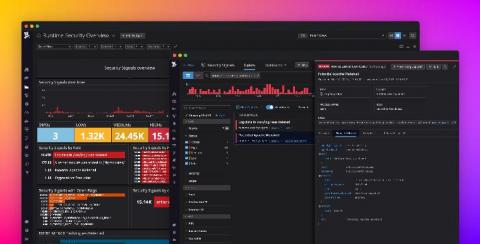
Event Log Management and Monitoring
Computer networks all around the world generate daily records of events occurring in their system. Some events are routine while others indicate potential security breaches or weak network health. Event log files consist of log information that can help organizations reduce their exposure against malware, intruders, damages and legal obligations.