Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
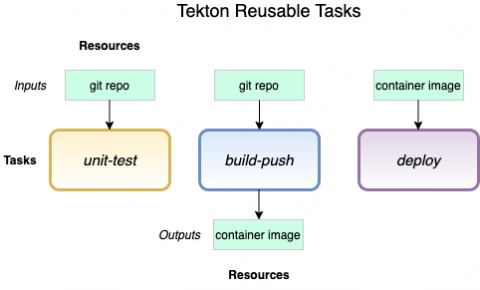
Securing Tekton pipelines in OpenShift with Sysdig
In this blog post, you’ll learn how to create a reusable Sysdig Secure image scanning task, for Tekton pipelines and Openshift clusters, that can be deployed in many pipelines. As a DevOps engineer, you want to deliver applications fast but keeping compliance with security standards like CIS, PCI DSS or NIST 800-190, GDPR can be an arduous task. You might implement image scanning in your CI/CD pipelines to detect and resolve issues such as known vulnerabilities and incorrect configurations.
Fighting COVID-19 One Kubernetes Cluster at a Time
Recently the leadership at Rancher Labs challenged all of us to think about ways we can contribute to the community during this current crisis. Coming up with ways to help in such an overwhelming situation is quite daunting. Since most needs are medical related, finding ways to apply software isn’t obvious. When I heard about Folding@home’s (FAH) efforts to reprioritize their computing resources toward COVID-19 research, I was immediately curious.
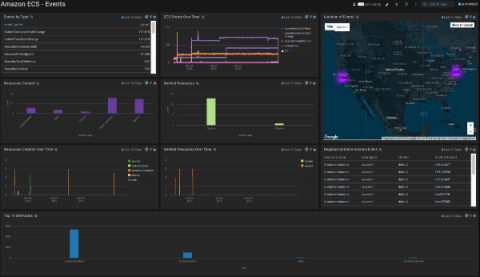
Monitor ECS applications on AWS Fargate with Datadog
AWS Fargate allows you to run applications in Amazon Elastic Container Service without having to manage the underlying infrastructure. With Fargate, you can define containerized tasks, specify the CPU and memory requirements, and launch your applications without spinning up EC2 instances or manually managing a cluster. Datadog has proudly supported Fargate since its launch, and we have continued to collaborate with AWS on best practices for managing serverless container tasks.
Deploy realtime GraphQL APIs in minutes with Qovery and Hasura
Hasura is an open source engine that connects to your databases & microservices and auto-generates a production-ready GraphQL backend. By using Hasura in conjunction with Qovery, you get a blazing fast, auto-scallable and extensible solution to quickly build your applications.
IBM Cloud Service Monitoring - Powered by Sysdig & Prometheus
Today Sysdig announced the availability of IBM Cloud’s new IBM Cloud service monitoring solution. The new capability – an extension of IBM Cloud Monitoring with Sysdig – provides pre-defined service metrics and dashboards for IBM public cloud services.
Where Are Docker Logs Stored?
Where are Docker container logs stored? There’s a short answer, and a long answer. The short answer, that will satisfy your needs in the vast majority of cases, is: From here you need to ship logs to a central location, and enable log rotation for your Docker containers. Let me elaborate on why with the long answer below.
Privacy Protections, PCI Compliance and Vulnerability Management for Kubernetes
Containers are becoming the new computing standard for many businesses. New technology does not protect you from traditional security concerns. If your containers handle any sensitive data, including personally identifiable information (PII), credit cards or accounts, you’ll need to take a ‘defense in depth’ approach to container security. The CI/CD pipeline is vulnerable at every stage, from build to ship to runtime.
Falco Support on AWS Fargate
Today we’re very excited to announce a partnership with Amazon to support Fargate in Sysdig’s product line. We are also announcing that Falco, the world’s most popular runtime security tool for containers, will soon be able to work on Fargate. This is an important milestone. For the first time, Fargate users will enjoy the benefit of deep instrumentation. This will make their workloads more secure, reliable, and efficient.
IAM Access in Kubernetes: How to Install Kube2iam
IAM is the de-facto method of authorization in AWS. Most Kubernetes “Quick Start” guides for AWS do not adequately cover how to manage IAM access in your pods. This blog series will first go over the security issues specific to AWS IAM on Kubernetes, then compare solutions, and then we will end with a detailed walkthrough for setting up your cluster with one of those solutions.