Operations | Monitoring | ITSM | DevOps | Cloud
Security
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Going All In: Why Customer Zero Is the Ultimate Gift to Your Customers - and Your Own Team
Innovation in DevSecOps must keep pace with the speed of the dynamic, volatile modern cybersecurity environment. Yesterday’s solution worked beautifully…yesterday. What has it done for me today? Continual iteration and speed are paramount, but they’re not without risks. As a SaaS provider, how do you know that the latest evolution of your product works at scale? How do you know that it works at all?
Community Spotlight series: Calico Open Source user insights from Sr. Software Developer, Burak Tahtacıoğlu
In this issue of the Calico Community Spotlight series, I’ve asked Burak Tahtacioglu from ParkLab Technology to share his experience with Kubernetes and Calico Open Source. Let’s take a look at how Burak started his Kubernetes journey, and the insights he gained from Calico Open Source. Q: Please tell us a little bit about yourself, including where you currently work and what you do there. I am a Sr. Software Developer in our Developer Experience team.
How Ivanti Deters Malicious Threats in the Everywhere Workplace
Back in May of this year, Verizon published its 15th annual Data Breach Investigation Report (DBIR) for 2022 which states that 82% of breaches involved the human element, whether it is the user of stolen credentials, phishing, misuse, or an error, people are the biggest contributors to security incidents and breaches. The past several months has also resulted in numerous phishing attacks via corporate email and SMS text messages.
An Easy Guide To Protecting Your Passwords The Right Way
Why Torq's Momentum Mirrors the Exponential Adoption of No-Code Security Automation
In just three quarters since Torq was officially launched, our visionary team has delivered a 385% increase in customers, resulting in 360% quarter-over-quarter growth. We’ve also boosted our headcount by 150% and now have more than 100 technology integration partners, including Armis, Orca, SentinelOne, and Wiz. In addition, we recently opened new offices in the UK, Spain, and Taiwan
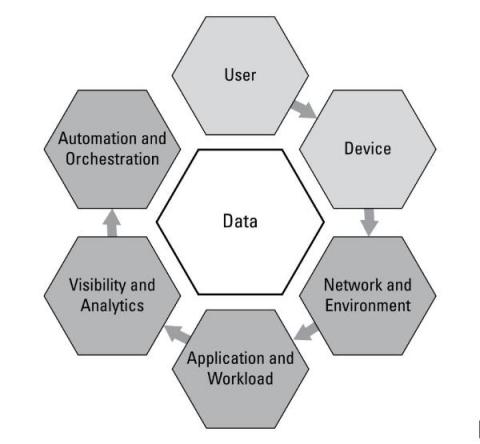
Zero Trust: The New Security Model for Cloud Native Applications and Infrastructure
Zero Trust security is gaining attention and momentum as a security approach or mindset that can improve the security posture of enterprises as they continue to battle hackers. Because of this widespread attention on Zero Trust, every software security vendor seems to be jumping on the Zero Trust bandwagon. However, Zero Trust is not a product or service. No single product or vendor can sell you Zero Trust security.
10 ways to make your software pipeline more observable
Ciara lists 10 ways to make your software pipelines more transparent and observable to gain insights, identify unusual behavior and possibly prevent a software supply chain attack.
SIEM-pler Migrations with Cribl Stream
A SIEM (Security Information Event Management) platform, along with several other tools that make you crave Alphabet Soup (XDR, UBA, NDR, etc), is a critical component of any organization’s security infrastructure. Between a constantly growing volume of logs, increasing attacks and breaches, and challenges finding qualified staff, many organizations may consider a SIEM migration. There could be several reasons for this.
How to Secure Your Data in the Cloud
We’ve entered a time when hard drives are becoming less important than data speeds, syncing, and remote storage. More and more end-users are saving their files in the cloud for convenience, safety, and cost savings. That said, some people still have concerns about cloud computing -- namely around security. How safe are files that are stored hundreds or thousands of miles away, on some other organization’s hardware?