Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
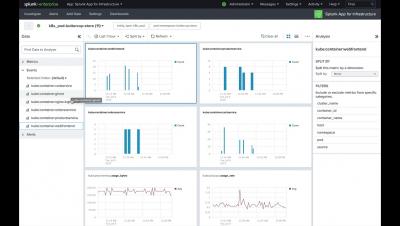
Best Practices for Automating Monitoring
Developer teams and even operational teams often ignore monitoring applications. Deadlines, inexperience, company culture, and management can lead to poor or neglected monitoring inside developing platforms. Automating all monitoring tasks is an excellent way to avoid this scenario. Automation leads to lower costs, less time spent solving issues, and more efficient teams.
Intro to Rio Online Training: The MicroPaaS for Kubernetes
How Kubernetes works
It's no secret that the popularity of running containerized applications has exploded over the past several years. Being able to iterate and release an application by provisioning its dependencies through code is a big win. According to Gartner, “More than 75% of global organizations will be running containerized applications in production” by 2022.
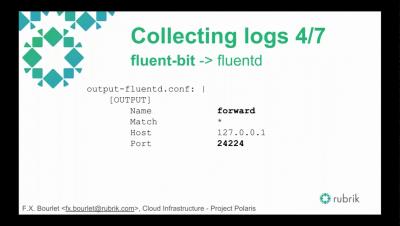
Container Logging with Logz.io and the ELK Stack
Tigera Secure 2.5 - Implement Kubernetes Network Security Using Your Firewall Manager
We are excited to announce the general availability of Tigera Secure 2.5. With this release, security teams can now create and enforce security controls for Kubernetes using their existing firewall manager.
Monitoring Amazon Classic Elastic Load Balancers with Blue Matador
AWS Elastic Load Balancing is one of the most widely used of Amazon’s cloud services. In many AWS stacks, an Elastic Load Balancer (ELB) will be involved in almost every single request that customers make to your application. Since they are critical to the health of your application, properly monitoring ELBs is a top priority for most teams. In this blog post, we will go over how Blue Matador monitors Classic Elastic Load Balancers automatically and without configuration.
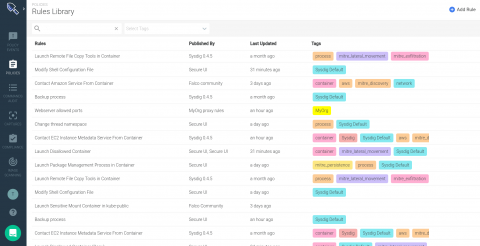
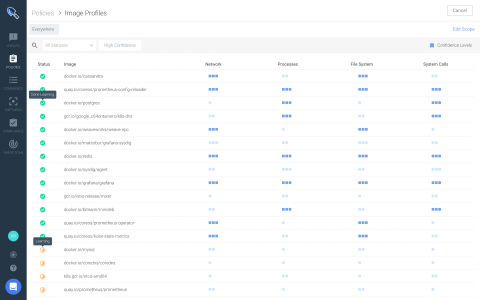
Introducing the new Sysdig Secure policy editor
Among many other features Sysdig Secure version 2.4 introduces a new and improved runtime policy editor, along with a comprehensive library combining out-of-the-box run-time policies from our threat research teams, container-specific compliance standards, Kubernetes security and Falco opensource community rules.
Sysdig Secure 2.4 introduces runtime profiling for anomaly detection + new policy editor for enhanced security.
Today, we are excited to announce the launch of Sysdig Secure 2.4! With this release, Sysdig adds runtime profiling to enhance anomaly detection and introduces brand new interfaces that improve runtime security policy creation and vulnerability reporting. These features are focused on upgrading the experience of creating your security policy to detect security threats and attacks to your infrastructure and apps.