Operations | Monitoring | ITSM | DevOps | Cloud
Vulnerability
How We Used Our Own Platform Capabilities to Prevent Log4j Attacks and Protect Customers
In December, information security researchers discovered a serious vulnerability in the popular open-source logging library, Log4j. If exploited, this vulnerability, known as Log4Shell, could allow malicious attackers to execute code remotely on any targeted computer. Millions of computers use Log4j. According to one study, 93% of all cloud environments are affected by the vulnerability.
How To Detect and Prevent Zero-Day Vulnerabilities With Smart Infrastructure Monitoring Tool
“End of life, end of support, pandemic-induced shipping delays and remote work, scanning failures: It’s a recipe for a patching nightmare.”, federal cybersecurity CTO Matt Keller says. Ensuring a high level of security for your IT infrastructure and being sure you have not missed something is hard to arrange during these days. A zero-day exploit happens when hackers identify a software weakness or a security gap and take advantage of it to perform a cyberattack.
Log4j vulnerability highlights the value of a combined security and observability approach
When we launched AppDynamics with Cisco Secure Application in early 2021, it was the industry’s first integrated application performance management (APM) and runtime application security offering. We made a bold bet that consolidated monitoring would become increasingly important and provide significant benefits such as improved security capabilities and reduced costs. It was the right bet.
CVE-2021-44521 - Exploiting Apache Cassandra User-Defined Functions for Remote Code Execution
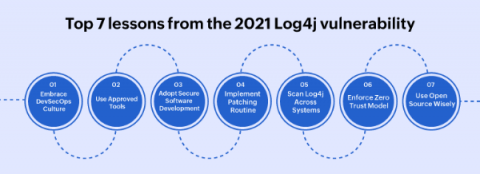
Top 7 lessons from the 2021 Log4j vulnerability
The Log4Shell (CVE-2021-44228) zero day vulnerability in the Java logging framework Log4j (versions 2.0 to 2.14.1) was revealed on December 9, 2021. The Apache Foundation assigned the maximum CVSS score of 10 to Log4Shell, as millions of servers and potentially, billions of devices came under risk. Security professionals around the world began patching the vulnerability, and scanning their systems to rule out any potential breach.