Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on IT Service Management, Service Desk and related technologies.
Ivanti Provides Critical Support for HoloLens2 with Windows Autopilot
We are excited to announce that Ivanti Neurons for MDM now fully supports all Windows Autopilot modes. This includes Autopilot pre-provisioned and self-deploying mode, in addition to the previously supported user driven mode. In particular, this self-deploying mode works seamlessly to automatedly enroll and configure HoloLens2 and Windows PC devices.
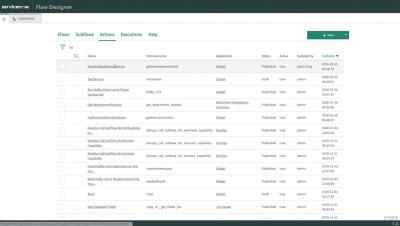
In the beginning: How ServiceNow was born
“It was November 5th, 2003. I knew that we had to start a company before I became 50, because a 50-year-old can't start a company. So, at 49—November 24th is my birthday—we started,” says Fred Luddy, ServiceNow founder. He began the company with a single laptop at a desk in his house. Although he founded the company alone, he couldn’t build it alone.
Announcing our brand evolution: Why the world works with ServiceNow
When Fred Luddy founded ServiceNow nearly 20 years ago, he envisioned a company built on two pillars: empathy and optimism. To this day, we approach every challenge with the optimism that we can solve it and the empathy to guide our way. These are amazing times we live in. Yep, I said it: amazing. Sure, we have big challenges, but it’s amazing that things are working, that the world is working. We’re playing a major role in that.
We were built on empathy
[ManageEngine Webinar] Understanding the role of AI in IT service management
Major New Features and Enhancements Now Available for Ivanti Workspace Control
We have just released Workspace Control 2022.1 (10.8.0.0), which contains three major new features and several bug fixes. We’ve also included several workflow improvements based on User Voice requests which were submitted via the Product Ideas page on the Ivanti Community.
What is depreciation of a fixed asset?
A fixed asset is a set of items intended to be used on a long-term basis for a company’s activity. In other words, they are assets that a company owns for a long time and that are not intended for resale. There are three main categories of fixed assets: tangible assets, intangible assets and financial assets.
Defining Your IT Security Perimeter
It wasn’t too long ago that a security system would be nothing more than a few walls, some cameras, and an inattentive security guard. That’s no longer the case In today’s digital landscape. Now organizations must invest in securing their assets from a growing number of cyberthreats. To start, they must first draw up the boundaries of their IT security perimeter.