Operations | Monitoring | ITSM | DevOps | Cloud
opsdemon
Latest posts
CMMC: What is it and why is it important to MSPs
The Cybersecurity Maturity Model Certification (CMMC) is a security framework implemented by the US Department of Defense (DoD) to improve protection of the defense industrial base. Like other security frameworks, the CMMC has a collection of controls for processes and practices with the goal of achieving a certain level of cybersecurity maturity.
CFEngine: The Agent Is In 5 - Running CFEngine On IoT
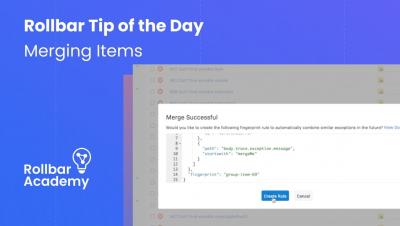
Rollbar Pro Tips: Merging Items
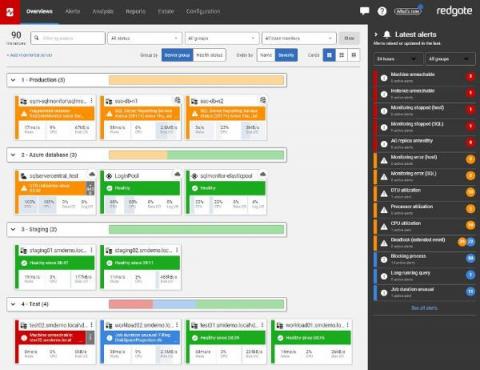
5 things to look for in a third-party monitoring tool
A closer look at how Puppet's new Compliance Enforcement Modules work
Since we launched Puppet Comply last year, we’ve been working hard to build out the solution’s capabilities so that we can provide our customers with more options in implementing a continuous compliance program, and become more proactive and efficient in how they manage compliance. A key activity in any strong continuous compliance program is remediation.
Observing container environments with Cloud Operations
Will Cloudflare R2 Win Customers from Amazon S3?
Cloudflare R2 vs Amazon S3
Facebook Outage: The Case for Configuration & Change Management
In the age of cloud, digital transformation, application modernization, and the mobile economy, the network is the lifeblood behind enabling excellent customer experiences. Network Operations (NetOps) and IT Operations (ITOps) teams are constantly aware that a disruption in core network systems performance can have a massive impact on their business.
Automating Cloud Security Posture Management Remediation
When we discuss cybersecurity and the threat of cyber attacks, many may conjure up the image of skillful hackers launching their attacks by way of undiscovered vulnerabilities or using cutting-edge technology. While this may be the case for some attacks, more often than not, vulnerabilities are revealed as a result of careless configuration and inattention to detail. Doors are left open and provide opportunities for attacks.