Operations | Monitoring | ITSM | DevOps | Cloud
opsdemon
Latest posts
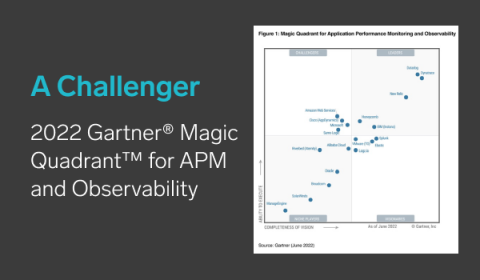
Sumo Logic - Challenging the status quo
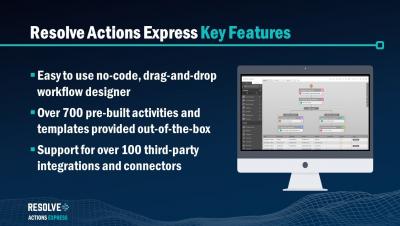
Resolve Actions Express SaaS - Getting Started
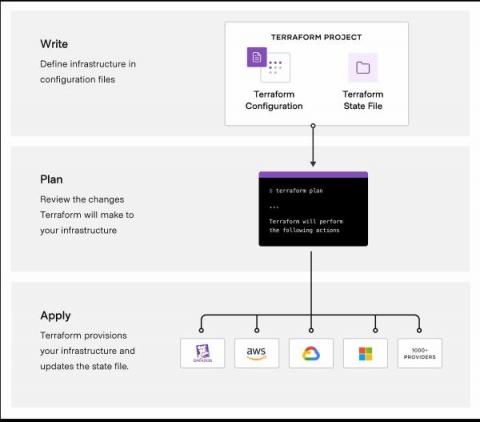
Introduction to Infrastructure as Code
Cloud infrastructure has been on the rise for the last decade. As it's adoption grows, so has the complexity of managing infrastructure, becoming more complex and more prone to user mistakes. This led to a new wave of tools in the Infrastructure as Code (IaC) space that aim to tackle this issue by treating your infrastructure as you would any other piece of software.
How to build a dashboard for any AWS CloudWatch data
Looking to keep an eye on logs and metrics from AWS or CloudWatch? There are several reasons you might want to build a CloudWatch dashboard somewhere outside of the CloudWatch console: Whatever the reason, we’ve put together a write-up to help you plug into CloudWatch to surface any logs or metrics in one place, for easy alerting and sharing, using the SquaredUp observability portal. You can get your own SquaredUp account, just head over to squaredup.io/get-started to sign-up for a free account.
Using Zero Trust Networking in Cloud Migrations
Moving workloads to the cloud has many benefits, and one that is often overlooked is the opportunity to modernize your network. In a traditional “perimeter-based” architecture, users and devices are authenticated and authorized on a device-by-device basis when connecting remotely via VPN.
Analyzing Log Data: Why It's Important
From production monitoring to security concerns, businesses need to analyze and review their logs on a daily basis to make sure their system is up to par. Here are the reasons why analyzing your log data is so important. If you landed here, chances are you probably know what logs are, but we’ll start off with a short explanation of what it is.
ManageEngine: Leveraging modern application monitoring to deliver enterprise-class digital experience
How to Start a Career in IT
Apache Pulsar vs. Apache Kafka 2022 Benchmark
You will have seen the Nastel Messaging Middleware Performance Benchmark Report comparing the performance of the commonly used messaging middleware platforms – IBM MQ, RabbitMQ, Apache Kafka, ActiveMQ Classic, ActiveMQ Artemis, TIBCO EMS, and Apache Pulsar. Nastel produced this using its CyBench performance benchmarking technology. StreamNative has also produced its own benchmark report focused on comparing Apache Pulsar vs. Apache Kafka using the Linux Foundation Open Messaging benchmark.