Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
How to View Logs in Kubectl
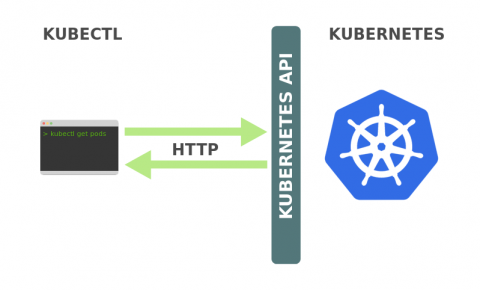
Kubernetes has become the de-facto solution for container orchestration. While it has, in some ways, simplified the management and deployment of your distributed applications and services, it has also introduced new levels of complexity. When maintaining a Kubernetes cluster, one must be mindful of all the different abstractions in its ecosystem and how the various pieces and layers interact with each other in order to avoid failed deployments, resource exhaustion, and application crashes.
Protection from malicious Python libraries jeilyfish and python3-dateutil
Two malicious Python libraries, jeilyfish (with a capital i and a lowercase L in the original name) and python3-dateutil, were detected on PyPI (Python Package Index) on December 1st. They were typosquatting similar named legitimate libraries jellyfish (with a double lowercase L) and python-dateutil libraries, a malicious technique aiming to trick developers to use the similar named modified libraries.
Five Ways to Quickly Uncover Malicious Activity and Protect Your Kubernetes Workloads
Organizations are rapidly moving more and more mission-critical applications to Kubernetes (K8s) and the cloud to reduce costs, achieve faster deployment times, and improve operational efficiencies, but are struggling to achieve a strong security posture because of their inability to apply conventional security practices in the cloud environment. Commitment to cloud security grows, but security safeguards are not keeping up with the increased use of the various cloud platforms.
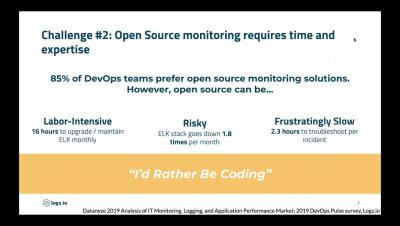
Simplified Monitoring for AKS Deployments with Logz io
Getting Started with Kubernetes using MicroK8s
Single-node deployments of Kubernetes are more common than what one would expect. In some scenarios, single-node clusters make much more sense. For development purposes or testing, there’s no need to deploy a full-blown production-grade cluster. Single-node deployments are also handy for appliances and IoT applications since they have a much smaller footprint. Enter MicroK8s, a tool by Canonical that enables you to easily deploy a lightweight single-node cluster in your local environment.