Operations | Monitoring | ITSM | DevOps | Cloud
Blog
Common C# exceptions and how to fix them
C# is a powerful programming language, but like all code, comes with its fair share of errors. Even experienced developers can find themselves stumped when they encounter a strange exception or error code. Fortunately, with the right knowledge and techniques, you can tackle any C# exception. In this article, we’ll discuss some of the most common exceptions in C# programming and how they can be fixed.
5 Essential Steps for Effective IT Asset Management
IT Asset Management is a critical aspect of any organization’s overall IT strategy. Many organizations, however, are not able to achieve their desired IT Asset Management goals due to the lack of a well-defined approach or the right solution. As a result, they often suffer from a high cost of ownership, low asset utilization, and increased security risks. This is why effective IT Asset Management is becoming increasingly important in the current economy.
Can Network Monitoring Identify Security Threats? Here's What to Know
By continuously monitoring network activity and assets, network monitoring plays a key role in identifying cybersecurity threats. The network monitoring process gathers important data that can be used in analytics or in conjunction with cybersecurity applications to rapidly identify and respond to threats.
Troubleshooting SD-WAN Performance Problems
Software-Defined Wide Area Network (SD-WAN) technology is revolutionizing the way organizations manage their network traffic. With its ability to decouple the data plane from the control plane, SD-WAN provides organizations with a more flexible, scalable, and cost-effective solution for managing their network traffic. However, understanding and troubleshooting SD-WAN performance can be a challenge, especially when it comes to the underlying physical network, or underlay.
Webinar Recap: Unlocking the Full Value of Telemetry Data
Growth of cloud computing and the preference for data-driven decision-making have led to a steady increase in investments in observability over the years. Telemetry data is recognized as not only critical for maintaining a company’s infrastructure, but also for aiding security and business teams in making informed decisions. However, just increasing investment in observability technology is not enough.
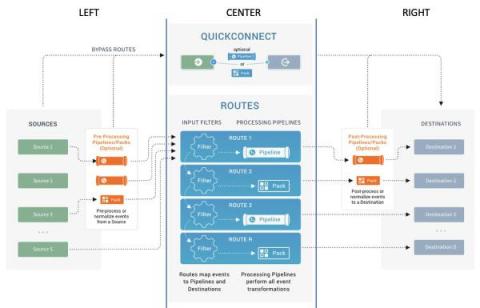
Left, Right, Center: A 3 Step Dance to Success with Building Data Pipelines
Remember the first time you were at a wedding, or a party and you learned about dances like The Electric Slide? You know, those dances with a clear structure and steps to follow, which were a huge help to someone who was slightly challenged on the dance floor, like me? All you had to do was learn a few simple steps, and you could hang with even the best dancers.
How to adopt distributed tracing without compromising data privacy
The age-old dilemma of privacy and security vs. productivity pops up for developers every time they consider introducing a new technology to their stack. The dilemma is often viewed as a trade off: on one hand, privacy and security measures can slow down how quickly new features can be rolled out; on the other hand, prioritizing productivity and business enablement over privacy and security can increase the risk of breaches to an organization.
Exploring cAdvisor for Common Use Cases
Container technologies have revolutionized the field of software development. By using containers, you can bundle together an application's source code with its libraries, dependencies, and configurations, ensuring that it runs predictably and reliably on different machines. But how can you be sure that your containers are running smoothly once deployed? That's where container monitoring tools like cAdvisor come in. Below, we'll go over what cAdvisor is and the different use cases for cAdvisor.