Operations | Monitoring | ITSM | DevOps | Cloud
Monitor webpages for changes with VisualPing
Frequent online shoppers, travel enthusiasts, parents seeking admissions for their wards, or the average online newsreader are all constantly plugged on to the Internet hoping to see the information they want updated on the respective websites. The only thing they can do is keep refreshing webpages and waiting for a change. Don’t you think that’s a waste of time and energy? You could instead be doing something more productive.
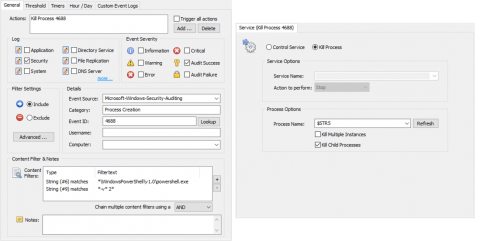
From PowerShell to p@W3RH311 - Detecting and Preventing PowerShell Attacks
In part one I provided a high level overview of PowerShell and the potential risk it poses to networks. Of course we can only mitigate some PowerShell attacks if we have a trace, so going forward I am assuming that you followed part 1 of this series and enabled: Module Logging, Script Block Logging, Security Process Tracking (4688/4689)
Rome Wasn't Built in a Day
At any given time, most cities have an ongoing infrastructure project that seems to take longer than necessary. Snarled traffic, endless lines of cars, and the ever present orange barrel. A sign has started appearing in those situations. It says "Rome wasn't built in a day. If it was, we would have hired those engineers." It’s clever way to remind people that progress requires patience. Similarly, great service provider businesses aren’t built overnight.
ManageEngine Tunes SIEM Solution to Simplify GDPR Compliance
Log360 Adds Prebuilt Report, Enhanced Data Breach Detection Capabilities to Streamline Enterprise Compliance with GDPR.
From PowerShell to P0W3rH3LL - Auditing PowerShell
Imagine someone getting the seemingly innocent ability to run a couple of commands on a machine on your network WITHOUT installing any new software, but those commands resulting in a reverse shell running on that same machine – giving the intruder a convenient outpost in your network. Now stretch your imagination even further and pretend that all of this happens without leaving any unusual traces in logs – leaving you completely in the dark.
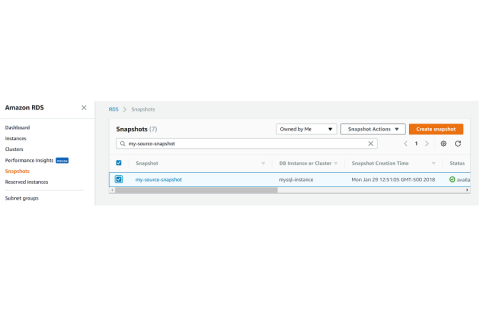
Copying RDS DB Snapshots
RDS DB snapshots are snapshots created from Amazon RDS DB instances. Those being MySQL, PostgreSQL, MariaDB, Oracle, and Microsoft SQL Server. Amazon Aurora also has snapshots, however, those are considered “cluster snapshots” and are handled differently.
Software Configuration Management: Patterns, Best Practices, and Tools for Agile and DevOps
Software configuration management (SCM) is a set of processes, policies, and tools that organize the development process. The goal of SCM is to improve the speed of and quality by catching errors early and enabling quick fixes when they occur. Understand how to define SCM and discuss how to accomplish it.
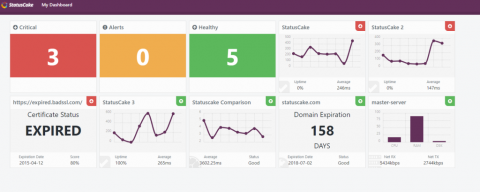
Feature Spotlight: Dashboards
Dashboards are pages which can show all your StatusCake operations in one place, from your uptime tests to your virus scans, making them a great tool for internal teams to get an instant view of service status as a whole. Once generated the page will be fully optimised to fit nicely on large office monitors.
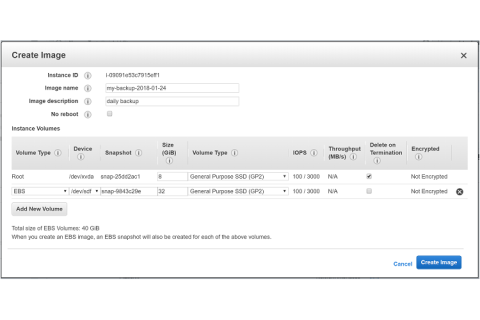
Daily AMI Images Are Key to Disaster Recoverability
As companies, big or small, move into the cloud, it’s becoming more and more important to ensure that data is protected. There are numerous options for data resilience, including (but not limited to), Amazon EBS and Amazon S3. What you choose to use depends on your business requirements. Amazon EBS volumes are supposed to be redundant within an availability zone, however they have been known to fail, both due to technical issues, and by human error.