Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
Deploy an Ingress Controller on K3s
Kubernetes provides a powerful networking model for microservices. One of the pillars of this model is that each pod has its own IP address and is directly addressable within the cluster. As a consequence, each Kubernetes cluster usually has a flat virtual network that external hosts can’t reach directly. That means routing traffic from clients outside the cluster to services deployed inside the cluster requires some additional work.
Sysdig Cuts Container and Kubernetes Visibility and Security Onboarding to 5 Minutes
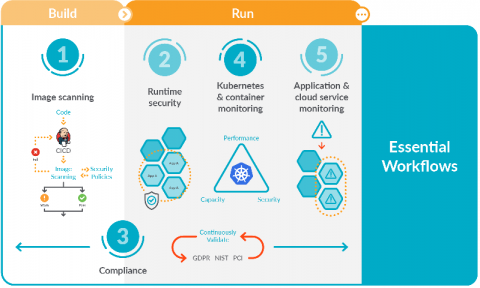
5 Essential workflows for secure DevOps
Focusing on these five essential workflows for secure DevOps will help you get started implementing monitoring, security, and compliance for containers and Kubernetes. You might be starting to adopt DevOps and find that it dramatically simplifies deploying applications in containers and Kubernetes. However, you probably also found that it adds a new set of complexities for managing, securing, and troubleshooting applications.
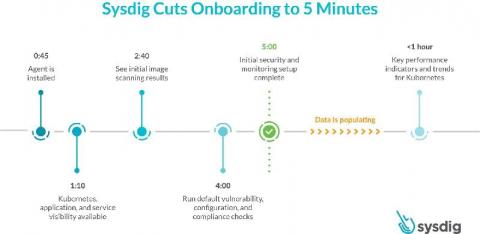
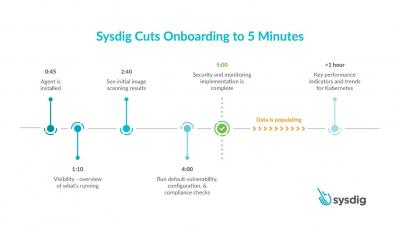
Sysdig cuts onboarding for container and Kubernetes visibility and security to 5 minutes
Today, we are excited to announce a faster onboarding for Kubernetes visibility and security. With the SaaS-first approach and new enhancements to the Sysdig Secure DevOps Platform, you can get results after just a five-minute setup. This release includes a new guided onboarding process, out-of-the-box dashboards as part of curated essential workflows, and a new Sysdig Essentials tier. 5 minutes to onboard secure DevOps - YouTube An error occurred.
Getting started with secure DevOps
Connecting the World's Travel Trade with Kubernetes
When you book a hotel online or with a travel agent, you’ve probably got a wish list that has to do with the size of the room, view, location and amenities. You’re probably not thinking about the technology in the background that makes it all happen. That’s where Hotelbeds comes in. The business-to-business travel technology company operates a hotel distribution platform that travel agents, tour operators, airlines and loyalty programs use to book hotel rooms.