Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
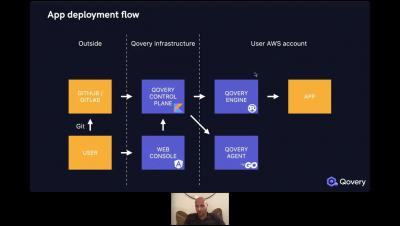
How we extended Helm lifecycle with Rust
Helm has some limits, discover how we extended functionnalities with Rust.
Five Kubernetes Deployment Best Practices (Part 2)
In our previous post , we focused on tips for making the transition and migration to Kubernetes a smoother, and less painful process. In this post, we’d like to now provide some tips from the operational trenches for future-proofing your Kubernetes operation, after making the move. Kubernetes, as a software-driven system, has many benefits for engineers and DevOps teams to take advantage of.
Four Best Practices to Migrate to Kubernetes (Part 1)
Kubernetes has evolved into the leading platform to build your microservices systems. Given its increased maturity over the past few years as well as the robust ecosystem which has been built around its technology, Kubernetes has become more production-ready than ever. Nevertheless, it still has its own unique set of challenges. In particular, it brings a lot of complexity into play with its adoption.
Fast and simple troubleshooting with GUI-based Dynamic Packet Capture
With the Calico 3.10 release, Dynamic Packet Capture is available in Dynamic Service Graph. This means users who require self-service, live troubleshooting for microservices and Kubernetes workloads can capture and evaluate traffic packets on endpoints without writing a single line of code or using any 3rd-party troubleshooting tools. Users don’t need to learn about or have knowledge of kubectl or YAML to troubleshoot their microservices and Kubernetes cluster.
Docker: Run Telegraf as non-root
The Telegraf 1.20.3 release changed the official Telegraf DockerHub image to no longer run the Telegraf service as root. With this change, the Telegraf service runs with the least amount of privileges in the container to enhance security given the wide extensibility and array of plugins available in Telegraf.
Why the creators of K3ai use Civo Kubernetes
Open Source for Better Observability
Monitoring cloud-native systems is hard. You’ve got highly distributed apps spanning tens and hundreds of nodes, services and instances. You’ve got additional layers and dimensions—not just bare metal and OS, but also node, pod, namespace, deployment version, Kubernetes’ control plane and more. To make things more interesting, any typical system these days uses many third-party frameworks, whether open source or cloud services.
Learn How to Simplify Kubernetes Performance Management | Pepperdata
Label standard and best practices for Kubernetes security
In this blog post, I will be talking about label standard and best practices for Kubernetes security. This is a common area where I see organizations struggle to define the set of labels required to meet their security requirements. My advice is to always start with a hierarchical security design that is capable of achieving your enterprise security and compliance requirements, then define your label standard in alignment with your design.