Operations | Monitoring | ITSM | DevOps | Cloud
SIEM
Top 3 SIEM Optimizations - How to Get More From Your Existing Tech Stack
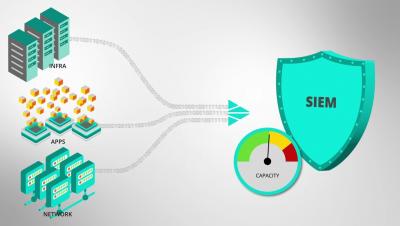
In today’s digital-first world, most security problems are actually data problems, and data volumes are outpacing organizations’ abilities to handle, process, and get value from it. You’ll have 250% more data in five years than you have today, but the chances of your budget increasing to match that are slim. The challenges that come with managing the rise in enterprise data volume directly affect your ability to adequately address cybersecurity risks.
SIEM Tools: For Enhanced Threat Intelligence and System Security
SIEM is an overarching mechanism combining Security Event Management (SEM) and Security Information Management (SIM). It is a combination of different tools such as Event Logs, Security Event Logs, Event Correlation, SIM etc. These work in tandem to provide you an up-to-date threat intelligence infrastructure and enhanced security for your applications and hardware.
SIEM Optimizations with Cribl Stream
Getting Started with Logz.io Cloud SIEM
The shortcoming of traditional SIEM implementations can be traced back to big data analytics challenges. Fast analysis requires centralizing huge amounts of security event data in one place. As a result, many strained SIEM deployments can feel heavy, require hours of configuration, and return slow queries. Logz.io Cloud SIEM was designed as a scalable, low-maintenance, and reliable alternative. As a result, getting started isn’t particularly hard.
How to Cut Through SIEM Vendor Nonsense
If you’re in need of new SIEM tooling, it can be more complicated than ever to separate what’s real and what’s spin. Yes, Logz.io is a SIEM vendor. But we have people in our organization with years of cybersecurity experience, and they wanted to share thoughts on how best to address the current market. Our own Matt Hines and Eric Thomas recently hosted a webinar running through what to look out for titled: Keep it SIEM-ple: Debunking Vendor Nonsense. Watch the replay below.
How to choose and track your security KPIs
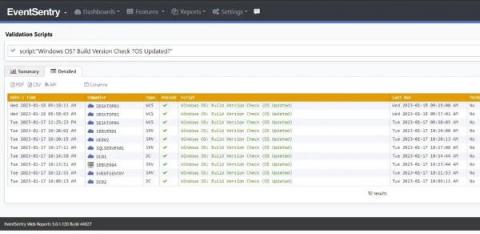
The Life of the Sysadmin: A Patch Tuesday Story
The System Administrator! AKA the Sysadmin. The keeper of the network, computers – well basically all things technology. The one who is hated for imposing complex passwords and other restrictions, but taken for granted when everything works well. They are the first to be called when “facebuuk.com” reports: “domain does not exist”.
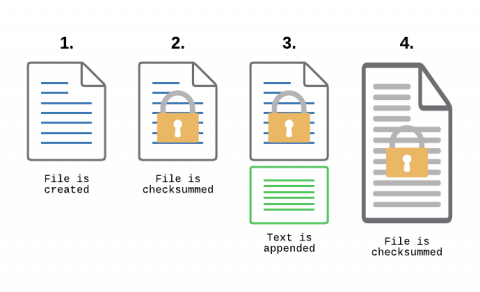
Monitoring Transaction Log Files for PCI compliance
File Integrity Monitoring, aka as FIM, is a must-have feature for anyone in charge of security. With FIM, one can detect when a critical file, such as a file that belongs to the Operating System, or a key configuration file, is changed. In most cases, configuring FIM is straightforward: If the file changes then generate an alert.
SIEM-pler Migrations with Cribl Stream
A SIEM (Security Information Event Management) platform, along with several other tools that make you crave Alphabet Soup (XDR, UBA, NDR, etc), is a critical component of any organization’s security infrastructure. Between a constantly growing volume of logs, increasing attacks and breaches, and challenges finding qualified staff, many organizations may consider a SIEM migration. There could be several reasons for this.