them. Companies have risk registers, but the so-called responsible parties either can’t do anything about the risks or don’t even know they’re supposed to. PMI-RMP calls this a failure to get stakeholders involved — specifically, Domain 2 zeros in on actually engaging people in risk management through back-and-forth conversations, not just blasting out notifications.
When you look at migration programs, this means you need to bake it into your governance — every risk bucket (stuff like data integrity, system integration, keeping services running, or managing organizational change) needs a person’s name on it. Not just for show, either: that person has to actually have the power to hit pause or escalate if things go sideways. It sounds like a small thing, but it changes everything. Because if you give someone the title without the authority, you’re setting things up so that failure gets formally documented, but no one can actually step in and deal with a crisis — even if everyone saw it coming.
Quantitative Techniques That Change Decision Quality
Now, on the tools side: most migration programs start with the basics. Teams get together, fill out risk grids with high/medium/low ratings, then pretty much leave it there. That’s fine early on, but it doesn’t cut it when you’re making big calls — like picking vendors, setting go-live dates, or flipping the actual switch.
To really improve your decisions, you need a couple of quantitative techniques. Monte Carlo simulations, for example, model how costs and timelines might play out over thousands of possible scenarios. You don’t just get a single best guess — you get a range that lays out the odds, like, “We’ve got a 75% chance of staying within budget, but there’s still a 25% shot we’ll overshoot by 20–30%.” That’s the kind of detail leaders can actually use: do we roll with these odds, build in more buffer, or rethink the plan entirely?
Expected Monetary Value (EMV) analysis forces explicit costing of risk responses. Rather than selecting mitigation strategies based on effort or preference, EMV calculates the expected financial impact of each risk and compares it against the cost of the response — revealing which mitigations are worth their investment and which are organizational theater. For programs where cost overruns like Birmingham City Council's Oracle ERP implementation ballooning from £46M to £114M are the reference case, the discipline to quantify risk response ROI is not optional.
Connecting Risk Management to Migration Approach Selection
Risk frameworks don't operate independently of the technical choices made at the program's outset. A lift-and-shift migration to the cloud carries a fundamentally different risk profile than a full platform replacement. The former preserves existing business logic at the cost of carrying technical debt forward; the latter eliminates debt but introduces extensive retraining, process change, and integration re-engineering risk.
Organizations using a dedicated migration services provider report a 71% on-time completion rate — a figure that reflects not just technical capability but the risk governance structures that experienced providers bring to complex programs. The choice of approach should be informed by risk appetite, not just by technical preference or cost.
Conclusion
Enterprise system migration risk management requires more than applying a generic project risk framework to a technically complex initiative. It requires structured risk categorization, layered governance across strategic, operational, and technical domains, named ownership with real authority, and quantitative analysis at decision-critical points. Organizations that invest in this structure before migration execution begins consistently outperform those that treat risk management as a compliance activity running alongside delivery.
For risk management professionals targeting the PMI-RMP certification, migration programs represent one of the richest real-world contexts in which every domain of the PMI-RMP ECO — from risk strategy to specialized quantitative analysis — applies simultaneously. Building expertise in this domain is both exam preparation and directly deployable practice.