Empower your team to resolve network issues-hours faster
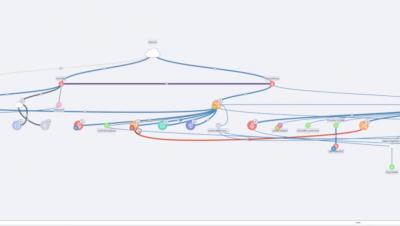
Network troubleshooting without Auvik is like trying to find a needle in a haystack. But with Auvik’s network monitoring and management software, you can quickly identify possible root cause devices, dig deep into device interfaces, and remote into the device to troubleshoot the issue. Problem solved.