Operations | Monitoring | ITSM | DevOps | Cloud
Threat Detection
Bullet-Proofing Serverless Infrastructures with Failure and Threat Detection
When building cloud-based systems and serverless systems, in particular, it’s crucial to stay on top of things. Your infrastructure will be miles away from you and not a device you hold in your hands like when you build a frontend. That’s why adding a monitoring solution to your stack, which offers a pre-configured serverless failure detection, should be one of the first decisions.
Secure Your Endpoints with Sophos & Logz.io
Intercept X is Sophos’ endpoint security solution, including anti-ransomware, zero-day exploit prevention, plus managed endpoint defense and response. It employs a layered approach reliant on multiple security techniques for endpoint detection and response (EDR). Those tactics include app lockdown, data loss prevention, web control and malware detection.
Runtime Threat Detection on AWS
How to Enable Detection Rules via Elastic Security - Version 7.10
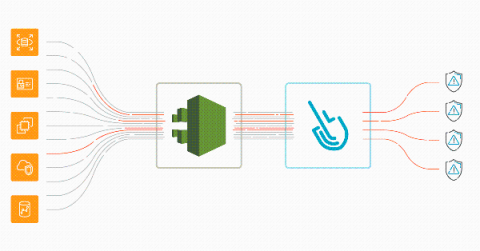
AWS threat detection using CloudTrail and Sysdig Secure
Implementing AWS threat detection with Sysdig Secure takes just a few minutes. Discover how to improve the security of your cloud infrastructure using AWS CloudTrail and Sysdig Cloud Connector. With the rise of microservices and DevOps practices, a new level of dangerous actors threatens the cloud environment that governs all of your infrastructure. A malicious or inattentive cloud API request could have a sizable impact on availability, performance, and last but not least, billing.
Using Private Threat Intelligence Feeds on Hidden Security Attacks with Logz.io
Oftentimes, security attacks that were clearly recorded in logs go unnoticed. They are obscured by a large sea of log data created by most modern cloud environments. In some cases, like during a DDoS attack, there will be a huge spike in logs so it will be very clear what happened. In other situations, just a few logs will document the attack. Finding these logs can be like finding a needle in a hay stack. But if you know what to looks for, it doesn’t need to be so hard to spot these attacks.
Guard Your Business Like a Warrior with These 10 Tools
Cybersecurity has been a core issue in business management and growth. As businesses try to manage more remote teams, it’s important now more than ever. With technology becoming an integral part of our everyday lives, we’re exposed to an ever-growing risk of cyber-attacks and malicious technological crimes. According to a recent study, on average, hack attacks occur every 39 seconds. That is, one in three Americans is a victim of cybercrime every year.
Practical security engineering: Stateful detection
Detection engineering at Elastic is both a set of reliable principles — or methodologies — and a collection of effective tools. In this series, we’ll share some of the foundational concepts that we’ve discovered over time to deliver resilient detection logic. In this blog post, we will share a concept we call stateful detection and explain why it's important for detection.