Operations | Monitoring | ITSM | DevOps | Cloud
Security
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Ransomware Cost Hospitals Nearly $21B Last Year. How Protected Are You?
Today, as computing power and wireless capabilities improve, organizations are increasingly leveraging Internet of Medical Things (IoMT) technologies, such as internet-connected blood pressure monitors, continuous glucose monitors and MRI scanners. These tools, with their ability to collect, analyze and transmit health data, improve efficiencies, lower care costs and drive better patient outcomes.
How to Test Salesforce Multi-Factor Authentication
Assuming you have correctly configured the user ids for MFA authentication in Salesforce, end-users should see the following screen when trying to login into the CRM application. The TOTP-based verification code is generated in third-party authenticator apps (Google or Microsoft) on your mobile device when you first scan the QR code or enter the key manually in the app. In this article, we’ll guide you through all the steps you need to set up our Salesforce MFA Web Sensor in your environment.
Is Remote Working a Cybersecurity Risk?
How to Get Started Securing Your Internal Software Supply Chain
Defining, building, and delivering a secure software supply chain is challenging for many organizations. Software builds utilize many open source components, and the vast landscape of cloud native developer and platform tools grows more extensive and more diverse every day. Developers, operators, and security teams must work together to ensure software is delivered swiftly and securely to meet business and customer desires.
SIGNL4 in IT Security
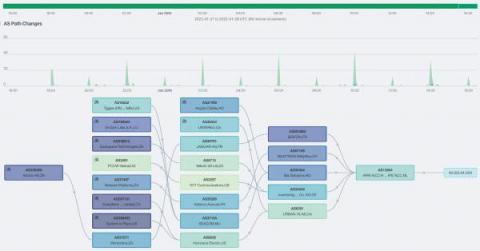
Introducing BGP monitoring from Kentik
Designed at the dawn of the commercial internet, the Border Gateway Protocol (BGP) is a policy-based routing protocol that has long been an established part of the internet infrastructure. Historically, BGP was primarily of interest to ISPs and hosting service providers whose revenue depends on delivering traffic.
CFEngine: The Agent Is In 10 - Event-Driven CFEngine
What a more holistic approach to cloud-native security and observability looks like
The rise of cloud native and containerization, along with the automation of the CI/CD pipeline, introduced fundamental changes to existing application development, deployment, and security paradigms. Because cloud native is so different from traditional architectures, both in how workloads are developed and how they need to be secured, there is a need to rethink our approach to security in these environments.