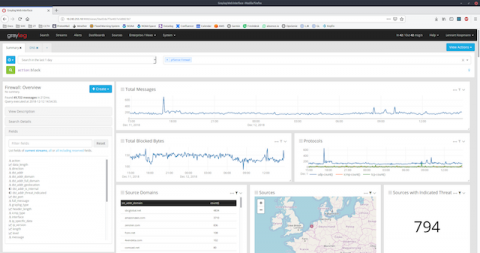
How to monitor networks for dummies. Here is what you need
Ok, so you own a company, now what? All right, then one of the million things to keep in mind, in addition to the plant that you are going to buy for your office, is learning how to monitor networks. Think that if your computerized network stops working properly (for any reason) and the data that normally flows through it does not, the company is not functional anymore, during the whole time the disaster lasts.