Operations | Monitoring | ITSM | DevOps | Cloud
Developer Sneak Peek | Slash commands for incident response
The Best Collaboration Tools for IT: MS Teams vs. Zoom vs. Slack
A key topic of conversation that comes up again and again with our customers is the challenge of collaboration in a remote work environment. Too many channels of communication or documentation are ineffective, and IT professionals are starting to feel fatigued by never feeling quite “in the know” with business decisions that are happening in real-time. When separated from colleagues, teams can feel distant and unmotivated or find it hard to stay focused.
Developer Sneak Peek | Searching files on Mattermost
How open source solutions help the U.S. Air Force accelerate software development and modernize collaboration
The pressure to ship quickly is greater than ever before. But for many organizations, including the U.S. Air Force, security and compliance concerns severely limit their ability to quickly adopt and integrate new technologies, putting teams at risk of being locked into approved vendors and missing out on critical innovations. In order break the cycle of slow-moving development, Platform One, the U.S.
Jira + Slack Integration: App Home - Demo Den October
Jira + Slack Integration: Personal Notifications- Demo Den October
Stuff Happens: How Slack and PagerDuty Work Together to Resolve Incidents Quickly
Like death and taxes, IT incidents are inevitable. Issues like server outages and broken code are common—and costly. A single hour of downtime costs businesses more than $300,000 on average, according to Gartner. That’s why a solid incident management strategy is a must for any organization. “People solve incidents, but we can’t do it alone,” says Ali Rayl, Slack’s vice president of customer experience.
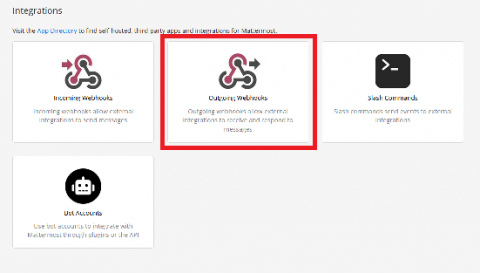
Mattermost integrations: Requesting data with slash commands
In the first two installments in this series, you learned you learned how to send alerts with incoming webhooks and request data with outgoing webhooks. In this article, you will learn how to set up a slash command. Slash commands are very similar to outgoing webhooks and even a little more powerful. To show their power in action, let’s find out how to use slash commands to request the temperature of a specific refrigerator.
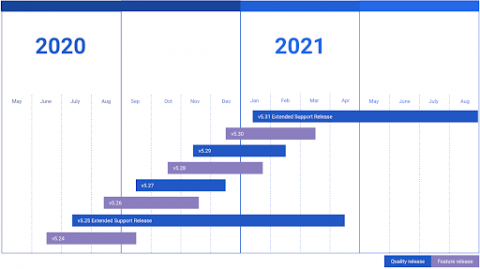
Support for ESR 5.19 is ending soon
As of October 15, 2020, Mattermost Extended Support Release (ESR) version 5.19 is no longer supported. If any of your servers are not on ESR 5.25 or later, upgrading immediately is required. With our simple upgrade steps, it takes only a few minutes. Extended Support Releases are releases that will receive backports for high severity or high-impact security fixes for the length of their lifecycle.