Operations | Monitoring | ITSM | DevOps | Cloud
Using OOP concepts to write high-performance Java code (2023)
Java Profiling Essentials: A Guide to different Java Profilers
When you are building an application with Java (or any other language, for that matter), there are certain aspects that you need to monitor constantly. This monitoring helps a long way in retaining your product's marketability and improving customer satisfaction.
First steps with the Apache Kafka Java client library
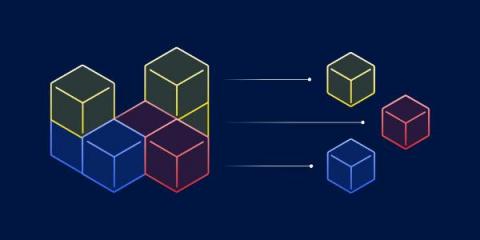
What are microservices? The pros, cons, and how they work
Microservices are a popular software design architecture that breaks apart monolithic systems. A microservice application is built as a collection of loosely coupled services. Each microservice is responsible for a single feature. They interact with each other via communication protocols such as HTTP.
Best Java GC Log Analyzers: Top Analysis Tools You Need to Know in 2023
Table of Contents When an application written for the Java Virtual Machine is running, it constantly creates new objects and puts them on the heap. Well, at least in the vast majority of the cases. Such objects can have a longer or shorter life, but at some point, they stopped being referenced from the code. Unlike languages like C/C++, we don’t have exact control over when the memory will be freed – freeing the memory is the garbage collector’s job.
How JMX Monitoring Works for Java Applications
The Java Management Extensions (JMX) framework is a Java technology that includes tools for managing and monitoring applications, system objects, and service-oriented networks. The JMX framework is designed to simplify the management of local and remote Java applications. The JMX framework introduces the concept of MBeans for real-time management of applications, whereby resources are represented by objects called MBeans (Managed Beans).
Java vs Python: Code examples and comparison
As two of the most popular and practical languages out there, should you choose Java or Python for your next project? Is one of these languages a clear-cut better option? The answer is a long one. According to GitHub’s annual Octoverse report, Python has now climbed to the second most popular language in usage, pushing Java down to third place.